The Logitech Revue has been out for a few months now and it’s already been cracked wide open. The new hack allows “root” access, thereby allowing anyone to load their own apps into the box and have access to the full filesystem. The bad news? You need a soldering iron.
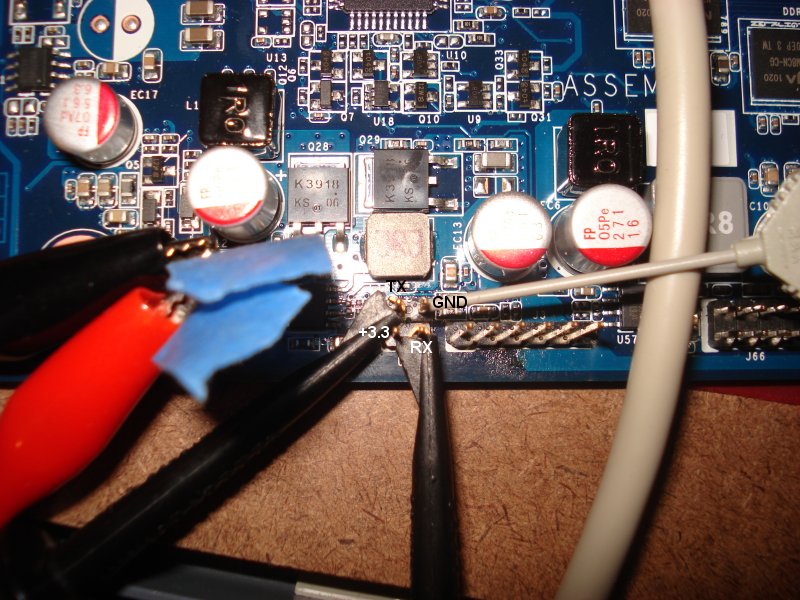
The hack uses the Revue’s UART1 port to upload a start-up script. You actually have to solder a set of leads to the mainboard and then connect to the box using a terminal program.
This is not a “try this at home” hack unless you’re good with an iron and an Arduino board. You can, however, check out the process right here.
The reason this is possible is due to the “out of factory” state of the Logitech Revue boxes not disabling the UART port on the board and allowing access to a root shell in recovery mode. After discovering this we were able to reverse the update files and manually upgrade the Revue to the most recent update. The attached files are our output of all the effort put forward by our team. Also as a notice to anyone performing the update, we are not responsible for any harm that may come of your box as an outcome of running our scripts. We will attempt to help you with any issues you may experience and have tried to make the process as safe as possible. Also if you have any suggestions or ideas on how we can make this process better please feel free to drop by our IRC channel and tell us.
ABOUT MANUAL-UPDATE
The manual-update.sh script is our attempt at duplicating the process done by the GTV scripts that update the box in recovery mode. There are also a few miscellaneous tweaks done to assure applications load correctly, backups are made, and that the box doesn’t auto-update. Some portions of the script do things such as flash parts of the NAND so make sure you do not short circuit your box or accidentally remove power during the manual-update process.