Who have the DDoS attackers not hit? That’s the question. This morning, RSS reader and feed-syncing platform Feedly is being hit by a distributed denial-of-service attack, where again the criminals are attempting to extort money in return for returning the service to normal operations. And only yesterday, Evernote was a victim of a similar attack.
These attacks seem to be increasing in frequency, and now leave a long line of victimized sites in their wake, including Meetup, Basecamp, Vimeo, Bit.ly, SAY Media/TypePad, Namecheap, Plenty of Fish and Moz, to name a few of the more recent victims.
And on Friday, cloud-based security services provider Incapsula fought off a 100 gigabits per second DDoS attack against an online gambling website that utilized more than five DDoS attack vectors, including a SYN flood, large SYN flood, NTP amplification, DNS flood and DNS amplification, according to reports.
If you’re not familiar with the tech lingo, just know this: These DDoS attackers have uncovered more powerful ways to attack by exploiting insecure Internet protocols, like NTP, which allow for attacks that in years past would have been considered record-breaking.
For comparison’s sake, one of the largest DDoS attacks was that of Spamhaus last year, which peaked at 300 Gbps in size. Now massive attacks are par for the course, and as network providers improve in their ability to protect against these attacks, the criminals are stepping up, too. In Incapsula’s DDoS report from this spring, the company found that 81 percent of DDoS attacks are now multi-vector, and these are becoming more common.
Increase In Attacks
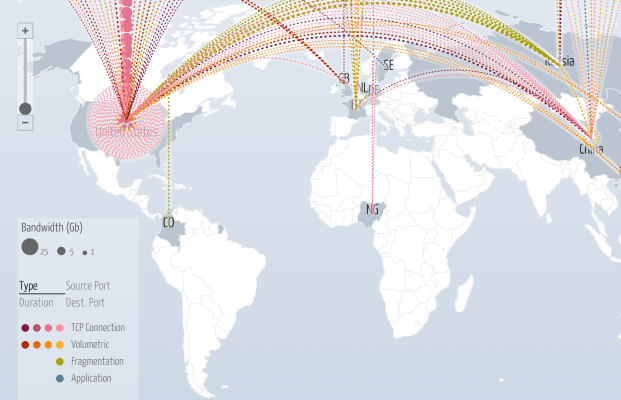
Every day, sites around the world are being hit, as this map shows. And, according to Matthew Prince, CEO of CloudFlare, whose company has worked with many of the victims to help them restore service, large-scale attacks have been ramping up.
“As a general trend, over the last three months there’s been an increase in very large attacks targeting DNS infrastructure. These appear to be coming from a large botnet concentrated in China. That doesn’t mean the attacker is actually in China, just that there are a lot of compromised PCs running there,” he explains.
These attacks are always high in bandwidth, but they’re large in the number of packets sent per second – some as high as 200 million+ per second. However, most of these new-style attacks have been hitting gambling sites, not the tech companies. However, Prince notes, that may change in time.
“I won’t be surprised when these extremely high packet volume attacks start targeting more mainstream sites,” he adds. “The challenge is, unless you have a massive network like Google or CloudFlare to absorb them, the attacks are getting large and sophisticated enough that even a large, tech-savvy organization like Evernote has no way of stopping them on their own.”
Evernote And Feedly
In Evernote’s case, the company noted yesterday evening that it was unavailable, and that it was working to neutralize a denial of service attack. A few hours later, a message on Evernote’s Twitter account said its service was restored – but it’s not out of the woods yet. “There may be a hiccup or two for the next 24 hours,” the tweet warned.
Evernote is up and running. There may be a hiccup or two for the next 24 hours. We appreciate your patience.
— evernote (@evernote) June 11, 2014
Early this morning, around 2 a.m. PT, Feedly became the next target. Again, like most companies who publicly disclose their status, Feedly is not paying the cybercriminals the ransom demanded, but is instead working with its network providers to mitigate the attack, as well as with other victims and law enforcement. As of 6:25 a.m. PT, Feedly says that while it has a restoration plan in place, it will still be several hours before the service is back online. Fortunately, users’ data has not been lost or compromised, the blog post notes.
It’s interesting that, while none of these more high-profile companies are paying the attackers off, the DDoS attacks continue. Why is that?
It could be that while the ones conscientiously updating their customers as to their status are not playing the criminals’ games, others may be. We had heard from one source that some New York-based tech companies did pay off DDoS attackers when they were hit, but never said anything — the only way you would know is if the companies were experiencing outages.
We’ve not been able to confirm this, so count this as a rumor for now. However, it would make sense that if some victims pay, the attacks will never end. Just like spam email, someone keeps clicking.