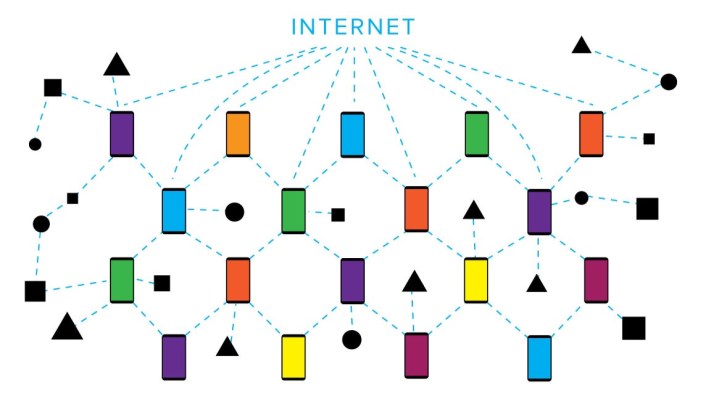
The massive and unprecedented utility and opportunities provided by the Internet of Things (IoT) have been shadowed by grievous security and privacy tradeoffs, which have become a focal point of attention for the tech industry in the recent months.
Discoveries like hacked baby monitors and remotely hijacked cars have given rise to new efforts and new initiatives, including the establishment of a foundation dedicated to defining standards and security practices for the IoT industry; a government-led solicitation project designed to encourage startups to address IoT security issues; and an educational book for children.
While IoT can borrow many lessons and tactics from security protocols and technologies that have been tested in other domains, there are some glaring differences between IoT devices and traditional computing systems.
The tech industry is taking strides to overcome the complexities these new devices introduce in order to make sure the future of IoT is not clouded by security shortcomings.
Differences in session lengths
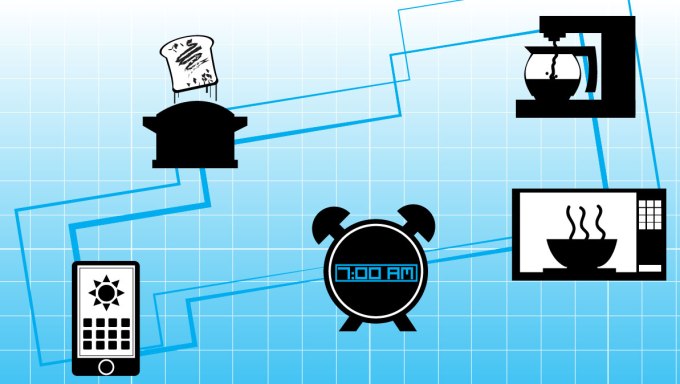
Current security protocols have been designed to control and protect the flow of data between computers in short-lived, intermittent sessions.
“In the IoT space however,” says Ken Tola, CEO of IoT security startup Phantom, “devices are connected for long periods of time, and using the exact same protection throughout these long-running sessions is no longer viable. Many of the successful exploits have occurred by recording encrypted communications and replaying those back into a system at a later date.”
Phantom is promising to mitigate the risk of replay attacks with an eponymous security software designed to securely authenticate a wide range of devices at any level of IoT systems and ensure protection in always-connected environments.
Phantom addresses the issue of long-running sessions by adding randomness and constantly changing how data is protected over time. “By switching algorithms at random intervals during sessions, Phantom prevents hackers from figuring out communications and by authenticating devices, Phantom keeps unwanted intruders out,” says Tola.
Phantom also addresses another IoT challenge, which is the scarcity of system resources. “Almost all modern protection relies on high-end operating systems and use massive amounts of resources,” says Tola. “None of these features are viable for the IoT.”
That is why Phantom has been designed to be extremely light-weight and operate at a very low level, which enables it to remain efficient on almost all devices.
Phantom is being tested in several IoT environments, including CANs (Controller Area Networks), which have been the main attack vector for major car hacks.
Differences in processing power and storage capacity
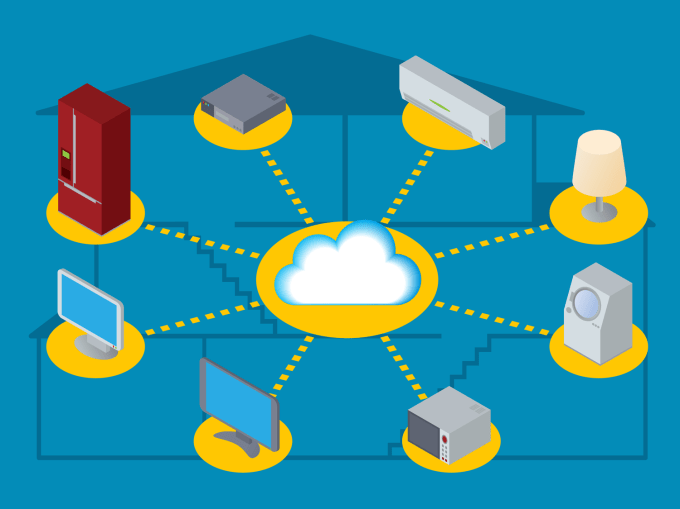
In contrast to computers and smartphones, a considerable percentage of IoT devices are incapable of running anti-malware software due to the lack of an operating system or the infrastructure needed to support such applications. They don’t have the processing power to carry out advanced techniques needed for protection against more sophisticated cyberattacks, and they don’t have the space required to store the ever-expanding databases of malware definitions.
IoT ecosystems need centralized, cloud-based solutions which would provide users with an intuitive interface to control devices and protect them against malware. Finnish tech company F-Secure wishes to achieve this goal with its new product, the Sense security monitor. Sense is a small gadget that connects to your home router and allocates its entire processing power to spotting and fighting malicious activity in your home network.
The device also monitors your network’s inner activities in order to detect devices that might have been compromised. As Mika Stahlberg, CTO at F-Secure, explains, “This feature is aimed at preventing IoT devices from becoming a bridgehead for bigger breaches against your network.”
Sense relies on F-Secure’s Secure Cloud to do its job. Secure Cloud is a smart repository of known viruses and threats that is constantly being updated with new information and feedback. According to Mika Majapuro, director of product management at F-Secure, “Sense leverages the power of Secure Cloud servers to carry out advanced tasks such as behavioral analysis and machine learning to detect, categorize and block new threats.” This is the kind of functionality that is beyond the power of individual IoT devices.
Differences in device behavior
In contrast to computers and smartphones, IoT devices are built for specific purposes and have limited functionality.
“But that’s actually a good thing in terms of security,” explains Yossi Atias, CEO and founder of tech startup Dojo-labs. “Every IoT device has a finite set of functions, and this allows us to tackle the IoT security issue from a totally different perspective.
“By analyzing the device network patterns and behavioral signature,” Atias elaborates, “you can detect network activity beyond the expected behavior that can indicate a compromised device or malicious activity. However complex, this is doable in the case of IoT devices, which unlike generic computing devices manifest a much smaller range of functionality.”
Dojo, the device being manufactured by Atias’s company, is a smart network device that adds a layer of protection to your home network. Among its functionalities is to discover devices connected to the network, secure them and constantly analyze their network activity. Dojo cloud platform is constantly updated with this behavioral information and with cyber security related knowledge. When a malicious activity or privacy breach is detected, Dojo notifies its owner through a mobile app, and in flagrant cases automatically stops threats. In addition to the mobile app Dojo provides simple color based indication through its pebble, using green, orange, red lights.
Differences in transfer methods

“Diversity in transfer mediums is much more intense in IoT than in traditional computing,” says Jim Reno, Chief Security Architect at Apcera. “Every message that is sent from an IoT device has to travel through various nodes before reaching its destination. These nodes rely on totally different technologies and protocols, many of which are prone to known attacks.”
The sheer number of IoT devices that are using improper encryption key storage methods and legacy security protocols is indeed worrying. The solution would be to have a scalable messaging infrastructure that could be integrated with various hardware and software combinations, and would ensure security regardless of the medium or technology used for the exchange.
This is the idea behind NATS, a flexible lightweight messaging system sponsored by Apcera, which can be used in various environments, including IoT ecosystems.
“NATS uses the TLS protocol and signed messages to ensure the integrity of communications,” explains Brian Flannery, Community and Ecosystem Manager for NATS. “It’s is a text-based protocol, providing very low-latency, and making it easy to implement in a variety of programming and scripting languages. This is important, as devices connecting to the network may have limited processing power, and come in many varieties. NATS can process millions of messages per second, which makes it efficient in IoT environments where numerous devices are involved and operations are time-critical.”
NATS is already being used and tested in several IoT devices and technologies, including Raspberry Pi, which is fast becoming an IoT development favorite.