The U.K. Prime Minister David Cameron is in Washington DC this week, lobbying the U.S. President on the need for circumventing the strong encryption of Internet services.
This follows Cameron’s anti-encryption comments in the U.K., earlier this week, although government sources subsequently clarified that he does not intend to outlaw encryption per se — so much as seek to circumvent it by putting pressure on Internet companies to co-operate with governments by inserting backdoors into their security systems.
The why of all this anti-encryption rhetoric is the usual ‘national security’ excuse, with Cameron arguing that U.K. intelligence agencies must be able to access user data “in extremis” — to order to track down potential terrorists.
The series of recent terror attacks, and apparent attempted attacks, in Paris and Belgium are being used as justification for this push and of ‘evidence’ of imperative. Although, as the Snowden revelations have shown us, we know governments already have vast online surveillance dragnets — dragnets which failed to prevent the aforementioned terror attacks.
Indeed, in all likelihood, these vast non-targeted digital surveillance programs have made the intelligence services’ job of tracking down ‘a few interesting needles’ that much harder, given limited resources end up being stretched by more and more digital noise. But that hasn’t stopped Cameron seizing the opportunity to lobby for yet more online surveillance.
Oh, bravo.
The Independent's @DaveBrownToons on tomorrow's edition of #CharlieHebdohttp://t.co/1nTqFUUyUb pic.twitter.com/GSj78n388N
— Mike Cameron (@mikercameron) January 13, 2015
So far so ‘standard political post-terror-attack excuse for digital surveillance crackdown’ operating procedure.
But that’s not all. The U.K. P.M. is also today banging his political drum from Washington on the need for governments and companies to tighten their cyber security, in the wake of the Sony hack. And has traveled over the pond with an entourage of U.K. cyber security startups in tow — to ostensibly show off British startup talent in the online security space.
In an interview with the BBC, Cameron said U.S. and U.K. security agencies would be stepping up their co-operation in this area, and staging joint ‘cyber war games’ — forming so-called “cyber cells”, comprised of FBI and MI5 agents working together and sharing more data about potential online threats.
The co-operation arrangement has been dubbed “unprecedented” by Downing Street. The first exercise will apparently be a staged attack on the financial sector, and will take place later this year, according to the BBC.
“It’s not just about protecting companies, it’s about protecting people’s data, protecting people’s finances. These attacks can have real consequences to people’s prosperity,” Cameron told the BBC’s political editor, Nick Robinson, in a video interview.
Eh?
Now you might think these two political positions stand in opposition — i.e. on the one hand calling for a reduction in online security by requiring Internet companies perforate their own encryption, while on the other announcing measures apparently aimed at bolstering online security against hackers.
However the fuzziness of political techno rhetoric allows for a very large slice of fudge to be so served. Especially as much mainstream media either does not understand and/or is not interested in conveying technology discrepancies — meaning the politicians get to spin without being unspun. And they know that.
“We need to be able, in extremis, to interrupt the contacts between terrorists, whether they are using fixed phones, mobile phones or the Internet,” Cameron went on to say in the BBC interview, when asked what he wanted the U.S. President to do about making companies like Facebook and Google “co-operate with tracking down terrorists”.
“We both face the same challenge and we need to work with these big companies, we have good relationships with them, to make sure that we can keep people safe. So it’s a conversation to have with the President, which I’ll be doing today and tomorrow, and a conversation we both need to have with the companies concerned,” he added.
Robinson’s follow up question to these comments was not to ask Cameron to square the insecurity circle of coercing a perforation of corporate encryption on the one hand whilst warning of the dangers of corporate hacking threats on the other.
Rather he asked Cameron whether President Obama “calls you bro”.
Ummm…
Spooky action at a distance
Now there’s another theory that can in fact square Cameron’s crypto policy inconsistencies.
This theory suggests that talk of “cyber cells” and “cyber war games” is just a smokescreen to deflect the media and bamboozle the voting public while both U.K. and U.S. governments seek to do a back-room data-sharing deal that will subvert the security of Internet companies in the interests of expanding government agencies’ surveillance capabilities — helped along by respective national agendas apparently being aligned on this point.
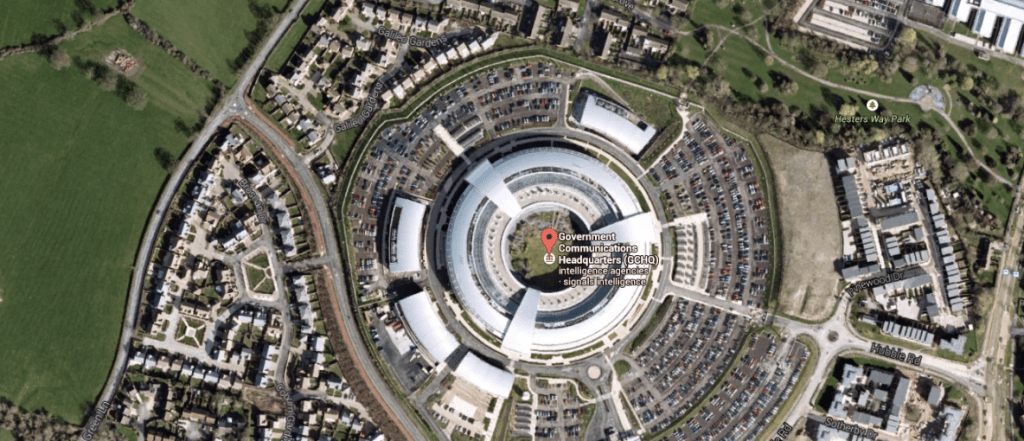
After all the FBI has been publicly critical of U.S. Internet companies tightening their encryption. As has the head of the U.K.’s GCHQ.
So joint U.S.-U.K. “cyber cells” might be a cloak for more than a few cyber war games. The whole closer cyber security co-operation initiative could also be a vehicle for passing encryption keys into perforated Internet services or a channel for more user data to flow.
As data privacy rights expert Caspar Bowden has noted, section 702 of the U.S. Foreign Intelligence and Security Act (FISA) already allows for spying on foreign nationals. And if the PM of the foreign body in question also wants the ability to spy on domestic citizens, well then, there’s no diplomatic blocker standing in the way — beyond the potential for some negative publicity for a government that asks another to subvert the crypto of all its own citizens.
Hence the combination of ‘keeping people safe’ counter-terrorism rhetoric being directed at encrypted Internet services by Cameron, coupled with him laying down a parallel smokescreen of joint U.K.-U.S. cyber security initiatives. Or that’s one reading of these otherwise conflicting Tory technology insecurity-security policy proposals.
This theory certainly makes Cameron’s incoherent technology policy pronouncements better add up. Which just leaves the question of who in the U.K. wants to vote for a Prime Minister who is asking a foreign government to spy on British citizens?
The Prime Minister is pleading with a foreign power to enable mass-surveillance of British people
1k UK followers => https://t.co/MfcNMsXkC9— Caspar Bowden (@CasparBowden) January 16, 2015
Oh and the other pressing question: how will U.S. Internet companies respond to a fresh round of political pressure over their use of strong encryption? Will they stand firm, a la Apple’s Tim Cook’s prior comments on iMessage encryption (“If the government laid a subpoena to get iMessages, we can’t provide it. It’s encrypted and we don’t have a key.”)?
Or will they be strong-armed into adding backdoors into mainstream services, thereby making them less secure against hackers, as well as accessible to spooks?
TechCrunch contacted Apple, Facebook and Google to ask for their response to Cameron’s latest anti-encryption comments and will update this post with any response. At the time of writing none of the companies had responded to a request for comment. Update: A Facebook spokesman declined to comment.





















Comment