Technically speaking, the iPhone 5 is already jailbroken. You’re just not allowed to have it yet. The reason for this is because one of the bugs that contributes to a functional jailbreak is so good, that the hackers who discovered it would rather hang on to it while looking for another to replace it, instead of releasing it out into the wild where Apple could learn of the exploit, and patch it. Plus, iOS 6.1 is on the horizon, so they definitely don’t want to release the bug before then.
David Wang (@Planetbeing), one of the half a dozen hackers working on the jailbreak for the latest iPhone announced this news on Reddit not too long ago. “The fact is, I have an untethered iOS 6.0.2 JB running on my iPhone 5 right now,” he wrote.
“This vulnerability is nice because it lets us see what’s going on,” Wang tells me. “We need to be able to look at the code we’re trying to change – get a dump of it. Otherwise, we’re basically working on things in the dark.”
The worst case scenario here is that the hackers have to “burn” their current exploit – this great bug they have – in order to get a jailbreak into the hands of the public. They just don’t want to do that yet. Besides, the fact that there were four bugs discovered on the iPhone 5 at the time of that Reddit post was promising. That leaves hope that they’ll be able to find a few more. And so far, progress on that front looks good.
So will end users ever be able to jailbreak the iPhone 5, then? Yes, Wang says. This year? Well, he sure hopes so. At least before the next iPhone comes out.
The Days Of Yore
Finding exploits isn’t like building an app or website where every day, you would see progress. Instead, bug hunting is like panning for gold. And there might not be any gold to be found.
For those unfamiliar with jailbreaking, or why anyone would want to go to such efforts to have control over their phone, the activity originally became popular because it allowed users to add applications and features Apple didn’t approve. Users could turn their phones into a Wi-Fi hotspot, install custom themes, make the device’s settings and controls more accessible, override Apple’s default restrictions, and more. Some users even unlocked their phones to run on unapproved cellular networks.
In the old days, jailbreakers were more competitive, organizing themselves into “teams” like the iPhone Dev Team and the Chronic team. A few rogue developers even operated independently. Hackers competed against and surprised each other – and jailbreaking users, too – with their releases.
Now the jailbreaking vibe feels different. The individuals involved are generally working together and sharing knowledge when appropriate. The competitiveness has been dialed down. Each person works on their own piece. Everyone commits their piece to the same GitHub repo, and the code from there will then be turned into a user-facing jailbreaking tool.
And it’s not always the same people who work on each device’s jailbreak these days, Wang explains. It’s whoever has the time and energy. “Over time, the teams have broken down a bit,” he says. “The team structure doesn’t really work. It promotes rivalries and you can’t work with who you want. What we have now is better – we work with each other and share knowledge, but it’s kind of compartmentalized. Instead of sharing it with a whole team, we just share with an individual what we think they need to know.”
Call it a kinder and gentler hacking scene, perhaps.
This time around, work on the latest iPhone jailbreak has been delayed a bit, but not only because of the hardened iOS 6 operating system, but because of other demands on jailbreakers’ time. Like their day jobs. Wang has a full-time day job in a different field. Another of the iPhone 5’s hackers, @Pod2G, has been busy working on his own iOS app, for instance.
In Search Of Exploits
There are other things that slow down the process between finding the bugs and releasing the jailbreak tool: for example, finding the differences in the code between the different devices and testing procedures. When the jailbreak is done, it can also be challenging to find someone who’s savvy enough to test it, but who won’t leak it publicly. “It can take a couple of days, or a couple of weeks sometime,” says Wang.
It wasn’t always this hard.
In the past, jailbreakers were able to find bugs in the bootrom, the first significant code that runs on the iPhone, and they were in. They would have full control over that phone for as long as that device existed, no matter what version of iOS was running. But now, devs can’t even access the bootrom.
“The bootrom has been getting smaller and smaller, but we can’t even get a dump of it right now. Even if we get code controlling the entire phone running, like we do, we can’t see the bootrom. And if we can’t dump it, we can’t look for code and mistakes very easily,” Wang says. The reason for this is because today, when the iPhone 5 boots up fully, it now hides the bootrom. This has been the case since “Limera1n” took advantage of an undisclosed bootrom exploit on the iPhone 4 (and earlier devices), which Apple has since fixed.
Did Apple patch the bootrom only because of jailbreaking?
“It sure seems like it, because who else would care about reading the bootrom? You can’t really get a virus on your phone by reading the bootrom,” Wang says.
Today, with no bootrom bug available, hackers now need to find a lot more bugs to have a complete jailbreak solution for users. You need the code injection bug (which puts the code on the operating system), and something that increases the privilege level of that code so it can change things on the operating system on the phone. This bug can sometimes be the same as the code-injection bug.
Then you need a kernel injection bug, which gives you unrestricted access to the operating system and tells the kernel to stop checking for code signatures. And more recently, because of iOS 6, you need something to address kernel ASLR (address space layout randomization), which moves the kernel around in memory.
Apple doesn’t let the jailbreakers see where the kernel is in memory, to prevent exactly what they’re trying to do, says Wang. So you need to find a bug that can get around kernel ASLR, too, and it might be the same bug as the one that increases the privilege level of code or the kernel injection bug.
And then you need to find an untether bug so the jailbreak runs whenever and wherever the iPhone boots up.
Yes, that’s a lot of bugs.
A Very Brief History Of Jailbreaking
But to fully understand how iPhone jailbreaking has gotten more difficult over the years, you have to have a sense of history. You have to understand what’s it’s been like and how that has changed.
When the iPhone 3G came out, a jailbreak tool called PwnageTool emerged. It was based on a bootrom exploit that allowed the iPhone’s hackers to change out the software on the device. Basically, it’s like changing software out on a computer – for example, you have a computer that runs Windows, and you install Linux on it. In terms of jailbreaking an iPhone, this is pretty powerful access.
Later, when the iPhone 3GS came out, the key bug that allowed the developers this level of access was still there. Well, at least until sometime around halfway through the iPhone 3GS’s cycle when Apple decided to shut down manufacturing temporarily to address the problem. After production resumed, there was a new bootrom in place and the bug was gone.
“Certainly their motivation was that there was a bug and they wanted it to be fixed,” says Jay Freeman, who created the jailbreak “app store” known as Cydia – which users install after their phone is jailbroken. “But exactly why they considered that bug more important to fix than any other bug they’ve not fixed, I don’t really know…We’ve never had a better exploit than that.”
But that didn’t prevent the hackers from looking for other means to break into the iPhone’s code.
Immediately after Apple patched the one bootrom bug, jailbreakers were able to discover other bootrom bugs, but only those that could change the software temporarily. To continue the Windows analogy, this would be like booting up a computer from a CD, USB or floppy disk – you’re not really installing the software from scratch here.
On an iPhone, that means the jailbreaks could temporarily boot the phone up with a new kernel that doesn’t protect the phone’s software, mount the hard drive of the device and change the software on the iPhone to do different things – that is, run all those jailbreak apps that modify how the iPhone behaves.
But the kernel is still protected, because the bootrom was not modified or damaged, which means the next time the phone is booted, the jailbreak is undone. This is what’s called a “tethered” jailbreak, referring to the fact that the phone has to be plugged in to a computer when the jailbreak is performed and then each time the phone is rebooted. By the time the iPhone 4 came out, jailbreakers had to find a bug in a program running on the phone normally that they could use to access a bug in the kernel, which they could then use to modify the kernel. This would allow them to modify other software on the phone.
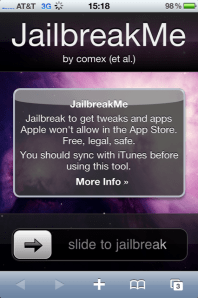
A famous example of this was the JailbreakMe website, which a jailbreaker known as @comex (aka Nicholas Allegra) discovered. This method used a bug in the web browser that could crash the browser and take control of it, in order to then get arbitrary code running in the kernel.
“Comex was just ludicrous,” Freeman says. “He found so many exploits in all sorts of things.”
(Comex was later hired by Apple, but we’ve heard he wasn’t working on anti-jailbreak measures while there. Wang tells us that users waiting for jailbreaks shouldn’t be significantly worried about Apple hiring from the jailbreaking community, either.)
The big next step was to make this jailbreak “untethered” – a device that can boot up directly to the jailbreak. This requires leaving some kind of code around that will cause the software to trip up upon boot, de-securing the device along the way. In the absence of a bootrom bug, like the one found on the iPhone 3G or 3GS, this was the best way for some time to achieve an untethered jailbreak.
A New iPhone, A New Search
Every time a new iPhone came out, the search for bugs begins anew. As was the case when the iPhone 4 came out.
On a memorable day – 10-10-10 – some members of the jailbreaking community were ready to release a tool called SHAtter, but before they did another hacker known as Geohot came out of nowhere with his Limera1n exploit for the iPhone 4 and iPad. Others, including @Pod2G, @Comex and @i0n1c, then worked to find untethers for that jailbreak.
Limera1n was important because, unlike the JailbreakMe webpage, which takes advantage of easily patchable software running on the phone (the browser), a bootrom exploit lasts for the entire life of that device.
“In order to upgrade the bootrom, you have to throw out your phone and get a new one…so [Apple] can’t ever upgrade Limera1n,” Freeman explains. “Limera1n is stuck on every device that ever shipped that had that bug.” The exception is if Apple goes out of its way to stop production, like it did with the 3GS, to fix the bug.
 The cat-and-mouse game between Apple and the jailbreaking community continued when the iPhone 4S came out. The exploit that Limera1n used was gone. That sent the hackers back to looking for what they call “userland” exploits – those bugs in the software (like the browser, as with JailbreakMe), which, when identified and used to develop a jailbreaking tool, are then likely to be patched by Apple in the very next firmware upgrade, e.g. iOS 4, iOS 5, iOS 6 and its minor releases. Hackers refer to this as “burning” the exploit, as it can never be used again after that point, since Apple always patches them.
The cat-and-mouse game between Apple and the jailbreaking community continued when the iPhone 4S came out. The exploit that Limera1n used was gone. That sent the hackers back to looking for what they call “userland” exploits – those bugs in the software (like the browser, as with JailbreakMe), which, when identified and used to develop a jailbreaking tool, are then likely to be patched by Apple in the very next firmware upgrade, e.g. iOS 4, iOS 5, iOS 6 and its minor releases. Hackers refer to this as “burning” the exploit, as it can never be used again after that point, since Apple always patches them.
Corona was the name of the userland exploit that allowed a jailbreak for the iPhone 4S, running iOS 5.0 and 5.01. Then Apple released iOS 5.1 and the bug was gone. So hackers created yet another jailbreaking tool, absinthe, that worked on iOS 5.1 and 5.1.1. Apple released iOS 6 and the bugs were gone again.
“iOS 6 has had significant security improvements. And iOS 6.1 also has even more improvements,” says Wang. “One of the things we’re having trouble with [on the iPhone 5] is the initial injection,” he explains.
Now remember that the iPhone 4 is not affected by all these iOS releases. Because Limera1n uses an unpatched bootrom exploit, it doesn’t matter what version of iOS runs on that device. It can be jailbroken. This, of course, raises the question: If bootrom exploits are that powerful, why don’t the hackers just look for them?
The answer is it’s not that simple.
“Finding bootrom exploits is more difficult only because there is much less software. We talk about this thing called an attack surface,” says Freeman. He likens it to the way a very large army wearing lots of battle armor probably has a break in it somewhere that you can poke a sword through. Meanwhile, a small army would be more likely to be protected fully. The only thing a bootrom does is verifies the other software, and it talks over USB. There’s not a lot of code in there.
Most of the bootrom bugs have been found in the USB setup code. Most of those bugs have been fixed.
However, in the iPhone 5, Apple added a Lightning connector, so there’s now a chance that there is a bug in the new bootrom – if hackers were to find a way to peek in there, which as noted above, they currently can’t.
So for now, it’s about finding non-bootrom bugs. And it’s been tougher to do so lately. There isn’t a good jailbreak for the iPhone 4 or iPod 4, only a tethered one. There’s no publicly available jailbreak for iOS 6 on the iPhone 4S or iPhone 5.
Like Dealing With Magicians
It’s hard to always know what’s going on with the current jailbreak. When jailbreak developers and other hackers are teasing their progress on Twitter, they’re sometimes showing off some of those so-called userland bugs in action. Maybe they show Cydia, Freeman’s app store for the jailbreaking community, running on their device. But Freeman clarifies that these teases are often only partial jailbreaks – Cydia is installed, but the apps that let you have all the fun wouldn’t necessarily work. Other times, they’ve used Apple’s own developer tools, which allow Apple’s paying developers to install their own code on the phone. Seeing a device running Cydia, in other words, is not proof that a jailbreak for you, the user, is ready.
Sometimes, however, it is a hint at progress.
“It’s a little bit like dealing with magicians. You might know how somebody’s trick works, but it’s their trick,” says Freeman. “A lot of the hacking community has that same kind of vibe to it. Somebody has managed to figure out how to do something weird.” Instead of hacking your brain, as magicians do, they’ve hacked a phone, he says.
For example, the recent demonstrations by @chpwn and @phoenixdev were totally legitimate, but they did not have kernel patches and so were not “complete” enough to do most of the things that people expect a jailbroken device to do, says Freeman. “They were only half-jailbroken.”
The trick is knowing which jailbreak developers you can trust. While it’s possible there’s still a chance someone will come out of nowhere, like Comex did back in the day, it’s a better bet that future jailbreaks come from those who have been consistently working on jailbreaking Apple’s devices over the years.
If They Jailbreak It, Will Users Come?
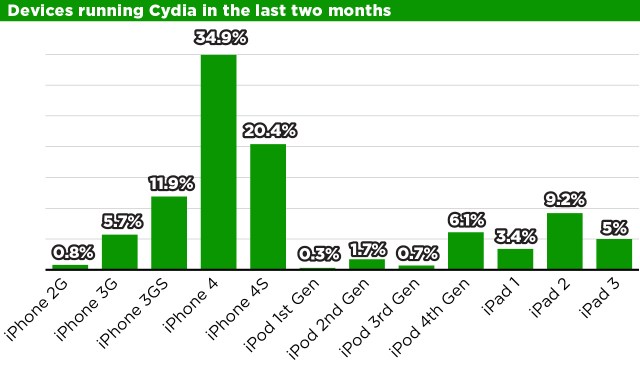
But when the iPhone 5 jailbreak arrives, the bigger question may be whether it will again draw a significant number of users, as it had in years past. Freeman says that, based on data over the past two months, he has seen 22,780,029 devices running Cydia, to give you an idea of scale. But of course, this includes more than iPhones – it counts iPads and the iPod touch, as well. Plenty of users still have iPhone 4’s and 4S’s too, it should be noted.
Freeman says that in between the releases of jailbreaking tools, Cydia installs begins trending downwards, but when the next big jailbreak tool is goes out, the number of Cydia installs has always been more than the time before.
 “Every time we release jailbreak, we get a massive spike of renewed interest, during which time people furiously are upgrading, jailbreaking, browsing packages, and purchasing products,” Freeman says. “They are seriously active users; that spike is so large that the rate it falls over time swamps the rate of organic user accumulation, so the overall usage of jailbreaking is always going down.”
“Every time we release jailbreak, we get a massive spike of renewed interest, during which time people furiously are upgrading, jailbreaking, browsing packages, and purchasing products,” Freeman says. “They are seriously active users; that spike is so large that the rate it falls over time swamps the rate of organic user accumulation, so the overall usage of jailbreaking is always going down.”
Is The Time For Jailbreaking Over?
In these quiet periods, though, there’s room for doubt that anyone still wants to jailbreak their phone. After all, Apple has addressed a lot of the things jailbreakers were after: It now has a drop-down notifications window and lets you put a wallpaper on the lock screen, for example. FaceTime on AT&T works over 3G/4G now. The iPhone is coming to T-Mobile, so you won’t need to jailbreak, then use an unlocking tool to make the phone compatible on T-Mobile. You can even buy unlocked phones, and it’s easier to just pay for a Wi-Fi hotspot feature with your carrier than it is to jailbreak and install software to make one work.
And for naughtier users, the app piracy community Hackulous recently shut down, citing lack of user interest. “Our community has become stagnant,” its creators said.
Freeman doesn’t think the lack of a jailbreak for the iPhone 5 is the main reason for the recent disinterest. It’s the type of jailbreaks that have been available lately for the most popular devices.
“We have to look at iOS 6: we don’t have a ‘good’ jailbreak for iOS 6 on the iPhone 4 or iPod 4 (as it is tethered),” he says, “and we have no jailbreak for iOS 6 on any of the newer devices, including last year’s iPhone 4S.”
“We all think that the popularity of jailbreaks is going down because of all the improvements Apple has made, but it seems to be still pretty popular,” Wang notes, however. And the fact that his Reddit post blew up, is also promising.
He admits that those working on the jailbreaks may not communicate with users as often as they did in the past.
“I don’t maybe make as much of an effort as maybe I should, because in a way, it’s always kind of hopeless. There’s always people who don’t read, or choose to misinterpret what you say,” he says. “It’s so difficult to not be misunderstood. Sometimes you don’t even want to bother trying.”
But he does still try. Just this weekend, for example, Wang and fellow jailbreaker @Pod2G tweeted that they made progress in finding more bugs, which hopefully brings us closer to a public jailbreak.
The iPhone 5 jailbreak, however it comes to be, could breathe new life into the jailbreaking scene and into a community which even grew large enough to have its own convention. And it will also answer the question as to whether all those millions of users are still interested in taking the plunge and jailbreaking their phones, or whether they’ve become comfortable enough with the status quo in these many months without a usable, untethered jailbreak on hand.
Wang, of course, and others like him, never had to take time off from using a jailbroken device. “My iPhone is always jailbroken,” he said.
And maybe one day soon, your iPhone can be jailbroken again, too.
Image credits: @chpwn Twitter; sbssettings/cydia – CultofMac.com; limera1n – Slashgear