Malware that piggybacked on CCleaner, a popular free software tool for optimizing system performance on PCs, appears to have specifically targeted high profile technology companies and may have been an attempt to harvest IP — perhaps for commercial or state-level espionage.
In an update on its investigation into the malware, which was revealed to have affected 2.27M users of CCleaner earlier this week, Avast the security company which owns the London-based maker of the software, said the attack was an APT (advanced persistent threat) program that specifically targeted large technology and telecommunications companies.
So while the malware infected a total of 2.27M PCs between August 15, 2017 and September 15, 2017 — using CCleaner version 5.33.6162 as its distribution vehicle — the attackers behind it appear to have been interested in only a specific subset of PC users working for tech firms.
Avast hasn’t published the names of specific companies targeted by the malware for, it says, “privacy reasons” — but says companies in Japan, Taiwan, UK, Germany and the US were targeted.
Asked whether it believes a state-level attacker was responsible for the malware, a spokeswoman for the company told us: “We are not excluding any possibility. It is possible that this was the result of a State level attack or industrial espionage. However, rather than speculate, we are focused on working with law enforcement to identify the perpetrators and prevent any damage caused by a second stage payload.”
In another new development, Avast said it believes the malware’s second stage payload was indeed delivered — saying server logs indicate it was sent to 20 machines in a total of eight organizations but adding that the actual number is likely to be “at least in the order of hundreds” being as server logs were only captured for three days (vs the several weeks the malware was being distributed). It had previously said the second stage of the payload had not been delivered.
Avast adds that it’s continuing to investigate, along with law enforcement, to try to trace the source of the attack.
Tech firms specifically targeted
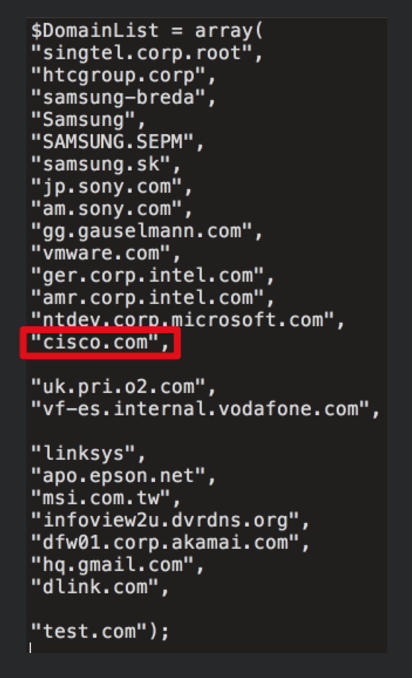
Meanwhile security researchers at Cisco Talos, who are also analyzing the CCleaner malware (using a digital copy of the attackers’ server passed to them by an unnamed source, and which it says it has verified to its own satisfaction), and publishing rather more detail as they do so — have revealed the below list of company domains which were apparently been specifically targeted for delivery of the malware’s second-stage loader.
The list apparently includes mobile makers Samsung, HTC and Sony, as well as telcos Singtel, Vodafone and O2, plus tech firms Cisco, Intel, VMware, Google and Microsoft. Also listed are: Linksys, Epson, MSI, Dlink and Akamai.
There’s also, rather chillingly, a distributor of security solutions, such as CCTV, alarm and door access systems.
One domain in the list not apparently targeting a technology business, per se, points to gambling company Gauselmann.
Cisco Talos’ researchers take the view that the targeting of “high-profile technology companies” suggests “a very focused actor after valuable intellectual property”.
They sum up their analysis as follows: “[A] fairly sophisticated attacker designed a system which appears to specifically target technology companies by using a supply chain attack to compromise a vast number of victims, persistently, in hopes to land some payloads on computers at very specific target networks.”
In its assessment of the second stage payload — i.e. the bit intended for the select tech targets — Avast describes the malware as a “relatively complex piece of code”, noting it is “heavily obfuscated and uses a number of anti-debugging and anti-emulation tricks”.
One part of the malicious code connects to an external server controlled by the attackers. While Avast says the structure of another component enables it to piggyback on other vendors’ code by “injecting the malicious functionality into legitimate DLLs” — describing such techniques as further evidence of the attacker’s “high level of sophistication”.
According to Cisco Talos’ analysis, the malware gathered system information from infected machines — including OS version information, architecture information, whether the user has administrative rights, as well as the hostname and domain name associated with the systems — and used this intel to determine how to handle those hosts.
They also describe this system profiling as “rather aggressive”, noting that it also included “specific information such as a list of software installed on the machine and all current running processes on the machine”.
“During the compromise, the malware would periodically contact the C2 server and transmit reconnaissance information about infected systems. This information included IP addresses, online time, hostname, domain name, process listings, and more. It’s quite likely this information was used by the attackers to determine which machines they should target during the final stages of the campaign,” they add, further noting compromised machines would share a list of installed programs, and a process list.
“When combined, this information would be everything an attacker would need to launch a later stage payload that the attacker could verify to be undetectable and stable on a given system,” they conclude.
They also make a point of demonstrating that the hackers could have used the same supply chain malware attack to target various other types of companies and organizations, noting that an analysis of the server database shows 540 affected systems attached to a domain containing “.gov” while 51 infected systems came from domains containing the world “bank”, and adding: “This demonstrates the level of access that was made available to the attackers through the use of this infrastructure and associated malware and further highlights the severity and potential impact of this attack.”
Avast is still recommending that consumer users of CCleader upgrade to the latest version (“now 5.35, after we have revoked the signing certificate used to sign the impacted version 5.33”) — and use a “quality antivirus product”.
But for corporate users it concedes “the decision may be different and will likely depend on corporate IT policies”.
“At this stage, we cannot state that the corporate machines could not be compromised, even though the attack was highly targeted,” it adds.
However Cisco Talos says that, in its view, those impacted by the attack “should not simply remove the affected version of CCleaner or update to the latest version but should restore from backups or reimage systems to ensure that they completely remove not only the backdoored version of CCleaner but also any other malware that may be resident on the system”.