It didn’t take long for someone to hack the first OpenSocial application. In fact, it took just 45 minutes.
A developer who goes by the alias “theharmonyguy” and describes himself as “just an amateur” claims to have compromised the RockYou OpenSocial application on Plaxo called emote (see the Plaxo blog for details on the application). Specifically, he claims to have added a number of emoticons to Plaxo VP Marketing John McCrea’s profile within 45 minutes of it launching.
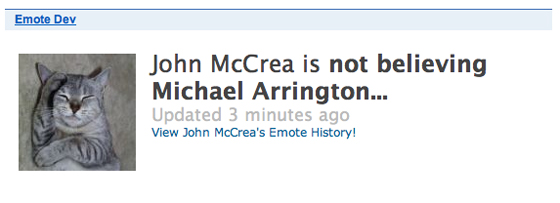
In an email, McCrea said he added all of the emoticons himself and his account doesn’t appear to be hacked. But when I asked theharmonyguy to hack my Plaxo account he did, within minutes, adding four quick emoticon messages such as “michael arrington is getting my bling on” and “michael arrington is w00t” (see image to left, none of those were added by me). theharmoneyguy then added one more to McCrea’s account, which will be difficult for him to deny:
theharmonyguy also pointed out specific problems with RockYou’s code, including some fairly humorous comments:
Some interesting code in there. For one, the app still doesn’t seem to be live for most of us (John McCrea from Plaxo has used it somehow) – it currently loads a “Please wait” iframe that never changes. But check out these code comments:
// TODO: no error checking – we’re bold…
// TODO: figure out why this is necessary???Also, the code constantly branches between Plaxo and “default,” which appears to be Orkut. In fact, there are some hardcoded names that I bet showed up in some OpenSocial screenshots somewhere:
if (getContainerType() == “orkut”)
{
friendIds[iNumFriends] = “11285577331363942034”;
friendNames[iNumFriends] = “Raymond Chan”;
iNumFriends = iNumFriends + 1;friendIds[iNumFriends] = “15479081059638046412”;
friendNames[iNumFriends] = “Jia Shen”;
iNumFriends = iNumFriends + 1;
}
theharmonyguy says he’s successfully hacked Facebook applications too, including the Superpoke app, but that it is more difficult:
Facebook apps are not quite this easy. The main issue I’ve found with Facebook apps is being able to access people’s app-related history; for instance, until recently, I could access the SuperPoke action feed for any user. (I could also SuperPoke any user; not sure if they’ve fixed that one. Finally, I can access all the SuperPoke actions – they haven’t fixed that one, but it’s more just for fun.) There are other apps where, last I checked, that was still an issue ( e.g. viewing anyone’s Graffiti posts).
But the way Facebook setup their platform, it’s tons harder to actually imitate a user and change profile info like this. I’m sure this kind of issue could be easily solved by some verification code on RockYou’s part, but it’s not inherent in the platform – unlike Facebook. I could do a lot more like this on FB if Facebook hadn’t set things up the way they did.
Oh, Facebook apps can also be prone to injection – I can insert any FBML I want onto the canvas pages of one popular app. But once again, I can’t really do anything, because to interface with the app requires me to have code related to that app, which isn’t generally available. Not sure if Google’s iframe implementation will be the same way.
Of course, the ability to change emoticons isn’t a particularly malicious hack; but the ease in which this was done suggests that Google has some work to do in getting its new platform stable. If they don’t, more damaging stuff may be on the way.
Update: Joseph Smarr, Plaxo’s Chief Platform Architect, says he has taken the application down for now:
Hi, just caught this thread now. Michael-thanks for the info. It does look like something isn’t quite working right. While I suspect it’s benign, e.g. some of the rockyou code not distinguishing between the “owner” and the “viewer” of the gadget (this stuff is not always easy to keep straight), I want to err on the side of caution, so I’m going to de-white-list the gadget for now.
As is, we’re maintaining a strict white-list so we don’t have any random would-be hackers messing around, and the platform itself is still a work in progress. Hopefully the benefit of seeing some real working OpenSocial code in production is worth bearing with a few kinks that need to get ironed out.