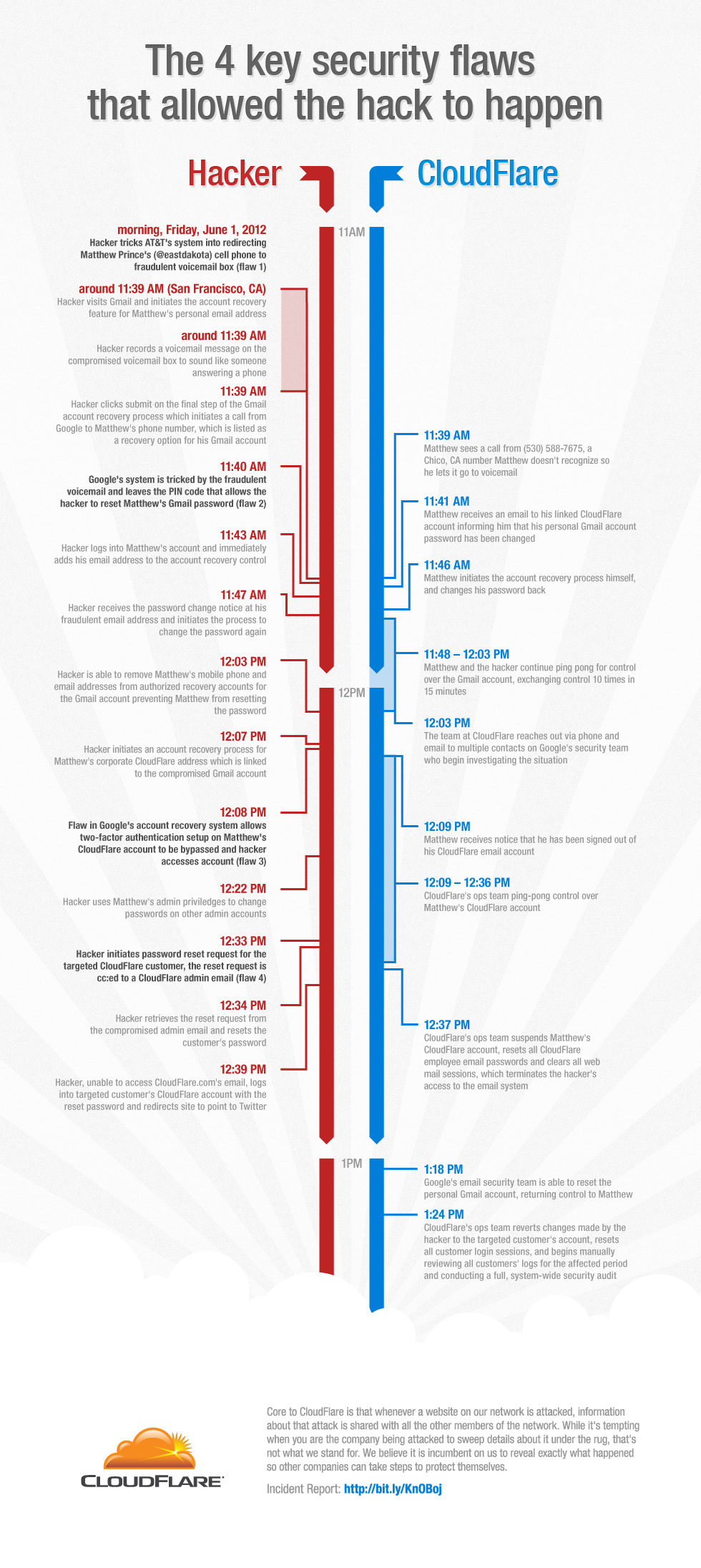
CloudFlare, the increasingly popular security and CDN service, suffered a security breach last week that allowed hacktivist group UGNazi to hijack CloudFlare CEO Matthew Prince’s Gmail account and gain access to the account of one of CloudFlare’s customers. CloudFlare won’t say who exactly the hacker targeted with this attack, but rumor has it that 4chan.org was likely on the hacker’s hit list. Now, after investigating the problem over the weekend, CloudFlare is releasing more information about how this could have happened. As Prince told me earlier today, the attack was the result of flaws in AT&T’s, Google’s and CloudFlare’s security protocols. The hacker smartly exploited all of these to gain access to the CloudFlare user’s account.
According to CloudFlare, here is what happened: the hacker gained access to Prince’s Gmail account and because CloudFlare sends an email to all of its administrators when a customer changes a password, the user was able to use this information to gain access to this account.
This sounds relatively easy (and CloudFlare has since changed its policy and acknowledged that this was a “dumb” thing to do), but because Prince uses Google’s two-factor authentication to protect his Gmail account, gaining access to his inbox took some smarts on the hacker’s part. Through what was likely some smart social engineering, the hacker was able to get AT&T to redirect Prince’s voice mail to a fraudulent voicemail box. Then, the hacker went to Gmail and used Google’s account recovery feature to get Gmail to call Prince’s phone with a PIN code to let him reset his Gmail password. To make this work, the hacker also had to record a custom voicemail message to make Google’s systems believe that an actual person had picked up the phone.
Had Prince picked up the phone when this call came in, the attack would likely have been thwarted (at least for the time being). He didn’t, however, and the hacker now had the PIN code to reset Prince’s Gmail account.
Still, Google’s two-factor authentication should have stopped the attack at this point. It didn’t however. Google told CloudFlare that it found a “subtle flaw affecting not 2-step verification itself, but the account recovery flow for some accounts. We’ve now blocked that attack vector to prevent further abuse.” Talking to SecurityWeek, Google also acknowledged that “if an administrator account that was configured to send password reset instructions to a registered secondary email address was successfully recovered, 2-step verification would have been disabled in the process. This could have led to abuse if their secondary email account was compromised through some other means.” It’s not clear if any other Google accounts were ever compromised in this manner before.
Combine all of these issues with CloudFlare sending a copy of every password reset request and the hacker’s attack suddenly doesn’t look so hard anymore. As Prince told me, no credit card data was exposed and there is no evidence that the hacker accessed any other accounts. From beginning to end, the whole procedure took less than two hours.
For CloudFlare, which promises to keep its users’ websites safe from attacks, this was clearly a rather unfortunate event. As Prince also noted, though, the company has tried its best to be very transparent about what happened and how it is fixing these issues.