According to Gartner, worldwide information security spending reached $76.9 billion in 2015. As the frequency and intensity of hacks worsen, security spending is expected to reach $170 billion by 2020. That’s more than 100 percent growth in five years.
Venture capital (VC) investments in cybersecurity startups continues to grow steadily (~40 percent each year over the past 5 years); 2015 may reach an all-time high, with projections of ~ $3.5 billion.
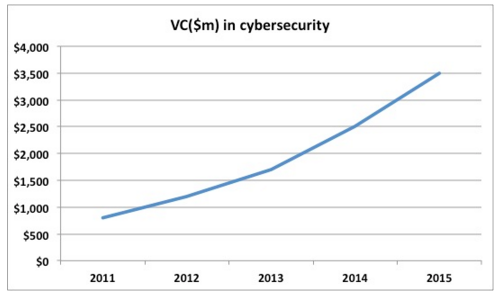
Source: CB Insights
Yet, when we look at cybersecurity as a percentage of all VC investments, the picture is somewhat sobering. Cybersecurity is less than 7 percent of all VC investments. Despite all the hacks and media attention, is the security sector under-funded?
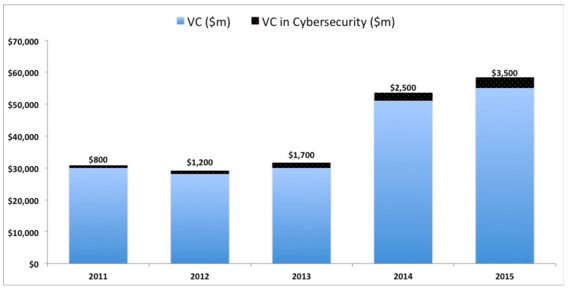
Source: NVCA, CB Insights
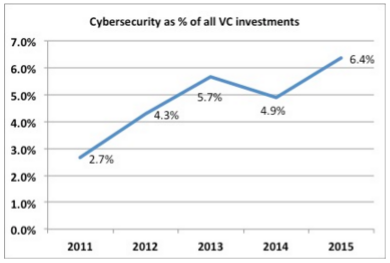
Source: NVCA, CB Insights
The conservative VC’s view
It’s all about exits and returns. Unicorns are a rarity in the security world. Security exits tend to fall in three distinct bands: ~$50 million, ~$200 million and $500+ million. Capital consumption is highly efficient as compared to other verticals, but the time-to-exit is much longer.

Cybersecurity exits range. Source: Author’s analysis. Data from CrunchBase
Authy, a two-factor authentication company (2FA) raised $3.8 million and was acquired by Twilio. Another 2FA company, Toopher, was acquired in April 2015 by Salesforce after raising less than $3 million. Aorato, backed by Accel, was acquired by Microsoft for $200 million. The company consumed less than $15 million. Smaller exits occur in ~3 years.
The third band of exits occurs in the $500+ million range. OpenDNS was acquired in 2015 by Cisco for $635 million. According to sources, it had reached $60+ million in ARR, but it took 10+ years from launch. Lancope, also acquired by Cisco in 2015 for $435 million, took 14 years to get to an exit. An occasional IPO like FireEye (IPO in 2014) or Palo Alto Networks (IPO in 2012) can create an adrenalin rush…but these are exceptions.
It’s baffling as to why enterprise cybersecurity budgets are stuck in archaic logic.
Many security startups are not unicorns; rather, they are cockroaches — they rarely die, and in tough times, they can switch into a frugal/consulting mode. Like cockroaches, they can survive long nuclear winters. Security companies can be capital-efficient, and typically consume ~$40 million to reach break-even. This gives them a survival edge — but VCs are looking for a “growth edge.”
The pace of growth in security companies is slower. FireEye (market cap: $6.5 billion) took 10+ years from startup to IPO. Palo Alto Networks (market cap: $11.6 billion) reached there a bit faster — in 7 years. When it comes to pace of growth and rapid value creation, there is no Uber in the security world.
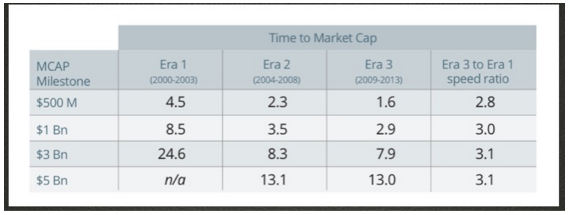
Speed matters! Between 2009-2013, tech companies could achieve market cap of $500 million in 1.6 years. (Source: Play Biggers Advisors)
Some tech darlings of the VC world have reached the $1 billion market cap (enviable unicorn status) in less than three years. That’s a challenge for cybersecurity entrepreneurs! If we cannot grow at such a pace, VCs won’t pay much attention. Funding in cybersecurity will remain stagnant, at less than 10 percent of total VC invested.
One of the leading VCs in Silicon Valley (the fund just raised more than half a billion dollars) told me that security is cool — but returns have been sporadic and below average. The double-whammy of low returns coupled with long exit cycles have marred VC enthusiasm. But if we read the tea leaves, things are getting better.
Expanding budgets
It’s baffling as to why enterprise cybersecurity budgets are stuck in archaic logic. Security spend should be ~ 10 percent of the total IT budget, as common thinking goes. At a macro scale, McKinsey experts state in their book Beyond Cybersecurity: Protecting Your Digital Business that total IT spend globally is approaching $2 trillion.
But security spend is still less than $100 billion. All it takes is one hack. And some budgets have surged to 300+ percent. This was affirmed by several cybersecurity experts I spoke with. I moderated a panel of leading cybersecurity VCs at Venture Alpha West 2015. Asheem Chandna of Greylock Partners, who sits on the board of Palo Alto Networks, Skyhigh Networks and other leading security companies, pointed out that across enterprises, security budgets are on the rise. This augurs well for cybersecurity startups.
With hacks becoming more intense, security awareness and importance is on the rise.
At least, buyers are aware. And board-level push for a better security posture is higher. Dharmesh Thakker of Battery Ventures, who has led investments in Cloudera and MongoDB, described that legacy companies are unable to react to technological shifts rapidly. Symantec and HP are undergoing structural changes and their ability to innovate and launch new products becomes constrained. They are tempted to partner.
Bob Ackerman, founder of Allegis Capital, has been investing in cybersecurity for more than 15 years. He pointed out that there has never been a better time for cybersecurity entrepreneurs. And while the fundamentals have not changed, the exit dynamics may be changing.
Cybersecurity VC Panel at Venture Alpha West 2015 . From L to R: Mahendra R (Secure Octane), Asheem Chandna (Greylock ), Bob Ackerman (Allegis Capital) and Dharmesh Thakker (Battery Ventures)
Expanding universe of buyers
Most VCs scratch their heads when it comes to exits in cybersecurity. The classical paths — IPO and acquisitions — are often narrow and constrained. IPO windows are subject to a variety of market conditions. As incumbents like Symantec and HP stumble, failing to adapt, newcomers benefit. In the past three years, Symantec has lost two CEOs and its revenues continue to shrink.
Its $900 million-a-year security business will soon be split away from its storage division. HP sells about $1 billion in security software and services each year, but its security revenues are shrinking rapidly. And Cisco can only buy so many companies. But the savvy investors see the landscape evolving with a number of new entrants in the market.
The onus of security is shifting to two new sets of players — the OS layer and the carriers. At the OS layer, companies like Microsoft, Intel and Google continue to pour capital into security. Google is one of the largest acquirers of security startups. With the proliferation of data centers and cloud providers, a new universe of buyers is emerging on the horizon.
From commodity to security
Carriers are tired of being a commodity business and see security as an opportunity to gain trust, increase cloud adoption and upsell. Earlier this year, SingTel announced a $810 million acquisition of cybersecurity company, Trustwave. Managed Security Services (MSS) is a $15 billion market, growing in double digits.
Gartner estimates that the size of the combined Enterprise Security Services IT Outsourcing and consulting services markets will be $47 billion in 2019. Large security services companies like IBM, Dell and AT&T are seeing a CAGR of 10+ percent each year, while small and mid-size service providers are growing at 100 percent each year.
This is music for carriers’ ears, aching to move away from the competitive world of commodity data centers. Verizon, AT&T (U.S.), British Telecom (U.K.), Orange (France) and NTT (Japan) are investing aggressively in cybersecurity services. As enterprises migrate to the cloud, they plan to shift their security burden to security service providers. When asked how enterprises expect to manage cloud security, 34 percent said they would look to a managed security service provider (MSSP).
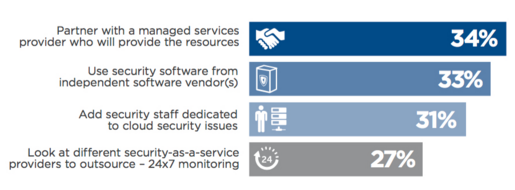
Source: Cloud Security Spotlight Report, Sep. 2015 survey ( 1,010 respondents)
Startups should bake in a managed services strategy in their offerings (as much as VCs hate it, customers want services). A tie-up with MSSPs could prove to be a valuable path to an exit.
In a parallel universe, private equity shops have found security roll-ups to be an efficient way to make money. Blackstone acquired Accuvant and Fishnet to create Optiv — one of the largest resellers of cybersecurity software in U.S. In March 2015, Thoma Bravo sold Blue Coat to private equity firm Bain Capital for $2.4 billion (Thoma Bravo had acquired Blue Coat in December 2011 for $1.3 billion).
The fundamental reason private equity shops have played in the cybersecurity arena is because a lot of startups/solutions are niche offerings. There is no “one-size-fits-all” security platform — it’s a mind-numbingly fragmented market, which irritates the heck out of investors and customers.
Challenges in 2016
The age of the overwhelmed CISO. With increasing hacks, the CISO’s life has just become a lot messier. One CISO told me, “Between my HVAC vendor and my board of directors, I am stretched. And everyday I get a hundred LinkedIn requests from vendors. Their FUD approach to security sales is exhausting.”
More than 50 large security vendors exist, and the list is growing rapidly. More than 200 new security startups are funded each year, competing for the CISO mindshare and budget. And the sales pitches use FUD (fear, uncertainty, doubt) as a primary tactic:
It’s like selling life insurance, but only by rubbing your face in it. A question from your insurance salesperson like, “What will happen to your kids if you die in a car accident?” will not generate any trust. Rather, I’d want an intelligent approach. Show me the data and the probability tree. And come to me with intellectual honesty. Earn my trust for the long haul — not one short-term BS vaporware sale.
CISOs want peace of mind in trusted partnerships. If they have a problem, do they trust you enough to call you in the middle of the night? They prefer to have comprehensive (not niche) solutions, which can be integrated within their existing systems and are built by security experts. While all products claim to be robust and reliable, CISOs need “IBM-like” solutions that can be defended in the boardroom. After all, their jobs are on the line.
The pace of security innovation often lags behind the pace of technology innovation.
This creates a challenge for startups that are seeking to grow fast; who are your early adopters? Not an average CISO for sure. Adam Ely, co-founder of BlueBox Security (backed by A16Z) did just that. “As we build our company, we work closely with CISOs who are innovative and entrepreneurial. Knowing such CISOs is critical to building your security startup,” he says.
The bigger question for cybersecurity entrepreneurs is not that of technological innovation, but that of being a trusted partner.
As SaaS security products become mainstream, the enterprise sales process is changing. In a low-touch world, developers need to be engaged. “Try before you buy” has become the primary mode of security sales. Let the customers come, play with it, try it!
Chinese mobile security company Cheetah Mobile (market cap: = $2.5 billion) offers free downloads of mobile consumer security products. It boasts of more than 500 million MAUs. Over a dim-sum lunch in San Francisco, Cheetah Mobile CEO Sheng Fu told me that the security sales model is outdated. “It has not evolved with the times. We need to think differently,” he said.
Raising seed capital just got harder. For seed-stage security companies, raising capital will not get any easier in 2016. According to CB Insights, security seed investments average about 2 percent of all dollars invested, and reached a five-year low in 2014.
Series A investment amounts have dropped steadily, from 31 percent of all investments in 2013 to 18 percent in H1-2015. Later-stage rounds have grown with Series B, up from 23 percent to 30 percent, and Series C, growing from 9 percent to 28 percent. Security companies have to now show that their product is past a proof of concept stage and scales rapidly.
This is largely due to the sheer volume of security startups. As one VC told me, half of these startups don’t know what the hell they are doing, and they all sound like each other. To raise capital, startups need to rise above the noise — differentiate with clarity and conviction.
Of signal, noise and stealth
Don’t innovate — differentiate. “I have seen at least 40 FireEye killers in the past 12 months,” one Palo Alto-based VC told me. Clearly he was exhausted. Some sub-sectors are overheated and investors are treading cautiously. Security founders often rely on their technical skills to find a niche in the marketplace. But establishing differentiators is the key. These differentiators can be around verticals of focus, features, channels, pricing and sales methodology.

Buyer behavior forces changes in security sales and product development
Crafting a business proposition is often harder as security sales are not based on Return-on-Investment. It’s a risk management approach. And the age-old tactic of “fear-based” selling does not work with intellectually savvy CISOs.
Having a clear contextual awareness of the other funded startups makes it easier to target the right VC and demonstrate your value proposition. Today, when most companies stay in stealth, contextual awareness becomes harder. Who has funded which company? And how does that impact your trajectory? After completing one pitch, the VC told the founder, “Thanks for sharing, but I have an exactly similar company in my portfolio,” and walked out.
Innovation lag — the road ahead. The pace of security innovation often lags behind the pace of technology innovation. Justin Somaini, CISO at SAP, told me that the “technology curve needs to flatten so that the security curve can catch up.” Security remains an afterthought, but that is changing.
SecOps/DevOps and continuous monitoring opportunities are driving innovation. Even privately held Kaspersky Labs is looking outwards to find innovative security startups. In February 2015, they announced a hackathon in quest of the next big thing.
A list of technology opportunities was released by Ponemon Institute earlier this year. Encryption, automation and analytics are in the top 5 — needless to say, customers demand data protection and automation.
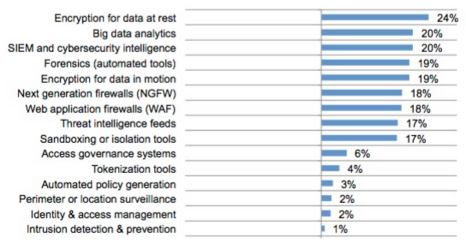
Source: Global Megatrends in Cyber Security, Ponemon Institute, March 2015
Such trends create immense opportunity for security entrepreneurs. Vertical-specific security tools for industrial/SCADA are in high demand. Wurldtech was focused on security for infrastructure and electric utilities. GE acquired the company, even as Wurldtech had raised less than $10 million.
One of the investors told me that the returns were “pretty nice, indeed.” The Jeep-Chrysler hack led to a recall of 1.4 million cars and a class action lawsuit. Soon thereafter, automotive security startups like TowerSec and Argus gained attention. And moral judgements aside, the Ashley Madison hack may have led to suicides.
With hacks becoming more intense, security awareness and importance is on the rise. While no one wants to live in a shark-infested digital ocean, that’s exactly where we have landed.
With budgets on the rise (as well as hacks), we will see more founders in 2016 jump in to start companies. Yet a rising tide of opportunity brings touristy challenges.
The security bazaar is noisier and messier than ever. Every company sounds exactly like the eight others, and lines get blurred. Those that thrive will do so on differentiation. Being frugal is great, but VCs don’t care about protecting the downside as much as a huge upside.
If cybersecurity companies scale faster, we will see more capital flowing into the arena. The second wave of security innovation has just begun. May the cockroaches thrive in the age of the unicorns.
