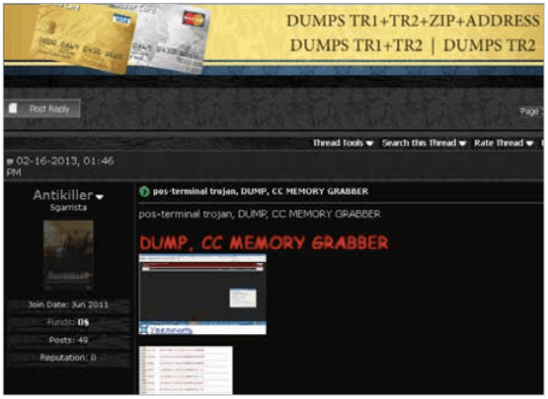
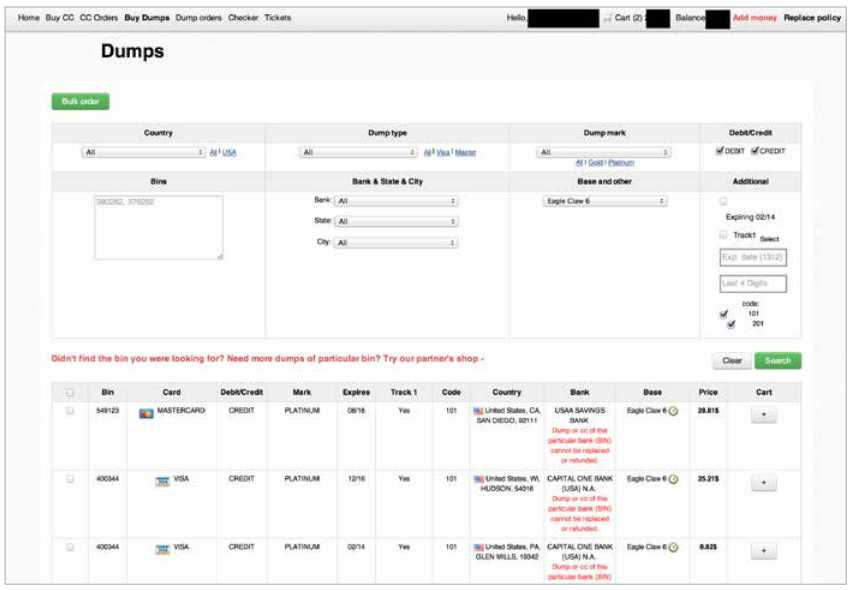
It looks like the rise of the “as a service” model, where people can buy software, platform access, security and more from a cloud-based provider for a fixed term, may have spawned its Damien: cybercrime as a service. The latest report from McAfee notes that the rush of point-of-sale credit card breaches that hit consumers in Q4 of last year — most notably at Target but other retailers as well — came from such sources, with the malware used “likely purchased ‘off the shelf’ from the Cybercrime-as-a-Service community” (one example illustrated above). McAfee also provided an update on the state of mobile malware — which it refers to as a “malware zoo”. It is showing little sign of abating, up 197% over the same quarter a year ago.
McAfee’s conclusions on the credit card breach paint a depressing picture for what is on offer for those who are intent on such thefts in the future. Although these were perhaps the biggest credit card breaches yet, and actually occurred at point-of-sale locations rather than online, the web had a big part to play, regardless.
“What is even more notable is how well the malware industry served its customers,” Vincent Weafer, SVP of McAfee Labs, writes. After purchasing off-the-shelf point-of-sale malware online (in Target’s case, it was called BlackPOS), the malicious hackers modified it specifically for their purposes.
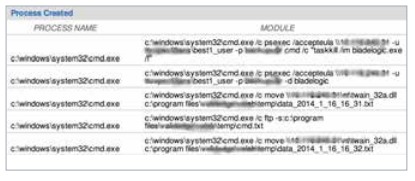
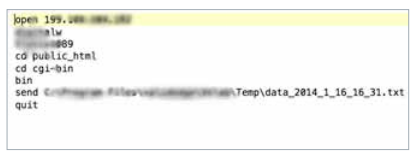
Working with different agencies, McAfee says that it was able to identify the coding used both to extract different data (domain names, user accounts, etc.) as well as the code that fed that data back to the hackers (respectively shown below):
“They even had a ready and efficient black market for selling the stolen credit card information, including an anonymous, virtual-currency-based point-of-sale payment system. Raw materials, manufacturing, marketplace, transaction support—it’s all there for thieves to use,” he writes. McAfee estimates that the credit card data — reportedly 40 million credit card numbers reported stolen — is being sold in batches of 1 million-4 million on marketplaces like Lampeduza Republic.
Other notable points in the McAfee report:
— Malicious signed binaries are on the rise. McAfee says that the growth of “dubious” content distribution networks — or the abuse of legitimate ones — is seeing a big spike in certificate authorities (aka CA — used to make secure connections over the internet) being piggybacked by malicious applications. In Q4, it says it found over 2.3 million new and unique malicious signed binaries, a 52% increase over Q3. The number discovered in 2013 — around 5.7 million — was more than three times the number discovered in 2012. “This threat is not only expanding ever more rapidly, but it is also becoming more complex,” McAfee writes. In total there were more than 8 million malicious signed binaries in 2013 — throwing into question the safety of the CA model.
— Mobile malware. This continues to climb, with 2.47 million new samples collected in 2014, and 744,000 in Q4 alone, rising 197% compared to a year ago. McAfee doesn’t single out a specific platform, but Android — as the world’s most popular smartphone platform, has been pinpointed by others as a particular target.
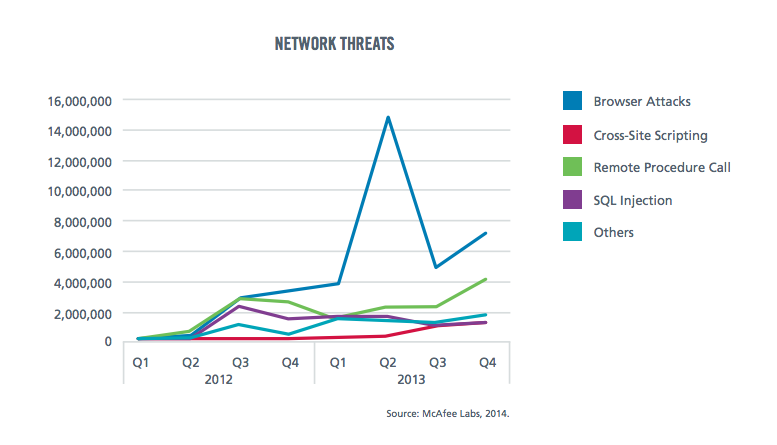
What’s interesting is that while the whole year is up on 2012, the biggest spike of all was actually a year ago:
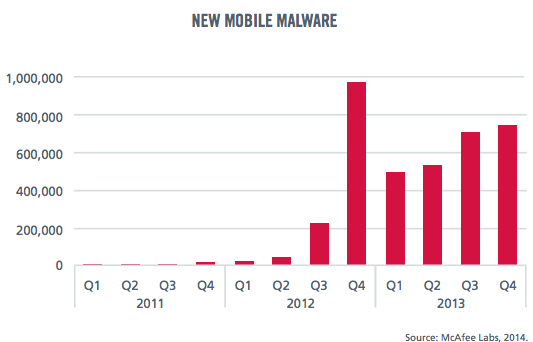
McAfee notes that mobile malware is finding its way to devices in much the same way as other platforms like PCs — through apps, through browsing online and so on. It also notes that its compiled a list of apps in a “reputation database” that tracks how much information they pull from users and how that increases their privacy riskiness. And just as they guessed, it turned out that of the top 10 in that list, six contained malware. (We’re trying to see if they will share the top 10 list with us.)
— Malware increase. McAfee tracked 200 new malware samples every minute in 2013.
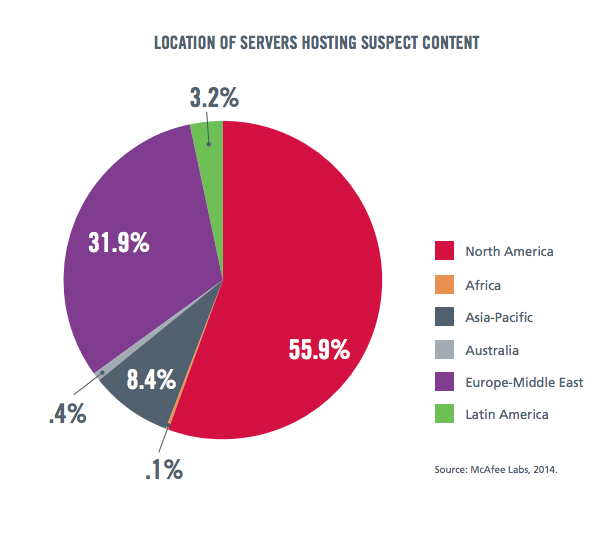
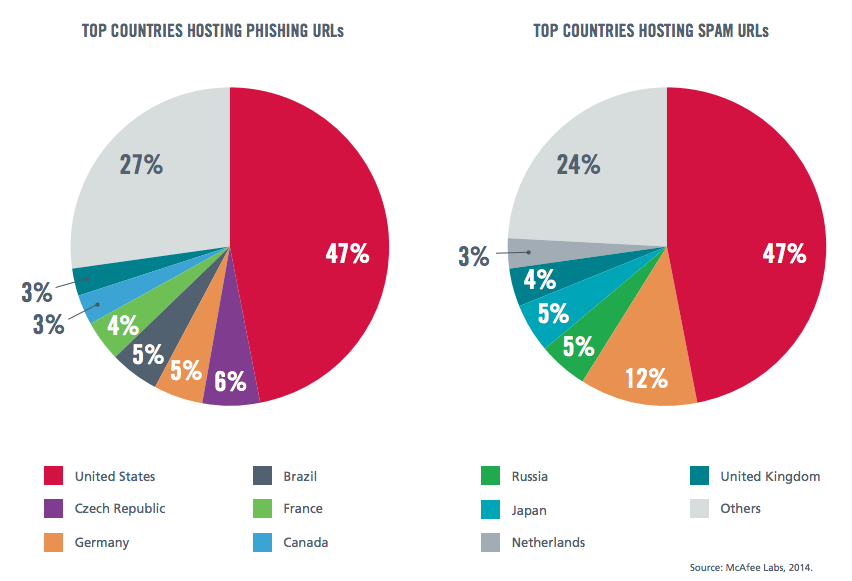
— North America still tops the list for dodgy content. Despite the rise of certain countries as hotbeds of malicious hackers, the U.S. is still topping McAfee’s list for hosting suspicious content and spam URLs. (U-S-A!)
— Overall, browser attacks remain the most-common route for malicious hacking.