There is a darker side to cybersecurity that’s frequently overlooked.
Just as you have an entire industry of people working to keep systems and networks safe from threats, commercial adversaries are working to exploit them. We’re not talking about red-teamers, who work to ethically hack companies from within. We’re referring to exploit markets that sell details of security vulnerabilities and the commercial spyware companies that use those exploits to help governments and hackers spy on their targets.
These for-profit surveillance companies flew under the radar for years, but have only recently gained notoriety. But now, they’re getting unwanted attention from U.S. lawmakers.
In this week’s Decrypted, we look at the technologies police use against the public.
THE BIG PICTURE
Secrecy over protest surveillance prompts call for transparency
Last week we looked at how the Justice Department granted the Drug Enforcement Administration new powers to covertly spy on protesters. But that leaves a big question: What kind of surveillance do federal agencies have, and what happens to people’s data once it is collected?
While some surveillance is noticeable — from overhead drones and police helicopters overhead — others are worried that law enforcement are using less than obvious technologies, like facial recognition and access to phone records, CNBC reports. Many police departments around the U.S. also use “stingray” devices that spoof cell towers to trick cell phones into turning over their call, message and location data.
Some agencies have also been shown to use legal but questionable practices like reverse-location warrants, which force companies like Google to turn over what information it has on any device located within a “geofence” of coordinates. Although rare, these reverse-location warrants have been known to ensnare innocent bystanders inadvertently caught up in these minidragnets of data.
Activists also fear that data collected from surveillance of protests could be shared among federal agencies and could be matched to social media profiles, credit reports and more with little oversight.
That’s prompted lawmakers to call for an end to secret surveillance and to seek out answers from a number of government agencies, from Homeland Security to the Department of Defense, and pursue police reform measures that would put new restrictions on how police can use facial recognition with their body cameras.
IBM stops selling facial recognition; Amazon, Microsoft pauses for now
It wasn’t just law enforcement facing the heat from critics this week. Several major tech companies that supplied surveillance technology to law enforcement pulled back from their government contracts.
Technology giant IBM was first to signal the end of its facial recognition business, calling for a “national dialogue” about the rules surrounding police use of face scanning and matching technology. A cynical view is that IBM’s facial recognition business didn’t make the company much money and was easy to ditch.
Amazon was next, saying it’ll put a one-year moratorium on selling to police, but paid only lip service in a hollow statement that the company refused to account for federal agencies’ use of its facial recognition tech.
Microsoft also said it will no longer sell to police until more federal regulation “grounded in human rights” is passed by Congress.
It’s surely a start, and a good example of corporations bowing to public pressure. But it’s difficult to escape the feeling that this should have happened sooner. Critics have for years complained that facial recognition technology is flawed, biased and disproportionately misidentifies people of color. The ACLU proved this when it found in 2018 that Amazon’s Rekognition facial recognition technology falsely matched two dozen members of Congress as criminals in a mugshot database.
MOVERS AND SHAKERS
It’s not just the government that spies. Commercial spyware is its own big business.
Reuters reported this week on New Delhi-based cyber firm BellTroX, which helped clients hack thousands of email accounts over the past decade. One of those firms was short seller Muddy Waters, a U.S.-based investment firm, whose chief executive Carson Block said he was “disappointed, but not surprised” to learn that his company had been targeted.
The private cyber-surveillance firm was unmasked by Citizen Lab, an internet watchdog attached to the Munk School at the University of Toronto. In a post, the lab’s researchers said BellTroX targeted journalists, hedge funds and government officials.
Citizen Lab also confirmed for the first time that it was BellTroX that targeted advocacy groups like Fight for the Future in 2017.
John Scott-Railton, a researcher at internet watchdog Citizen Lab said the company is “one of the largest spy-for-hire operations ever exposed.”
BellTroX is one of several companies that builds surveillance tools and hacking software for governments to use against their targets. Italian spyware maker Hacking Team and Israel’s NSO Group are both widely known for building hacking tools used by governments to hack into the phones and devices of their targets. But critics have denounced these spyware outfits for selling their tools to despotic regimes, like Saudi Arabia and the United Arab Emirates, which, by international standards, have atrocious records on human rights.
It’s why a new bill, passed this week by the Senate Intelligence Committee, could not come at a more crucial time. The bill, if passed by both the House and Senate, would compel the U.S. director of national intelligence to investigate the threats posed by commercial spyware against U.S. citizens, residents and personnel overseas.
In remarks to TechCrunch, Scott-Railton called commercial spyware a “problem at scale and is dangerous to U.S. national security.”
$ECURITY $TARTUPS
This week, hacker blogging site Hacker Noon raised $1 million from Coil, the site announced on Wednesday. The site is well known among the security researcher crowd for deep-dives into ethical hacking, cybersecurity, coding and more.
Meanwhile, Ethyca has raised $13.5 million in its latest fundraise. The startup allows organizations to identify its stores of sensitive data and applies permissions, auditing and reporting around it. It’s already secured a number of major contracts, including banks and tech companies — that as of yet don’t want to be named.
And, fraud detection platform NS8 has raked in a massive $123 million in its Series A round, led by Lightspeed and AXA, a round that will help the startup to accelerate its product development to meet demand and double down on hiring across sales, engineering, marketing and infrastructure.
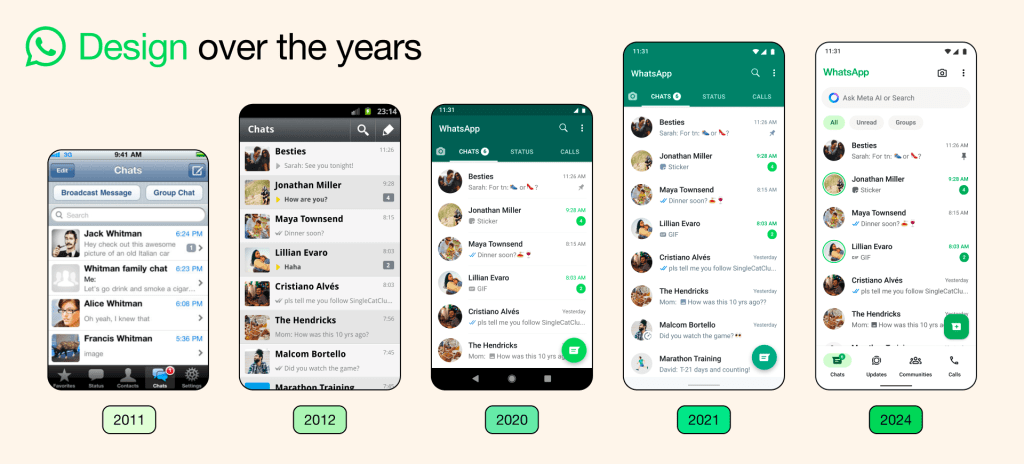
Send tips securely over Signal and WhatsApp to +1 646-755-8849.
























Comment