A security flaw in one of AT&T’s customer-identification scripts has allowed a group of 4chan hackers to extract as many as 114,000 email addresses of iPad owners, according to Gawker. AT&T has apologized and explained the flaw and data leaked. Essentially, a bit of open information (the SIM card’s ICC-ID) was tied to a piece of private information (the iPad owner’s email address) so that on encountering certain AT&T fields, it would automatically fill in the field with the appropriate email. Think the “Remember this password?” notifications that pop up when you register for a site, but a little more low-level.
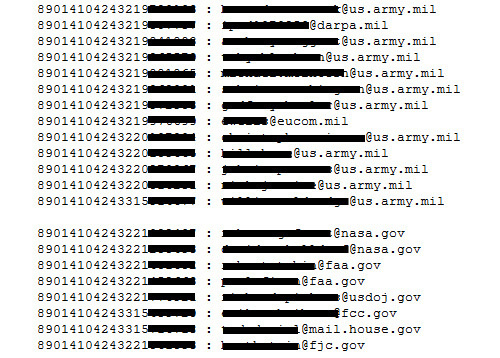
The hackers, a group known as Goatse Security (I’ll let you work out the reasoning for the name yourself), organized a brute-force attack in which they pummeled a public AT&T script with semirandom ICC-ID numbers, which would return nothing if invalid but an email address if valid. A few hours later, they had the ICC-IDs and email addresses of everyone from Michael Bloomberg and Diane Sawyer to a Mr. Eldredge, who commands a fleet of B-1 bombers.
As is occasionally the case with grey-hat hacker actions like this, the hack seems to have been executed first and AT&T notified shortly afterward — though not before an unknown number of third parties had access to the script. AT&T closed the hole immediately (it was as simple as turning off the script), and apologized as follows:
AT&T was informed by a business customer on Monday of the potential exposure of their iPad ICC IDS. The only information that can be derived from the ICC IDS is the e-mail address attached to that device.
This issue was escalated to the highest levels of the company and was corrected by Tuesday; and we have essentially turned off the feature that provided the e-mail addresses.
The person or group who discovered this gap did not contact AT&T.
We are continuing to investigate and will inform all customers whose e-mail addresses and ICC IDS may have been obtained.
We take customer privacy very seriously and while we have fixed this problem, we apologize to our customers who were impacted.
Impacted. Like wisdom teeth. Why not “affected?” Anyway, I notice they say they were not contacted by the group but by some business customer. The timing isn’t clear from the Gawker article, but I wonder if there’s a little more to this than anyone cares to admit. Groups like Goatse often warn their targets beforehand, but it seems like one or the other would have mentioned that if it happened. You’d think a company as exposed as AT&T would have bells on its scripts that would ring if suddenly requests increased by 1000%, but practices like that are perhaps too much to be expected.
Did Gawker really print out the whole list? I hope not
As AT&T mentioned, the only information the breach could provide was an email address. Some of the high-level ones (CEOs and such) noted as leaked were likely already public, like all of ours here. But let’s not forget that of the 114,000, 113,950 weren’t high-level media executives. A vast list of early-adopting, 3G-using, iPad owners is be a valuable thing (to say nothing of a guy with a bunch of bombers), and I have no doubt that someone more unscrupulous than Goatse Security will be passing that list on to interested buyers. Nothing else, though, if we are to believe those in the know — and they have no reason to deceive us in this case.
What will the outcome be? A bit of extra spam for those involved is likely the worst that will happen. The ICC-ID isn’t used in any secure access protocols.
And who’s to blame? AT&T, AT&T, and AT&T. It’s arguable that Apple (who gets it in Gawker’s headline) should have something in place to prevent something akin to a unique device ID from being used as authorization, but that’s stretching it. The script, which accepted any properly-formed input and spat out private information, was the issue from start to finish and it is AT&T who created and served that script. Apple isn’t safe from the fallout, though: many who hear of this in the papers tomorrow will choose not to separate the device maker from the service provider. The worst part is there’s not much they can do but say hey, we’re committed to security and point their finger at AT&T.
What can you do? If you are an iPad 3G customer, call customer service and demand reasonable satisfaction. A few months of free unlimited 3G would probably go over nicely, don’t you think? And, of course, there is their always-personable CEO as well. I’m sure he’d like to hear from you (limit one email per customer, please).
The rest of the story (and continuing updates) can be found at Gawker.
Update: Goatse Security, in an interview, has defended their actions as legal and ethical, and for the most part, I agree. They tipped off a third party (which explains the statement discrepancy I noted above) about the exploit after they had executed their script.