computer security
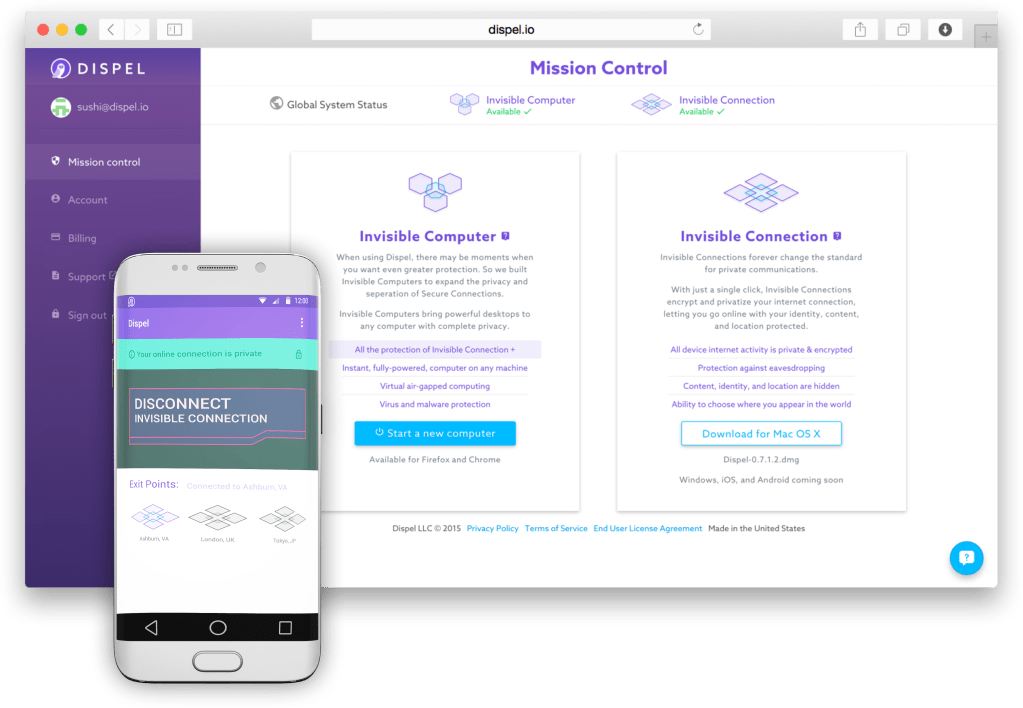
Dispel’s Privacy-As-A-Service Platform Keeps Your Internet Connection Secret And Safe
Most security services today give you virtual private networks that encrypt your connections (if you work for any sizable company, you probably use some kind of VPN client to log…
Solving The Persistent Security Threats For The Internet Of Things
The security problem — and, just as important, the security risks that consumers perceive in internet-connected devices — represents a real threat to the hundreds of millions of dollars companies…
Israeli startup Dojo-Labs has it eye on securing the connected smart home from the threat posed by, well, all the devices that comprise the connected smart home…
Encrypted webmail provider, ProtonMail, has been fighting a wave of DDoS attacks since November 3 that, by last Friday, had taken its service offline for more than 24 hours. At…
Senate Passes Cybersecurity Threat Sharing Bill That Tech Hates
In a crushing blow to the tech industry and privacy advocates, the Senate today passed the controversial Cybersecurity Information Sharing Act (CISA). The bill, which passed the Senate on a…
The White House Backs Down On Phone Encryption
In a victory for tech firms, the Obama administration will not force firms to breach the security of their products in order to provide information to law enforcement. The decision comes after…
Records Of 15 Million T-Mobile Customers Swept Up In Experian Hack
T-Mobile announced on Thursday the personal information of about 15 million customers was swept up in a hack on Experian, a vendor that processes the phone company’s credit applications. The…
Women Could Be The Solution To Fighting Cybersecurity Threats
Cybersecurity professionals are more in demand than ever before, but a new report finds the number of women in the field hasn’t grown. Women represent just 10 percent of the…
Why Cool Startups Are Losers In China
Here’s Hongyi Zhou’s advice to Chinese entrepreneurs: “Don’t try to be cool.” Zhou is CEO of Qihoo 360 (NYSE: QIHU), whose company’s core is the definition of uncool: anti-virus software. Yet…
All computer screens emit electromagnetic waves that can be intercepted by criminals who then use the data to reconstruct what is displayed. Research on the topic is largely classified. But…
An employee at an investment firm exposed clients’ personal data while using LimeWire. One of the clients was Supreme Court Justice Stephen Breyer. Much of his personal data was stolen!…