Tor has been the go-to for anonymous communication online for years now — and that has made it one of the juiciest targets possible to the likes of the NSA and FBI. A new anonymizing protocol from MIT may prove more resilient against such determined and deep-pocketed attackers.
The potential problem with Tor is that if an adversary gets enough nodes on the network, they can work together to track the progress of packets. They might not be able to tell exactly what is being sent, but they can put together a breadcrumb trail tying a user to traffic coming out of an exit node — at least, that’s the theory.
A team of researchers led by MIT grad student Albert Kwon (with help from EPFL) aims to leapfrog Tor’s anonymizing technique with a brand new platform called Riffle.
“Tor aims to provide the lowest latency possible, which opens it up to certain attacks,” wrote Kwon in an email to TechCrunch. “Riffle aims to provide as much traffic analysis resistance as possible.”
In addition to wrapping messages in multiple layers of encryption (the eponymous technique of Tor, “The Onion Router”), Riffle adds two extra measures meant to baffle would-be attackers.
First, servers switch up the order in which received messages are passed on to the next node, preventing anyone scrutinizing incoming and outgoing traffic from tracking packets using metadata.
Then comes a two-part measure to prevent a malicious server from simply replacing real messages with dummies and tracking a single target one. Messages are sent from the user to all servers, not just one — and outgoing messages must be signed with an independently verifiable mathematical proof that they are the ones the server received. This way, any server tampering with messages will be spotted at once.
Both these techniques — mixnets and dining-cryptographer networks, respectively — have existed independently for years, but serious drawbacks prevented either of them from being adopted, let alone both in the same system. DCNs didn’t scale well, requiring a lot of bandwidth, and the proofs needed for mixnets were too computationally expensive to keep latency low.
The key advance made by Kwon and his team is was implementing both in such a way that those weaknesses are avoided. You can read about the technical details in the paper itself (PDF) but the gist is that it uses a mix of public-key and symmetric cryptography, not dissimilar to how it works on the web.
With this change, the resulting network is not only resistant to both active and passive attacks, but scales well and doesn’t use too much processing time. File sharing with hundreds of users could theoretically reach 100 KB/s, according to the researchers’ estimates, and less bandwidth-intensive use like microblogging could handle 100,000 users with under 10 seconds of latency.
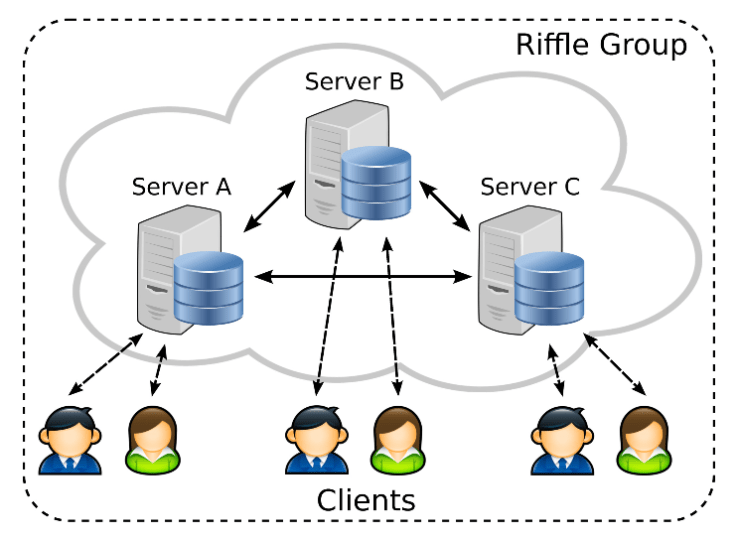
That was done, Kwon wrote, on three servers running on a gigabit LAN. But adding servers, counterintuitively, would actually degrade performance in a way.
“The more servers there are, the more secure it is,” wrote Kwon. “However, in terms of performance, since all messages go through all servers, the less servers there are, the more performant it is.”
Small, secure networks rather than ubiquitous global ones is the idea, then, although 100,000 anonymous nodes is more than enough to serve many a country or community.
There’s no downloadable version of Riffle right now — Kwon said he’d like to clean up the code a bit first, since it’s really just a prototype at present. There’s no plan to commercialize it, either, nor will it be a replacement for Tor, even though it does some things vastly better.
“There are indeed some incompatible design goals,” Kwon wrote, “However, they could also be complementary to each other, taking advantage of both the security of Riffle and the large anonymity set size of Tor.”
Keep an eye on Kwon’s site for further updates.