It took about six months for popular consumer drone maker DJI to fix a security vulnerability across its website and apps, which if exploited could have given an attacker unfettered access to a drone owner’s account.
The vulnerability, revealed Thursday by researchers at security firm Check Point, would have given an attacker complete access to a DJI user’s cloud stored data, including drone logs, maps, any still or video footage — and live feed footage through FlightHub, the company’s fleet management system — without the user’s knowledge.
Taking advantage of the flaw was surprisingly simple — requiring a victim to click on a specially crafted link. But in practice, Check Point spent considerable time figuring out the precise way to launch a potential attack — and none of them were particularly easy.
For that reason, DJI called the vulnerability “high risk” but “low probability,” given the numerous hoops to jump through first to exploit the flaw.
“Given the popularity of DJI drones, it is important that potentially critical vulnerabilities like this are addressed quickly and effectively,” said Oded Vanunu, Check Point’s head of products vulnerability research.
A victim would have had to click on a malicious link from the DJI Forum, where customers and hobbyists talk about their drones and activities. By stealing the user’s account access token, an attacker could have pivoted to access the user’s main account. Clicking the malicious link would exploit a cross-site scripting (XSS) flaw on the forum, essentially taking the user’s account cookie and using it on DJI’s account login page.
The researchers also found flaws in DJI’s apps and its web-based FlightHub site.
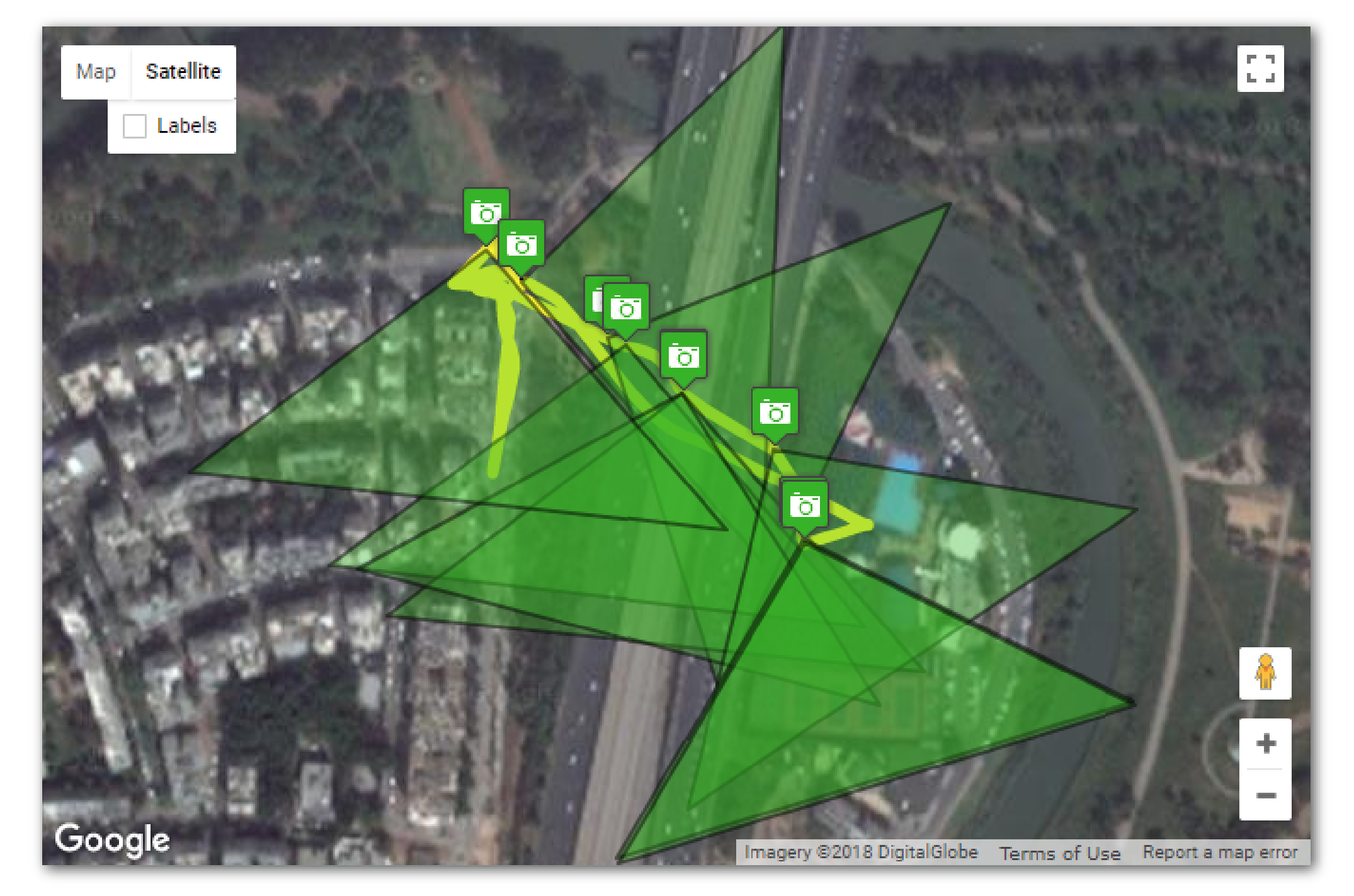
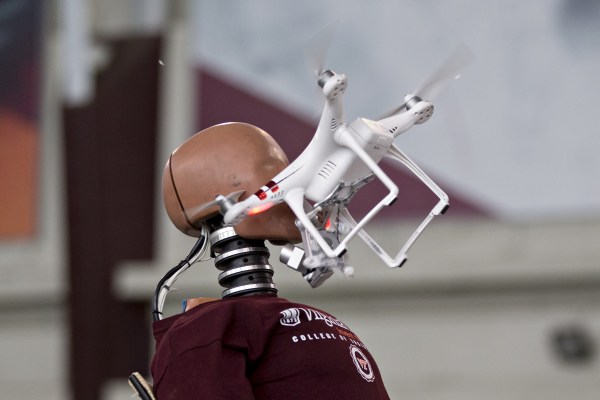
By exploiting the vulnerability, the attacker could take over the victim’s account and gain access to all of their synced recorded flights, drone photos, and more. (Image: Check Point)
Check Point reached out in March, at which time DJI fixed the XSS flaw in its site.
“Since then, we’ve gone product-by-product through all the elements in our hardware and software where the login process could have been compromised, to ensure this is no longer an easily replicable hack,” said DJI spokesperson Adam Lisberg.
But it took the company until September to roll out fixes across its apps and FlightHub.
The good news is that it’s unlikely anyone independently discovered and exploited any of the vulnerabilities, but both Check Point and DJI concede that it would be difficult to know for sure.
“While no one can ever prove a negative, we have seen no evidence that this vulnerability was ever exploited,” said Lisberg.
DJI heralded fixing the vulnerability as a victory for its bug bounty, which it set up a little over a year ago. Its bug bounty had a rocky start, after the company months later threatened a security researcher, who “walked away from $30,000” after revealing a string of emails from the company purportedly threatened him after finding sensitive access keys for the company’s Amazon Web Services instances.
This time around, there was nothing but praise for the bug finders.
“We applaud the expertise Check Point researchers demonstrated through the responsible disclosure of a potentially critical vulnerability,” DJI’s North America chief Mario Rebello said.
Good to see things have changed.