Just because almost every gadget or appliance can be connected to the internet, doesn’t mean they should be. Outages can render these “smart” devices useless, and many use weak security that can make them easily hackable.
And as security researchers recently found out, the consequences of having a major security flaw in one popular sex toy could have been catastrophic for tens of thousands of users.
U.K.-based security firm Pen Test Partners said the flaw in the Qiui Cellmate internet-connected chastity lock, billed as the “world’s first app controlled chastity device,” could have allowed anyone to remotely and permanently lock in the user’s penis.
The Cellmate chastity lock works by allowing a trusted partner to remotely lock and unlock the chamber over Bluetooth using a mobile app. That app communicates with the lock using an API. But that API was left open and without a password, allowing anyone to take complete control of any user’s device.
Because the chamber was designed to lock with a metal ring underneath the user’s penis, the researchers said it may require the intervention of a heavy-duty bolt cutter or an angle grinder to free the user.
Alex Lomas, a researcher at Pen Test Partners, said in a blog post that an attacker could lock “everyone in or out” very quickly. “There is no emergency override function either, so if you’re locked in there’s no way out,” he wrote.
The unsecured API also allowed access to the private messages and the precise location from the user’s app.
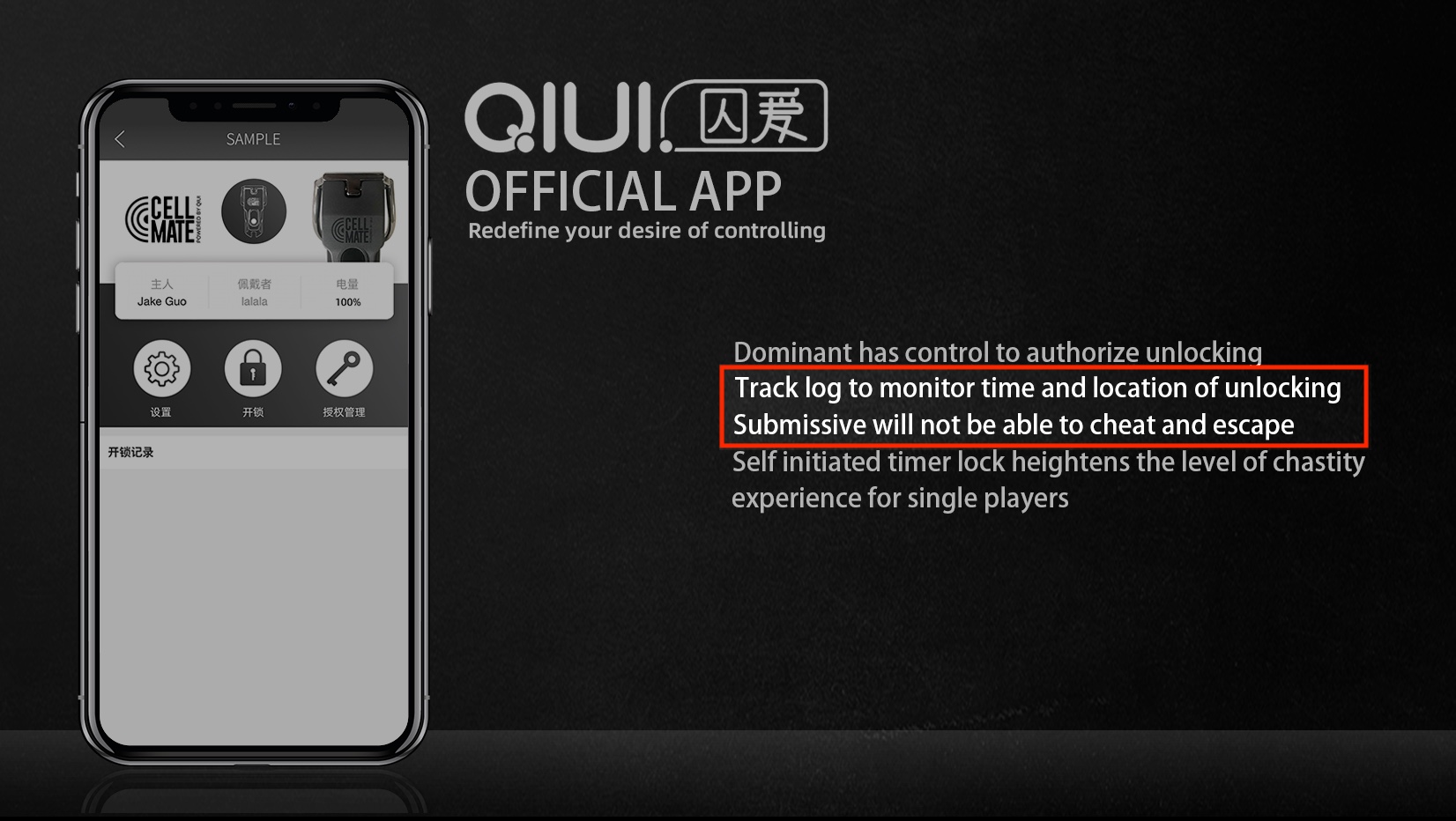
A vulnerability in the Qiui’s Cellmate app allowed anyone unauthenticated access to the private messages and location of any user. The lock on the chastity device can also be remotely controlled, researchers said. (Image: Qiui)
TechCrunch first learned of the vulnerability in June. The researchers contacted Qiui, based in China, about the flawed API. Taking the vulnerable API offline would have locked in anyone using the device. The developer pushed out a new API for new users, but left the unsecured API up for existing users.
Qiui chief executive Jake Guo told TechCrunch that a fix would arrive in August, but that deadline came and went. “We are a basement team,” he said. In a follow-up email explaining the risks to users, Guo said: “When we fix it, it creates more problems.”
In the end, Qiui missed the three self-imposed deadlines to fix the vulnerable API, said Lomas.
The decision to go public was made after Pen Test Partners learned of a separate security issue from another researcher, who also found it difficult to get a response from Qiui. “This reinforced our decision to publish: clearly others were likely to find these issues independent of us, so the public interest case was made in our minds,” wrote Lomas.
It’s not known if anyone maliciously exploited the vulnerable API. Several user reviews of the app complained that the app had bugs that would cause the device to stay locked.
“The app stopped working completely after three days and I am stuck!” said one user. Another said they “got already stuck twice when wearing it due to the unreliable app.”
“It worked for about a month until I almost got stuck in it. Thankfully it unlocked itself randomly and I was able to get out of it. The device left a bad scar that took nearly a month of recovery,” said another review.
Qiui joins a long list of sex toys with security problems that inherently don’t exist in non-internet-connected devices. In 2016, researchers say a bug in a Bluetooth-powered “panty buster” let anyone remotely control the sex toy over the internet. In 2017, a smart sex toy maker settled a lawsuit after it was accused of collecting and recording “highly intimate and sensitive data” of its users.
Practice safe sex; don’t use a smart device.
Related stories:
- An adult sexting site exposed thousands of models’ passports and driver’s licenses
- Plenty of Fish app was leaking users’ hidden names and postal codes
- A network of ‘camgirl’ sites exposed millions of users and sex workers
- Tinder’s new personal security feature can protect LGBTQ+ users in hostile nations
- Many smart home device makers still won’t say if they give your data to the government
- Group dating app 3Fun exposed sensitive data on 1.5 million users
