Earlier today, VPN service PureVPN was dealt a double blow by malicious hackers: a zero-day exploit; and the mailing of a subsequent, fake email alleging account closure and a data compromise. Uzair Gadit, the founder of the VPN tunneling service — which assigns new IP addresses to users’ connected devices, enabling them to access the Internet in firewalled countries or to use services that are usually geo-restricted at their current locations — tells us that there is no issue with PureVPN. “Our VPN service is functioning 100% fine and there is no interruption whatsoever,” he wrote in an email.
While the company is investigating the cause of the email, he continued, “we hereby confirm that, as we do not store any of our users’ credit card nor PayPal information in our on-site databases, there has been no compromise in our users’ personal billing information.”
The incident highlights how, while VPN tunneling services are often thought to be more secure routes for those worried about data compromises, they are not immune from attacks themselves. Perception of these services can be especially precarious considering that they have not been immune to crack-downs from restrictive governments in the past, such as in this incident in China from December 2012.
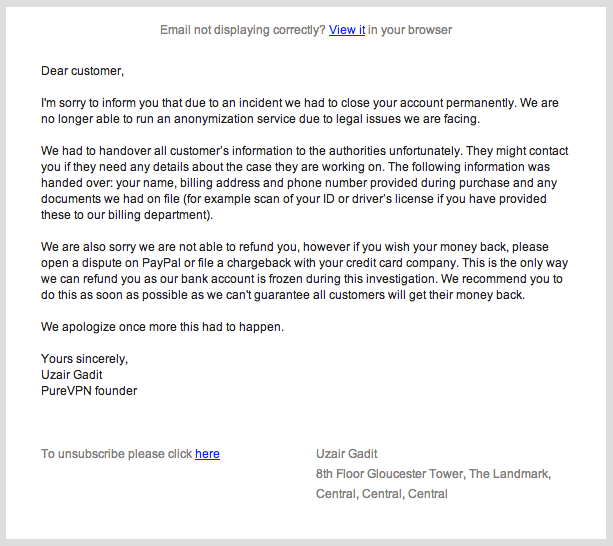
The PureVPN story was brought to TechCrunch’s attention by one of PureVPN’s customers who is based in China. Several hours ago, he sent over the following letter, noting that his account was closed, and that his billing information was being handed over to authorities, who might be contacting him in future:
A couple of hours later, his first email was followed up with another, which noted that the earlier email was fake:
“We are sending this note as a clarification,” the note said. “We are NOT closing down nor do we have outstanding legal issues of any sort. We have neither been contacted by any authorities nor do we store our user’s personal data to share with anyone.” The company says that while the VPN service remains fully operational “secure to the highest possible levels of encryption,” it has disabled the billing portal and client area while it is investigating the issue. The company is also posting updates on its blog.
We reached out to PureVPN about the two emails, and Gadit gave us a bit more information about what has happened.
He says that the email appears to have hit only a subset of all of PureVPN’s users, but the fact that our tipster was in China is not an indication that it’s only users in that country who may have been affected, with email IDs and names being the only data that appears to have been accessed.
“I confirm that the subset is NOT limited to Chinese users,” he says. “The motive is yet unclear.” Gadit says that PureVPN has hundreds of thousands of users from over 100 countries worldwide.
“There is NO issue with the service, there has been a fake email sent to some of our users talking about legal issues and other misleading stuff. Our VPN service is functioning 100% fine and there is no interruption whatsoever,” he wrote. “While we are investigating the cause of the email we hereby confirm that, as we do not store any of our users credit card nor PayPal information in our on-site databases, there has been no compromise in our users personal billing information. Similarly, service troubleshoot logs (connection attempts, users IPs and location) are safe and intact as we do not store such logs on site. Furthermore as we vouch for privacy, security and anonymity on the internet we do not store actual VPN service usage logs so there is no point in users’ privacy or anonymity being breached.”
He says that initial reports “suggest that we [were] hit with a zero day exploit, found in WHMCS.” This is a third-party CRM service used by PureVPN on its site. WHMCS had to release a security patch on October 3. At the time, it noted that “the vulnerability allows an attacker, who has valid login to the installed product, to craft a SQL Injection Attack via a specific URL query parameter against any product page that updates database information.”
So far, this, combined with PureVPN’s growth itself, are Gadit’s two reasons for the breach. “Clearly we are getting more and more popular crossing new heights too fast,” he wrote. “Such attacks are not unexpected with popular services these days. Such incidents only add to our resolve to emerge as more securer and faster privacy and security VPN service.”
He said that PureVPN is working on posting a complete report when it has completed its investigation.
In the meantime, if you’re a PureVPN user, be extra vigilant in looking out for any emails that ask you to reconfirm any billing details that you use for the service; they may be related to data collected during the zero-day exploit. That is in addition to being vigilant of the many other kinds of phishing emails you may get every day.
Update: In another update on the PureVPN blog on Monday, the company has confirmed that it was a zero-day exploit related to a vulnerability at WHMCS. The compromised data were email addresses and names for a subset of registered users, and “no billing information such as Credit Card or other sensitive personal information was compromised.” It also notes that after it publishes its final report it will be offering compensation for affected users.
