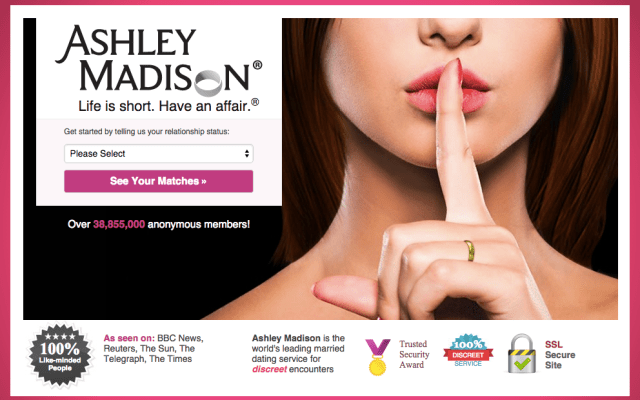
Hacked data from online extramarital affairs website Ashley Madison has apparently been leaked online, after a threat by a group of hackers to do so earlier this summer if the service did not shut down (which it has not).
In July the group, which calls itself The Impact Team, published a range of random user data they claimed to have taken from Avid Life Media, the parent company behind Ashley Madison and two other dating-related websites.
ALM claims Ashley Madison has more than 33 million members, spread across 46 countries — although the proportion of active profiles is unclear. The hackers themselves accused the site of scamming users with “thousands” of fake female profiles.
A post on the Hydraze blog late yesterday claimed the Ashley Madison data had finally been leaked on an Tor website. The data apparently includes some 33 million accounts; 36 million email addresses; and personal info including names, street addresses, phone number and credit card transactions.
A readme file contained with the data dump contains the following statement from its creators:
Avid Life Media has failed to take down Ashley Madison and Established Men. We have explained the fraud, deceit, and stupidity of ALM and their members. Now everyone gets to see their data.
Find someone you know in here? Keep in mind the site is a scam with thousands of fake female profiles. See ashley madison fake profile lawsuit; 90-95% of actual users are male. Chances are your man signed up on the world’s biggest affair site, but never had one. He just tried to. If that distinction matters.
Find yourself in here? It was ALM that failed you and lied to you. Prosecute them and claim damages. Then move on with your life. Learn your lesson and make amends. Embarrassing now, but you’ll get over it.
Any data not signed with key 6E50 3F39 BA6A EAAD D81D ECFF 2437 3CD5 74AB AA38 is fake.
While ALM has not confirmed whether the data dump is genuine, security researchers are inclining towards saying it looks genuine at this point.
The data dump was made on 11/07/15 — so any accounts created after that point wouldn’t be included.
Responding to news of the latest data dump in a statement, ALM said it’s investigating into the original hack is still ongoing.
Of the new revelations it said:
We have now learned that the individual or individuals responsible for this attack claim to have released more of the stolen data. We are actively monitoring and investigating this situation to determine the validity of any information posted online and will continue to devote significant resources to this effort. Furthermore, we will continue to put forth substantial efforts into removing any information unlawfully released to the public, as well as continuing to operate our business.
The statement goes on to condemn the hack as “an act of criminality”, adding:
The criminal, or criminals, involved in this act have appointed themselves as the moral judge, juror, and executioner, seeing fit to impose a personal notion of virtue on all of society. We will not sit idly by and allow these thieves to force their personal ideology on citizens around the world. We are continuing to fully cooperate with law enforcement to seek to hold the guilty parties accountable to the strictest measures of the law.
While strong on moral outrage, ALM’s statement provides no new details on how the apparent breach occurred. We’ve reached out to them to ask about their security and will update this post with any response.
Speaking to security investigator Brian Krebs yesterday, Ashley Madison’s original CTO Raja Bhatia, claimed the site never stored credit card information.
“We don’t store that,” Bhatia told Krebs. “We use transaction IDs, just like every other PCI compliant merchant processor. If there is full credit card data in a dump, it’s not from us, because we don’t even have that. When someone completes a payment, what happens is from our payment processor, we get a transaction ID back. That’s the only piece of information linking to a customer or consumer of ours. If someone is releasing credit card data, that’s not from us. We don’t have that in our databases or our own systems.”
However security researcher Per Thorsheim claims to have found active credit card data within the dump…
When news of the hack broke earlier this summer, Thorsheim also pointed out that Ashley Madison did not verify email addresses of users — so the presence of an email address within the data dump can’t be used to identify a genuine user of the site.
Security researcher Graham Cluley reiterated this point today, writing on his blog: “I could have created an account at Ashley Madison with the address of barack.obama@whitehouse.gov, but it wouldn’t have meant that Obama was a user of the site.”
So while security site CSO is reporting that the data dump includes some 15,000 email accounts that use a .mil (US military) or .gov email address — and The Telegraph claims the data also contains around 100 UK government email addresses — it’s not necessarily saying very much, given the lack of an email verification process.
Another security researcher, Robert Graham, who’s also been parsing the data dump, says he’s found credit card transaction data, but not full credit card numbers. However he notes that given the data does have full name and addresses it could “out” still serious users of the site.
Graham also notes that the hack includes full account information — so not just names but personal dating information, such as height and weight. Other news sources are reporting the data includes details about sexual fantasies, and also profile photos of users.
In addition to addresses, the data also apparently contains GPS coordinates. “I suspect that many people created fake accounts, but with an app that reported their real GPS coordinates,” Graham adds.
Account compromise checker @haveibeenpwned developer, Troy Hunt, has now added the Ashley Madison data dump to his service — albeit in a non-publicly-searchable format, in a bid to preserve some blushes. He has tweeted that so far some 5,000 subscribers to his service have received notifications that their details are in the data dump.
According Rob Graham, CEO of Errata Security speaking to Ars Technica, the dump also includes user passwords but these were cryptographically protected using the bcrypt hashing algorithm — which should make them tough to compromise.