An internet advertising company specializing in helping law firms sign up potential clients has exposed close to 150,000 records from a database that was left unsecured.
The database contained submissions as part of a lead-generation effort by X Social Media, a Florida-based ad firm that largely uses Facebook to advertise various campaigns for its law firm customers. Law firms pay the ad company to set up individual websites that aim to sign up victims from specific categories of harm and injuries — from medical implants, malpractice, sexual abuse and more — who submit their information in the hope of receiving legal relief.
But the database was left unprotected and without a password, allowing anyone to look inside.
Security researchers Noam Rotem and Ran Locar found the database and reported it to the company, which pulled the database offline. The researchers also shared their discovery exclusively with TechCrunch and wrote up their findings.
The database contained names, addresses, phone numbers, the date and time of a person’s submission and the circumstances and explanation of their accident, injury or illness. Often this included personal health information, sensitive medical information, details of procedures or the consumption of certain medications or specifics of traumatic events.
Several records seen by TechCrunch include records from campaigns targeting combat veterans who were injured on duty. Other campaigns sought to sign up those who suffered illnesses from pesticides or medications.
Other campaigns included soliciting claims for sexual abuse. We found several names, postal and email addresses and phone numbers of victims, many of which also described their sexual abuse as part of filling out the website form.
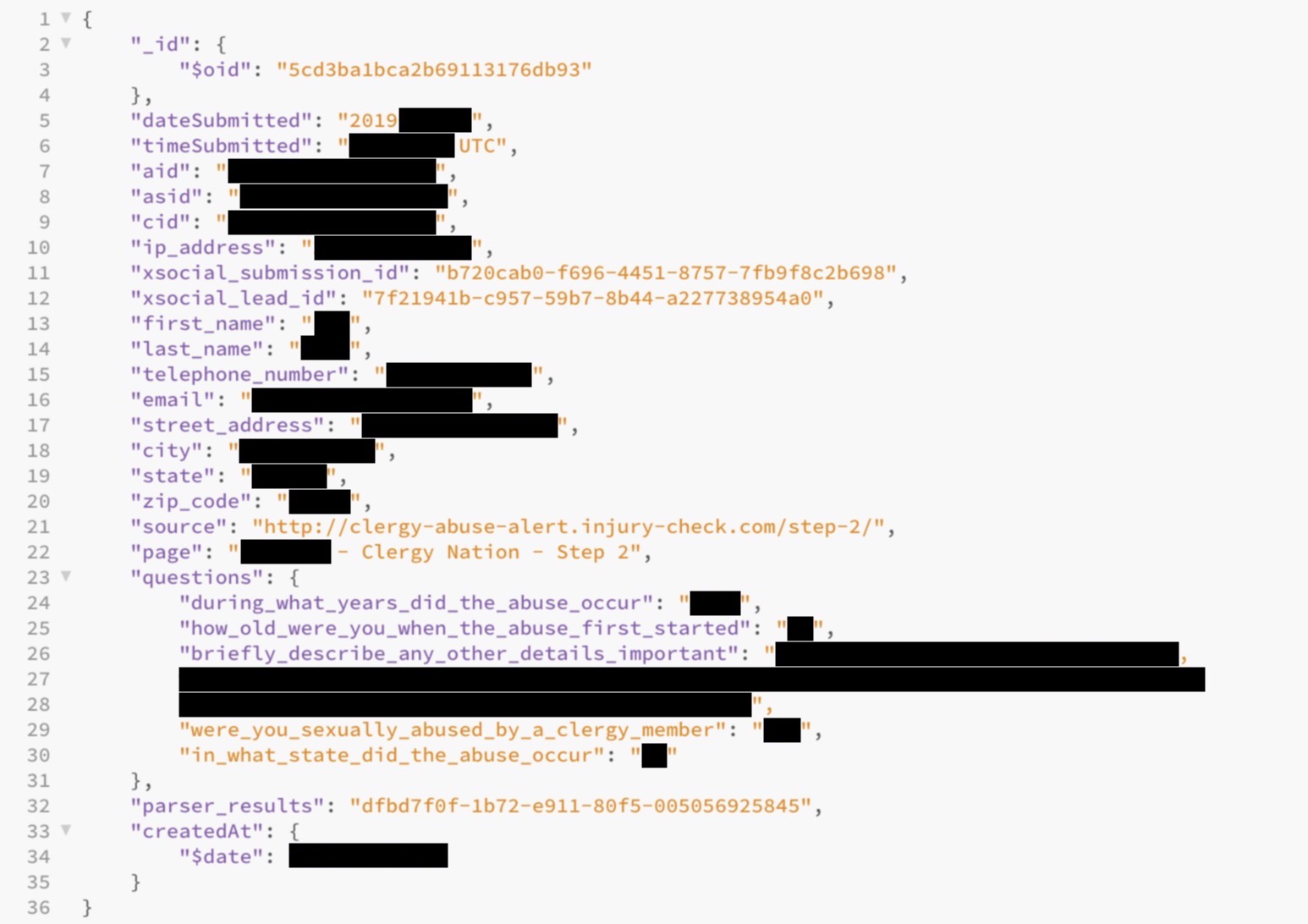
One of the records in the database. (Image: supplied)
The researchers said the exposed data could be “easily traced” back to the individuals who filled out the website forms.
The exposed database also contained a list of more than 300 law firms who paid X Social Media to set up the lead-generation operation. It also contained records of how much each law firm paid the ad company — in some cases amounting to tens of thousands of dollars. The database also contained the bank routing and account numbers of the ad company, which law firms used to pay the company for its services.
In reporting this story, we found a second, smaller database. In an effort to get the database secured, we provided the IP address to Jacob Malherbe, founder of X Social Media, in an email. Within an hour, the database had been pulled offline.
Despite this, Malherbe denied that the company stored medical data, described the findings as “inaccurate” and asked we “direct all other emails to our company lawyers.”
When presented with several files containing the data, Malherbe responded:
After being notified by TechCrunch about a security problems in MongoDB the X Social Media developer team immediately shut down the vulnerability create [sic] by a MongoDB database and did a night long log file review and we only found the two IP addresses, associated with TechCrunch accessing our database. Our log files show that nobody else accesses the database while in transit. We will continue to investigating this incident and work closely with state and Federal agencies as more information becomes available.
When asked, Malherbe declined to provide the logs to verify his claims. The company also wouldn’t say how long the database was exposed.
This is the latest exposed database found by the researchers in recent months.
The researchers have previously found data leaking on Fortune 500 firm Tech Data, exposed user records and private messages of Jewish dating app JCrush and leaking data from Canadian cell network Freedom Mobile and online retailer Gearbest.
Read more:
- Fortune 500 giant Tech Data exposed customer and billing data
- Jewish dating app JCrush exposed user data and private messages
- Rela, a Chinese lesbian dating app, exposed 5 million user profiles
- At Blind, a security lapse revealed private complaints from Silicon Valley employees
- Donald Daters, a dating app for Trump supporters, leaked its users’ data
- Security lapse exposed private Theta photos
- After breach, Stack Overflow says some user data exposed
- An unsecured SMS spam operation doxxed its owners