
SCRANTON, PENNSYLVANIA – SEPTEMBER 11: A political poster favoring U.S. presidential candidate former Vice President Joe Biden and Senator Kamala Harris is placed on a front lawn September 11, 2020 in Scranton, Pennsylvania. (Photo by Robert Nickelsberg/Getty Images)
A privacy bug in Democratic presidential candidate Joe Biden’s official campaign app allowed anyone to look up sensitive voter information on millions of Americans, a security researcher has found.
The campaign app, Vote Joe, allows Biden supporters to encourage friends and family members to vote in the upcoming U.S. presidential election by uploading their phone’s contact lists to see if their friends and family members are registered to vote. The app uploads and matches the user’s contacts with voter data supplied from TargetSmart, a political marketing firm that claims to have files on more than 191 million Americans.
When a match is found, the app displays the voter’s name, age and birthday, and which recent election they voted in. This, the app says, helps users “find people you know and encourage them to get involved.”
While much of this data can already be public, the bug made it easy for anyone to access any voter’s information by using the app.
The App Analyst, a mobile expert who detailed his findings on his eponymous blog, found that he could trick the app into pulling in anyone’s information by creating a contact on his phone with the voter’s name.
Worse, he told TechCrunch, the app pulls in a lot more data than it actually displays. By intercepting the data that flows in and out of the device, he saw far more detailed and private information, including the voter’s home address, date of birth, gender, ethnicity and political party affiliation, such as Republican or Democrat.
The Biden campaign fixed the bug and pushed out an app update on Friday.
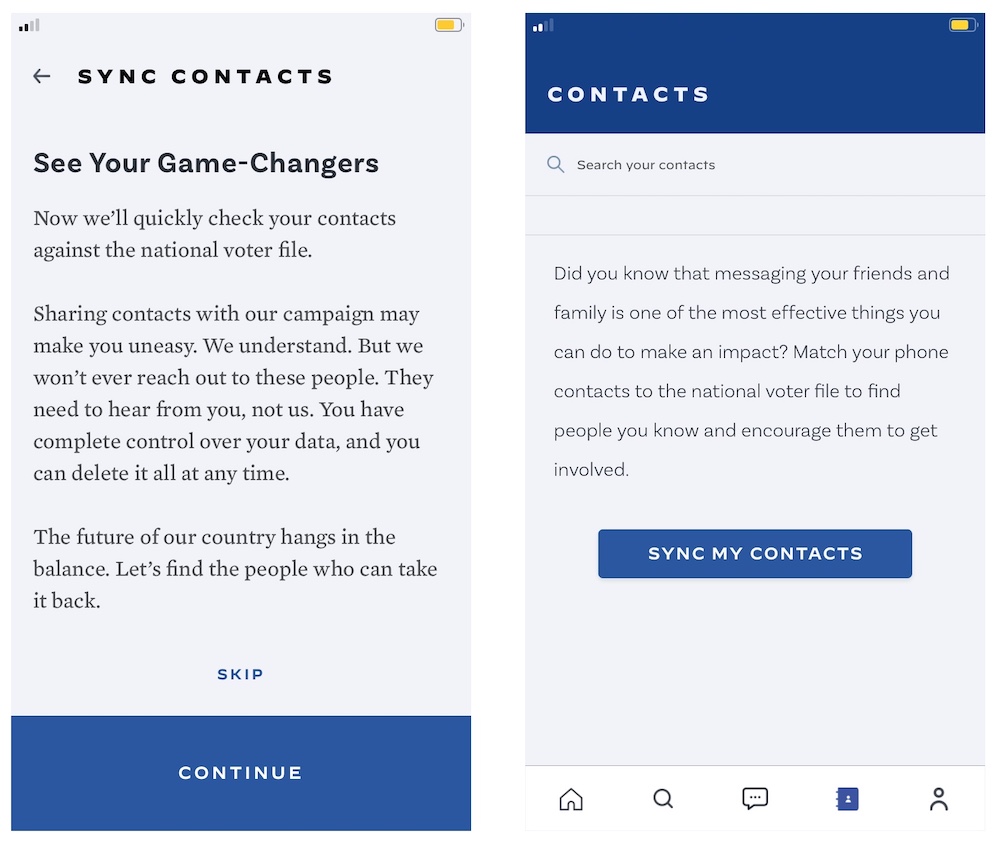
A screenshot of Joe Biden’s official campaign app, which uploads and matches a user’s contacts with their existing voter file. But a bug allowed anyone to pull in any voter’s information. (Image: TechCrunch)
“We were made aware about how our third-party app developer was providing additional fields of information from commercially available data that was not needed,” Matt Hill, a spokesperson for the Biden campaign, told TechCrunch. “We worked with our vendor quickly to fix the issue and remove the information. We are committed to protecting the privacy of our staff, volunteers and supporters will always work with our vendors to do so.”
After publication, Hill disputed the researcher’s findings and and that the app returned gender, ethnicities, or home addresses
Mike Czin, a spokesperson for TargetSmart said: “Due to a coding error by a progressive app developer, a limited amount of publicly or commercially available data was accessible to other users. The issue was quickly identified and fixed.”
A spokesperson for TargetSmart said a “limited amount of publicly or commercially available data” was accessible to other users.
READ MORE
It’s not uncommon for political campaigns to trade and share large amounts of voter information, called voter files, which includes basic information like a voter’s name, often their home address and contact information and which political parties they are registered with. Voter files can differ wildly state to state.
Though a lot of this data can be publicly available, political firms also try to enrich their databases with additional data from other sources to help political campaigns identify and target key swing voters.
But several security lapses involving these vast banks of data have questioned whether political firms can keep this data safe.
It’s not the first time TargetSmart data has been embroiled in a security lapse. In 2017, a voter file compiled by TargetSmart on close to 600,000 voters in Alaska was left on an exposed server without a password.
In 2018, TechCrunch reported that close to 15 million records on Texas voters were found on an exposed and unsecured server, just months ahead of the U.S. midterm elections.
Last week Microsoft warned that hackers backed by Russia, China and Iran are targeting both the 2020 presidential campaigns but also their political advisors. Reuters reported that one of those firms, Washington, DC-based SKDKnickerbocker, a political consultant to the Biden campaign, was targeted by Russian intelligence but that there was “no breach.”
Updated with Hill remarks.
