A thirty-strong group of security researchers have co-signed an open letter calling for the Guardian to retract a story it published last week that had claimed mobile messaging app WhatsApp contains a “backdoor”.
“Unfortunately, your story was the equivalent of putting “VACCINES KILL PEOPLE” in a blaring headline over a poorly contextualized piece,” writes academic Zeynep Tufekci, who organized the open letter.
The letter goes on to argue the Guardian’s assertions are “very concretely endangering people”.
“My alarm is from observing what’s actually been happening since the publication of this story and years of experience in these areas,” writes Tufekci, adding: “You never should have reported on such a crucial issue without interviewing a wide range of experts.”
She has also made her views on the Guardian’s report and the potential consequences for at risk users of WhatsApp amply clear on Twitter…
WhatsApp also robustly rejected the Guardian’s claims of a “backdoor” in its platform as false when we contacted them last week for comment, telling us: “WhatsApp does not give governments a “backdoor” into its systems and would fight any government request to create a backdoor. The design decision referenced in the Guardian story prevents millions of messages from being lost, and WhatsApp offers people security notifications to alert them to potential security risks.”
We also contacted the author of the Signal Protocol, Moxie Marlinspike — who last year worked with WhatsApp to roll out the end-to-end encryption in a landmark move for security by expanding access to the robust and respected crypto across such a mainstream messaging platform.
In his email to TechCrunch Marlinspike dubbed the Guardian story “supremely inaccurate”.
The newspaper’s report is based on research by independent security researcher Tobias Boelter, who in April 2016 published details of what he described as a “retransmission vulnerability” in the way WhatsApp handles key exchanges when a message has not been delivered.
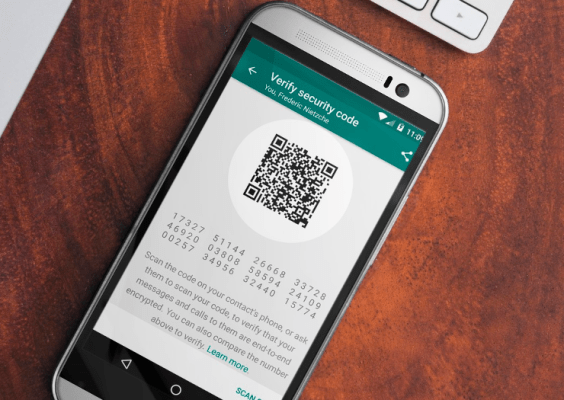
Users of the WhatsApp platform do have an option to turn on notifications for when a key has been changed — although this warning will only be delivered after the message itself has been sent. Hence Boelter arguing there’s a security risk for WhatsApp users.
Boelter said he flagged the issue to WhatsApp’s parent company Facebook at the time he wrote about it but was told it was “expected behaviour”.
Last week WhatsApp asserted the key retransmission process is a design decision — intended to minimize the risk of messages being lost in transit when, for example, someone gets a new phone or swaps out their SIM.
And the group of security researchers co-signing Tufekci’s letter to the Guardian evidently concur it’s a feature not a bug — with co-signatories including cryptographer Bruce Schneier, The Tor Project’s Isis Lovecruft, security researcher Thaddeus T. ‘Grugq’, Mozilla’s Katherine McKinley, the Open Crypto Audit Project’s Kenneth White, and security researcher and author Jonathan Zdiarski.
“WhatsApp’s behavior around key exchange for unread when phone or SIM cards are changed is an acceptable trade-off if the priority is message reliability,” writes Tufekci, going on to argue that the intercept vulnerability in how WhatsApp handles key retransmission is “a small and unlikely threat”.
“People do not have a free choice in what apps to use; they gravitate towards ones with the largest user base (the ones the people they want to connect to are using) and to ones that are seamless to use. Causing unnecessary and unwarranted concern about WhatsApp is likely to make many users give up on the idea of using secure apps altogether. Again, think of causing alarmist doubts over vaccines in general because of a very rare threat of side effects to a few,” she continues.
“Individually targeted attacks by powerful adversaries willing to put effort into compromising a single person are a different kind of threat. If that is the threat model in mind, than merely recommending Signal is irresponsible. Your reckless, uncontextualized piece posits a mythical Snowden-type character, with a powerful, massively resourced adversary, for whom WhatsApp would not be a good choice. From that it concludes that WhatsApp is unsafe for a billion people for whom it is, at the moment, among the best options for secure communication.”
We’ve reached out to the Guardian’s London technology editor, Jonathan Haynes, to ask whether the newspaper will be retracting the story and issuing an apology, and will update this story with any response. The author of the original story does not appear to be a staff writer at the newspaper.
Update: A Guardian News & Media spokesperson has now provided TechCrunch with the following statement:
We ran a series of articles highlighting and discussing a verified vulnerability in WhatsApp and its potential implications. WhatsApp was approached prior to publication and we included its response in the story, as well as a follow up comment which was received post-publication. While we stand by our reporting we have amended the article’s use of the term ‘backdoor’ in line with the response and footnoted the articles to acknowledge this. We are aware of Zeynep Tufekci’s open letter and have offered her the chance to write a response for the Guardian. This offer remains open and we continue to welcome debate.
Prior to the publication of Tufekci’s open letter the newspaper had already edited the story — changing the headline to replace the word “backdoor” with “vulnerability”.
An editorial note at the bottom of the article regarding that change reads: “This article was amended following a further statement from WhatsApp, which said that it did not give governments a “backdoor” into its systems.”
But despite making some edits to the original report, the paper has published follow-up articles that continue to suggest users switch from WhatsApp to Signal. It has also not issued a formal correction.
While Tufekci has said on Twitter that she “loves Signal“, she argues in the letter it is not an appropriate equivalent alternative for the mainstream WhatsApp user-base because it is a less reliable option, given Signal actively blocks message delivery after a new key has been generated (rather than just offering an opt-in warning that a key change has happened).
She also suggests use of Signal “may not be advisable in some settings, because it marks you as an activist”, arguing: “There are many threat models under which WhatsApp is the safest option, and there are reports of people around the world being jailed merely for having installed an encryption app.”
“It’s fine to recommend Signal and to broaden its user base. It’s not fine to fearmonger and scare people away from WhatsApp… because of a minor and defensible difference in the kind of warnings it gives and the blocking behavior of a few undelivered messages when someone changes phones or SIM cards,” she adds.
Tufekci also argues that too many user warnings can, counterintuitively, be bad for security — by encouraging users to ignore them. Another reason she asserts WhatsApp’s more light-touch approach is valuable for safeguarding the communications of a mainstream user-base. (The platform had more than one billion global monthly active users, at the last count.)
Marlinspike makes a similar point in a blog post he wrote last week also defending WhatsApp’s design decision around key changes — arguing that “given the size and scope of WhatsApp’s user base” a non-blocking notification is the “appropriate” choice.
“The fact that WhatsApp handles key changes is not a “backdoor,” it is how cryptography works. Any attempt to intercept messages in transmit by the server is detectable by the sender, just like with Signal, PGP, or any other end-to-end encrypted communication system,” he wrote, adding: “Even if others disagree about the details of the UX, under no circumstances is it reasonable to call this a “backdoor,” as key changes are immediately detected by the sender and can be verified.”
The Electronic Frontier Foundation has also characterized what WhatsApp is doing with key changes as a “trade off“, and while it agrees with Boelter there is a vulnerability the organization asserts that to describe it as a backdoor is “inaccurate to the point of irresponsibility”.