This post has been updated to reflect new information about the reported incident involving a 737 and a drone in Mozambique.
As a Boeing 737 approached a landing strip in Mozambique, reports suggested a drone had crashed into it. Aviation Herald reported that “post flight examination revealed a drone had impacted the right hand side of the radome.” Subsequently, Mozambique’s Civil Aviation Authority concluded the radome most probably failed as result of a structural failure, ruling out a foreign object damage.
Like most security breaches, fessing up is often a sign of weakness, so we will never know. Over the last year, drone crashes have been reported at a nuclear facility, the Empire State Building and one crashed through a window into an office building. Some of these may have been hobbyists who lost control of their toys, but it’s a sign of things to come. For some, the war of the machines has begun — and you don’t need deep pockets to play.
According to a recent report, one of the biggest 2017 cybersecurity threats is weaponized drones. A Parrot AR drone costs less than $200. It can be hacked or hijacked easily. And it’s an excellent weapon in the hands of an irresponsible hacker.
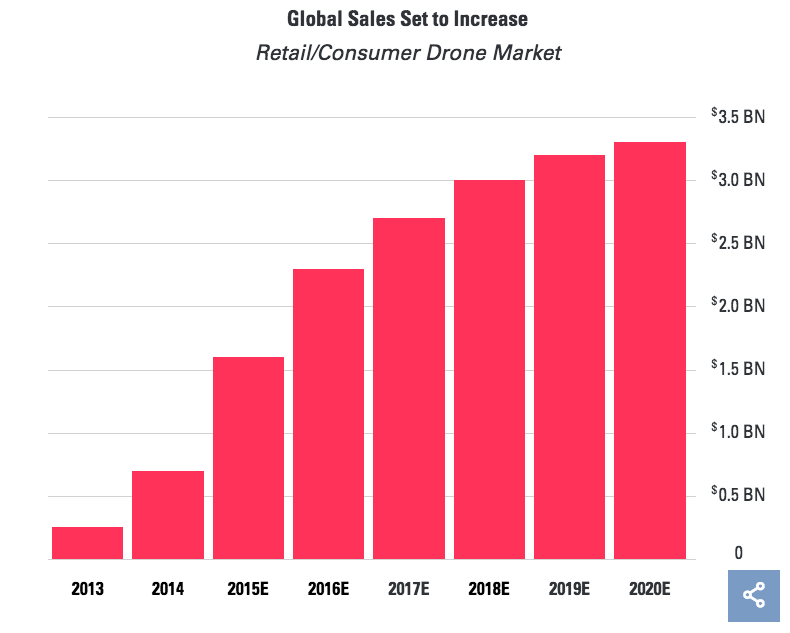
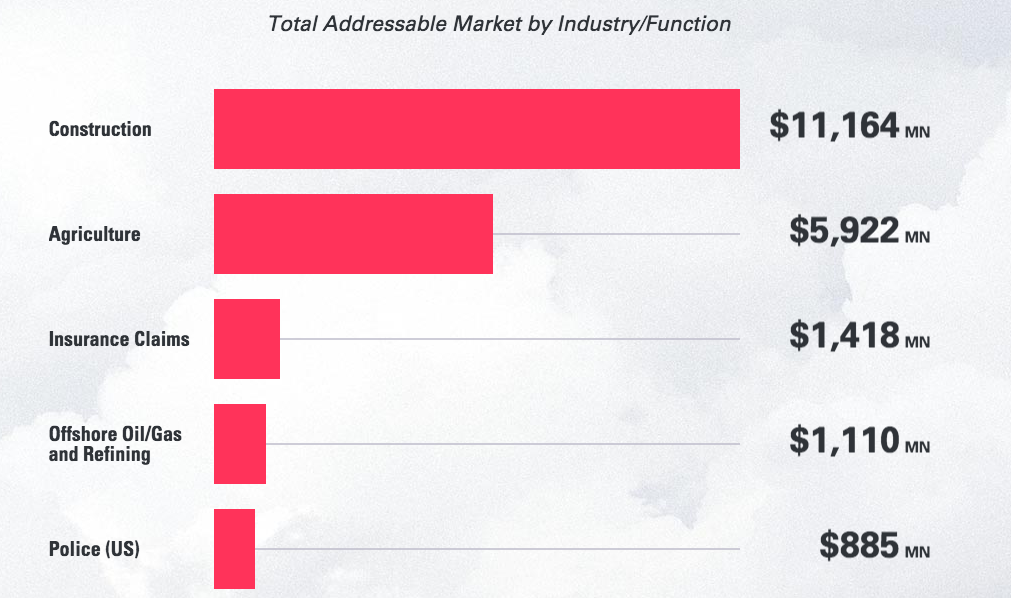
A Goldman Sachs drone market report predicts the retail market to be upwards of $2.5 billion in 2017. Drones will bring new efficiencies and drive ROI in market applications, such as construction (site review/mapping), agriculture (crop-yield estimation, crop scouting), insurance (equipment loss assessment), oil/gas/mining and police/emergency medical services. The combined TAM is a staggering $20 billion. Goldman Sachs predicts the U.S. to be the largest drone market, at $17.5 billion, followed by China ($4.5 billion) and the U.K. ($3.5 billion).
But when you start to dig inside the drone market map, I could not find much going on when it comes to security. Can we protect ourselves from rogue drones? Worse, if you call the authorities to say I’m being attacked by a drone, you would get a one-way ticket to the psychiatric ward.
Begging for help
As we have seen in other technology verticals, security is always an afterthought. Security is friction; it slows revenues and creates heartburn for product development. Over a few holiday drinks, one CISO told me that security teams are never invited for Christmas parties. Indeed, if we treat them as outcasts and pariahs of the technological landscape, society pays a price.
The FAA demonstrated how easy it is to hack leading drone brands such as Parrot, DB Power and Cheerson. None of these manufacturers used passwords or encryption. We saw similar “insecurity” trends in most IoT products where lack of passwords, encryption and embedded keys in the firmware point to the utter irresponsibility of IoT manufacturers.
The perimeter be damned; that attack surface just got three-dimensional.
In a recent demonstration, a drone was used to hack Philips Hue Wi-Fi-enabled light bulbs. Researchers (er… those nice-guy/whitehat hackers) pulled this off with minimal (a few hundred dollars) expense, and it was kinda cute that those hacked bulbs flash the “SOS” code, begging for help. This was a benign hack — an attempt to show IoT + drone = havoc. Physical security from drone attacks is paramount to our enterprise, societal and infrastructural landscape. A drunken lark was playing around benignly and crashed a drone inside the White House.
Note to Gartner: It’s about time we redefine perimeter security. A small investment of no more than a few hundred dollars can give tremendous leverage to a malicious actor. The lives impacted and the damage that could be caused can be significant. Soon, we will all be begging for help if this trend continues.
Dransomware
Consider ransomware. A recent Muni attack in San Francisco was a wake-up call. A public transit system is held up for ransom. While Muni was able to recover without paying the ransomware, estimates are that Muni lost $560,000 per day due to lost ticket sales.

Now, if you combine the malicious intents of ransomware actors with drones, the sky is no limit. With drone attacks, recovery may not be that easy. There is no “hot backup” in the physical domain.
What about drone security
Under pressure to grab market share, drone manufacturers are not necessarily focused on security. So security becomes a responsibility for someone else. While the FAA issued a rule requiring all UAS weighing more than 0.55 pounds (250 grams) to be registered, it’s unlikely to deter hackers.
I reached Sebastian Blum at Dedrone, a drone security startup, to better understand the implications of this new world in which we live. A recovering VC, Sebastian quit a lucrative job to join a startup. “We are seeing attacks inside prisons, data centers and public utilities. I don’t like the status quo. We are all romantics seeking to solve big problems — and this problem is getting bigger,” he told me. Sebastian pointed out that drones are being used to sniff data-center traffic, and even crash into data-center cooling systems.
Drones are being used to deliver goods inside prisons. And no sooner than a football game starts, and stadiums are beginning to see their airspace being invaded by drones. Dedrone, backed by Menlo Ventures, has developed a platform to detect and deploy a range of countermeasures against drone invasion of airspace. “As much as you may be tempted to, you cannot shoot a drone down — that’s against the law. Only law enforcement officials have that authority,” says Sebastian. And shooting a drone down will not remove the root cause of the problem.
Give me an umbrella
My favorite singer songwriter, the late Leonard Cohen, once said, “I don’t consider myself a pessimist. I think of a pessimist as someone who is waiting for it to rain. And I feel soaked to the skin.” Drones can, and will, cause havoc. Innovation sprints ahead causing insecurity, now in the physical domain. Regulatory forces will cramp down on innovation, rightfully so if the industry behaves irresponsibly. The Federal Trade Commission is suing D-Link for IoT security. D-Link had hard-coded “guest” as username and password — go figure!
In the meantime, the CISO has a new challenge. The perimeter be damned; that attack surface just got three-dimensional. Sniffing for traffic, logging incidents and responding has a whole new meaning. Some CISOs will step up to the challenge. And those who “wait” for the rain are bound to get soaked to the skin.
