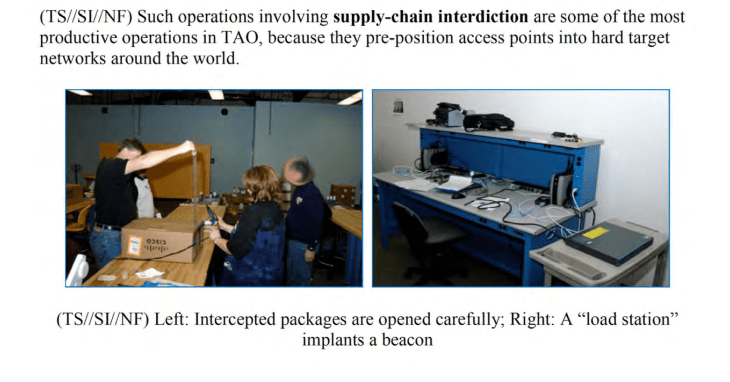
The photo above, released to coincide with Glenn Greenwald’s new book No Place To Hide, depicts the TOA – the Tailored Access Operations – division at the NSA where busy techs unpack expensive networking equipment in order to implant bugs and other tracking systems right into the hardware.
As we noted over the past few days, Greenwald alleges that the NSA routinely injected tracking systems into off-the-shelf networking components including hardware from Cisco. This photo shows just how glamorous this job really is as t-shirted techs carefully unpack boxes, plug the machines into an update station, and press a button. Hardware exploits are obviously a bit trickier but no less banal.
How valuable was the program? One NSA user wrote:
Whether or not this situation is moral or even legal is obviously in question but the potential for this program to backfire is extreme. Imagine this hardware going elsewhere around the world, potentially into an industrial situation where the exploit becomes a method for non-governmental espionage. And trust me: it happens. One manufacturer recently smiled while telling me that his own office was probably bugged “by competitors,” shrugging at the impossibility of ever knowing the truth. The NSA may have been looking to build a panopticon but what they’ve succeeded in doing is turning the gaze in on itself.