Clinkle is the hottest app around to have done mostly nothing. The stealth payments service, which has raised $30 million from big-name investors, has yet to publicly launch. But that doesn’t mean it can’t be hacked.
Today, a guest user posted a list of 33 usernames, user IDs, profile photos, and phone numbers to PasteBin. Based on the data provided, it seems as though these users are Clinkle employees who are testing the app.
Founder Lucas Duplan is on the list (yep, that’s his Clinkle profile pic, shown above), as well as former Netflix CFO and Clinkle COO Barry McCarthy. Former PayPal exec Mike Liberatore, now Clinkle CFO, is also listed.
The data was seemingly accessed through a private API that Clinkle has in place. Referred to by the hacker as “typeahead”, the API appears to be the basis of an autocomplete tool, allowing uses to type a single letter (like ‘A’) and find all usernames starting with that letter (like ‘Adam’ and ‘Andrew’). [Note: Twitter has a similar tool with the same name — it’s unclear if they’re one and the same.]
Clinkle seems to use this API in their own app (presumably so users can find friends when making a payment), which has allowed one hacker to search user names, leading to the associated user IDs and phone numbers.
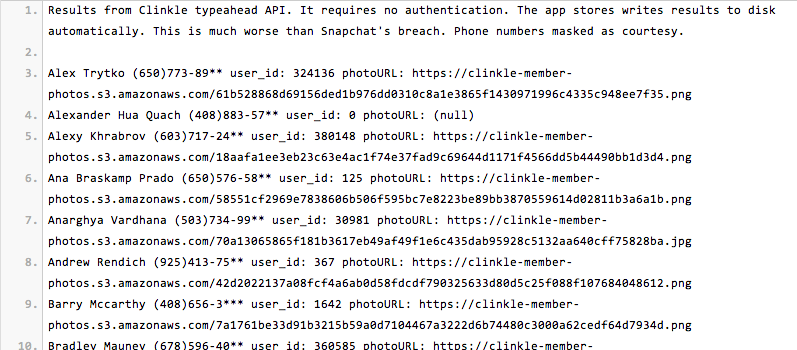
Here’s what the hacker had to say:
Results from Clinkle typeahead API. It requires no authentication. The app stores writes results to disk automatically. This is much worse than Snapchat’s breach. Phone numbers masked as courtesy.
In other words, whoever broke into the app didn’t need a userID to access Clinkle’s list of testers or their personal information, which seems to be saved on a Clinkle server.
But to be fair, Clinkle’s breach isn’t quite the same as Snapchat’s, considering the information of 4.6 million Snapchat users was released, as opposed a small group of employee testers.
Here’s Clinkle’s explanation for the breach:
You’re describing visibility that was purposefully built into the system as part of our preliminary user testing and was always intended to be turned off. As you can see from the list, we’ve been testing internally and registrations have been limited to Clinkle employees. We were using an open API, which has now been closed. That said, only names, phone numbers, photos, and Clinkle unique IDs were accessible.
Clinkle points to a Stanford student as the alleged hacker but that has yet to be confirmed.
Clinkle, rumored to launch later this year, currently has both an iOS app in iTunes and an Android app available in the Google Play store for those who wish to join the waiting list.
Based on the size of the app (52MB) and the unzipped files uncovered after downloading it, it seems like the full Clinkle app is out there, rather than a placeholder app built for wait list registrants.
Right now, the app has a waiting list wall, which “VIP” members can bypass once an administrator grants permission. This likely allows Clinkle to demo the app to investors and partners without having to go through some cumbersome download process.
During the process of fundraising, I’m sure that little trick came in handy. Not so much today, though.
The hack produced some interesting data about the team that works on Clinkle.
Founder Lucas Duplan is listed as the first user (User ID: 1), with a picture that very much resembles him holding cash money. The CFO, Barry McCarthy, is also listed with a legitimate profile photo, as is the Head Of Comms, who confirmed the validity of the images and the data.
The photos from Clinkle’s Team page, where 22 unidentified Clinkle employees are pictured alongside goofy pseudonyms, also seem to resemble people in the leaked profile photos. Finally, we can put faces to names.
So what are the implications?
Well, Clinkle hasn’t actually launched yet, so it’s very possible that the team hasn’t been focusing on security. However, security and trust should be top priorities for a payments company. Especially for a company so young.
Clinkle was founded by a group of more than a dozen Stanford students in 2011, and has stayed under the radar while key employees finish their degrees. The company was partially funded by Stanford professors before raising $25 million in a party round. Over 18 investors participated.
The WSJ, followed by every other news outlet, proclaimed this the biggest Stanford startup exodus in history. Clinkle was all the rage.
Seriously, Silicon Valley wouldn’t shut up about it.
In fall, however, two rounds of layoffs left many wondering if the Stanford-fueled payments startup was really the Messiah of trade. The company slashed around 30 employees, and then another 16.
Around the same time, screenshots and videos of the app in action were leaked, letting Clinkle’s cat out of the bag.
Rumors circulated that the company was going through leadership issues. That those promised equity weren’t getting it. That folks were overworked and underpaid. That there was no transparency about the product timeline, or the product itself. That 22-year-old Lucas Duplan was taking home a six-figure salary and mistreating employees.
Today, the same questions as before creep back into our consciousness.
What have they been doing with all that money this whole time? Posting profile photos that confirm our worst fears? Whether the breach was a result of intentional openness or unintentional laziness on the part of Clinkle is unclear, but the photo doesn’t lie.
