Jailbreaking your iPhone has its downsides. In what’s being called the “largest known Apple account theft caused by malware,” security specialists Palo Alto Networks on Sunday released a report detailing a new form of iOS malware it’s calling “KeyRaider,” which is responsible for stealing the account information from over 225,000 Apple customers. The malware targets those with hacked – aka “jailbroken” – iOS devices, so is not a significant threat to the millions of Apple account holders who have not made modifications to their device’s software.
Jailbreaking, for those unfamiliar with the term, is an activity that was more common in previous years as it allowed Apple device owners to install otherwise unapproved apps and tweaks on their iOS devices.
Many of these jailbroken apps allowed users to personalize their iPhone with things like themes, widgets, launchers, different user interfaces and more. However, the activity has declined in popularity as Apple began to address some of the reasons users jailbroke their phones in the first place by adding officially approved customization options like Today widgets, dynamic wallpapers, improved multitasking experiences, custom keyboards, and more.
Because jailbreaking an iOS device means the user is routing around the built-in security protections, that can open them up to malware attacks like this. For example, in the past, an attack called “Unflod” intercepted encrypted traffic to steal Apple passwords. Another attack called AppBuyer used a similar technique to steal passwords and purchase apps from the App Store.
However, the KeyRaider malware goes further.
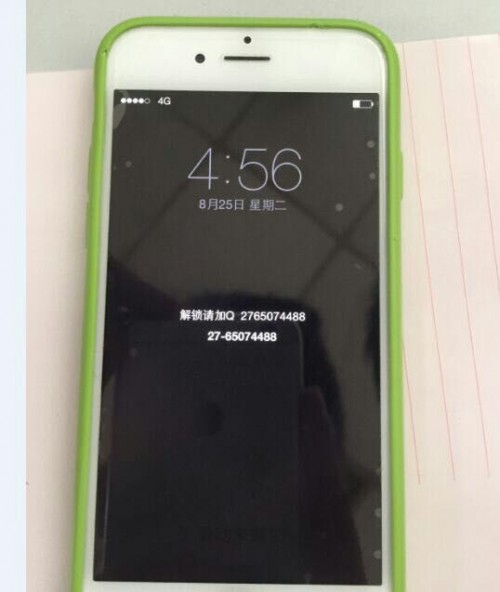
It doesn’t only steal Apple account user names, passwords and device GUIDs (device IDs), it also steals certificates and private keys used by Apple Push Notification Service and it prevents the infected iPhone or iPad from being unlocked either by passcode or the iCloud service.
That has led to some users having their iPhone held for ransom in wake of the malware’s distribution.
The research into this latest malware was conducted by Palo Alto Networks along with amateur technical group WeipTech, which is made up of users from a large Apple fansite called Weiphone, based in China. The group had begun investigating reports that some users’ Apple accounts were being used to make unauthorized purchases and install apps.
Details of this hack were previously reported by Chinese tech press in August, noting that with access to user account information, attackers could also acquire personal data, like emails, messages, documents, and photos.
KeyRaider was distributed by third-party Cydia repositories in China, but impacted users from outside the country as well, including those from France, Russia, Japan, United Kingdom, United States, Canada, Germany, Australia, Israel, Italy, Spain, Singapore, and South Korea.
However, Palo Alto Networks tells us the majority of the infections are in China.
“We did identify e-mail addresses associated with many other countries, but they were the minority,” Ryan Olson, intelligence director of Unit 42 at Palo Alto Network tells us.
He also says that Palo Alto can’t definitively be sure this is the largest attack to date, because it’s not always possible to quantify the size and scope of these hacks.
“Typically we don’t find out how many credentials were stolen,” Olson explains. “In this case, WeipTech was able to access the database of stolen credentials which gave us a much better count than in previous events.” Olson also adds that malware for iOS is not as common, though other data breaches have leaked info, as noted above.
People today may be most familiar with the celebrity photo iCloud attack, for example, which leaked private photos. But that attack was a much smaller scale, affecting hundreds at best, and was based on phishing, not malware.
[gallery ids="1202638,1202637,1202636,1202635,1202634,1202633"]
According to Palo Alto Networks, KeyRaider malware has stolen over 225,000 valid Apple accounts and thousands of certificates, private keys, and purchasing receipts. The stolen data is uploaded to a command-and-control server which also has vulnerabilities.
The attack makes it possible for users of two iOS jailbreak tweaks to download applications from the App Store without paying. To date, the tweaks have been downloaded over 20,000 times which means that around that number of users have been abusing the account information of 225,000 stolen credentials.
The malware is more of a concern in China, not only because of the way it was being distributed (through Chinese Cydia repositories), but also because many sellers in the country sell pre-jailbroken iPhones to customers.
In other words, KeyRaider is not an issue that affects a broad portion of the iOS user base. Apple had a reported 885 million iTunes accounts as of a year ago, so 225,000 affected individuals is a very small percentage of Apple account holders. But the malware’s existence does indicate there could be potential problems ahead as Apple’s presence in the Chinese market grows.
We reached out to Apple for comment, and will update if one is provided.
