As we spend more and more of our lives on social networks and marketplaces, YC-backed Smyte is launching out of beta to make sure we don’t get defrauded, spammed, or harassed.
While the Googles and Facebooks of the tech world have entire departments dedicated to preventing spam and abuse, building this infrastructure is a major pain point for smaller companies.
“To solve this problem, a lot of companies will take one engineer and stick them on it for a week, and they’ll have all these problems because you really need a specialist who’s done this before,” says Julian Tempelsman, co-founder of Smyte.
Tempelsman previously worked for Google, where he fought financial fraud for Google Wallet, spam and phishing for Gmail, and general Google Apps abuse. “I was pretty much seeing the worst of the worst of how shitty people can really be online,” Tempelsman says.
So he joined forces with co-founders Pete Hunt — who previously built React, Facebook’s number one open source project — and ex-Instagram engineer Josh Yudaken, to create Smyte, an out-of-the-box solution for two-sided marketplaces and social networks that improves trust and safety.
Essentially, in any situation where an untrusted buyer is interacting with an untrusted seller, Smyte is able to pick up on suspicious behavior before a user does anything destructive.
Developers can add a line of Smyte code into any website or mobile app, which gives Smyte access to a data feed. Smyte’s automated labeling system identifies any potentially malicious activity, based on a variety of signals and relationships, and flags it for manual review.
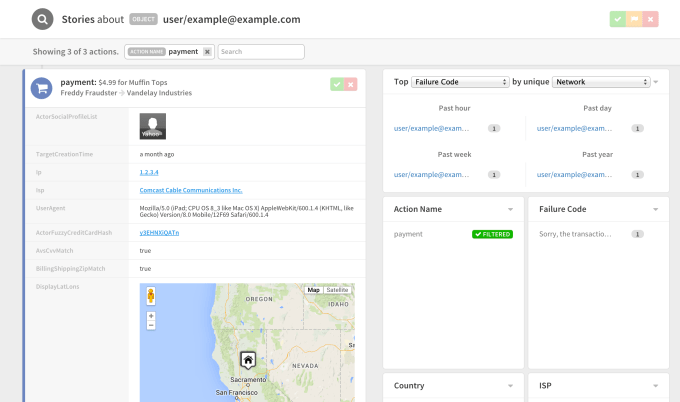
“If somebody is using a lot of credit cards over a given period of time, it probably means that they have a stack of stolen credit cards and they’re testing which ones work, and which ones don’t,” says Hunt.
But it’s just as important to let the good users through, even if their actions trigger warning signals. Grandma on Facebook, for instance, who goes in and friends everybody, is a classic example of an innocent user whose actions appear malicious to a machine.
“The sign of a system that’s not well-designed is if it kicks Grandma off because she looks like a scammer,” says Hunt. “The trick is not catching the bad guys, the trick is letting the good guys through, blocking the bad, and if you’re not sure about somebody, giving them a warning.”
Smyte is already working with some of the top crowdfunding platforms (though they won’t tell us which ones) to ensure that nobody gets defrauded. Hunt and Tempelsman tell me they’re currently processing millions of data points per day.
“What we’re doing is similar to HTTPS — you don’t type in your password or credit card data into a web browser that doesn’t have the lock icon, so why is it that people are interacting on sites and mobile apps if they don’t trust the system?” Hunt asks.
A graduate of Y Combinator’s Winter 2015 class, Smyte has raised $2.25 million in seed funding from Harrison Metal, Baseline Ventures, Founder Collective, Upside Partnership and YC.