Editor’s note: David Cowan is a partner at Bessemer Venture Partners, co-founded VeriSign, Good Technology and Defense.net, and co-authored several cybersecurity patents. He is currently a director of Lifelock, iSight, Endgame, Reputation, GetInsured, Rocket Lab, Smule and Zoosk.
In the past two years, cyberspace has clearly changed in ways that threaten every online business, big or small. Startups now use the cloud infrastructure that mature companies do, and quickly aggregate large, juicy caches of private user data and payment credentials. As malware infestations scale to scour the “long tail” of targets, they don’t discriminate between the Fortune 50 and the TechCrunch 50.
In fact, some increasingly common attacks — like DDoS extortion — specifically target smaller, more vulnerable businesses, whose loose cowboy cultures, shallow security expertise, fragile infrastructure and fresh capital make for easy pickings.
Jeremy Grant at NIST reports “a relatively sharp increase in hackers and adversaries targeting small businesses.” According to a recent survey, 20 percent of small businesses in Canada reported cyber losses last year. Who knows how many more fell victim and just don’t know it?
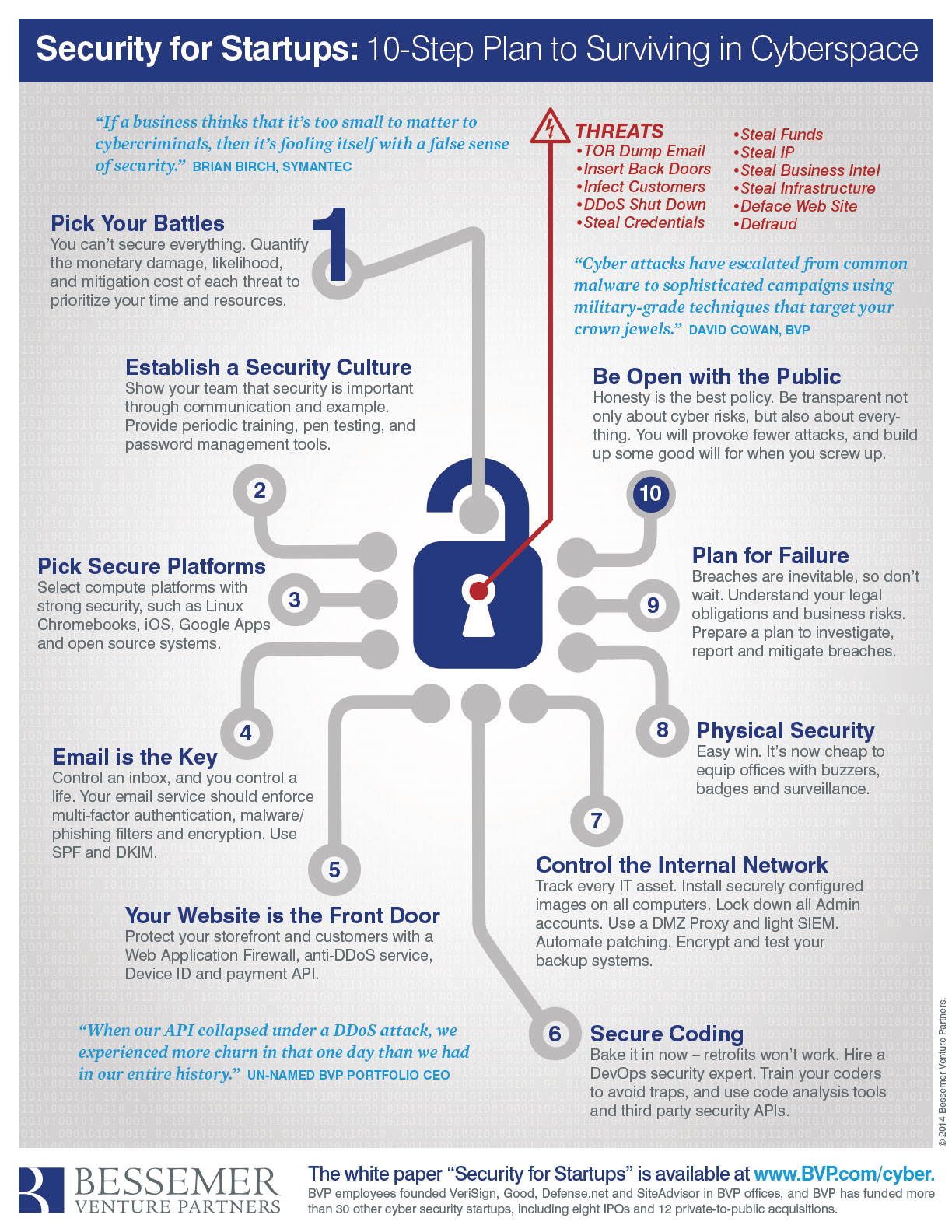
“Startups are incredibly vulnerable to cyber attacks in their first 18 months. If a business thinks that it’s too small to matter to cybercriminals, then it’s fooling itself with a false sense of security.” – Brian Burch, Symantec (CNN)
For many attacks—API disruption, marketplace fraud, IP theft—the smaller the target, the greater the damage. Startups often lose a year or more when targeted by identity thieves, nation-states, hacktivists, competitors, disgruntled employees, IP thieves, fraudsters or Bitcoin miners. Evernote, Meetup, Feedly, Vimeo, BaseCamp, Shutterstock, MailChimp and Bit.ly all fell victim to extortion rackets, and Code Spaces shut down altogether. “When our API collapsed under a DDoS attack, we experienced more customer churn in that one day than we had in the entire two years since our launch,” recalled one CEO.
Stubhub, Uber, and Tinder struggle to battle fraud in their marketplaces. Uber employees themselves were caught defrauding competitor Gett. Evernote, Bit.ly, Formspring, Dropbox, Cupid Media, Zendesk, Snapchat, Clinkle, MeetMe, LastPass (a password security company!) and many others have had to tell users they lost their passwords or payment credentials to hackers. Cyber thieves stole $5 million worth of Bitcoins from Bitstamp, and destroyed Mt. Gox and Flexcoin. Hackers exposed the content and identities of Yik Yak accounts. The CEOs of HB Gary, Snapchat and many other startups have been vilified following the theft and publication of embarrassing emails. Google routinely blacklists websites for weeks due to malware. Appstudio, SendGrid, HB Gary and others have been defaced or even permanently shut down by anti-Western hacktivists for political reasons. For OnlyHonest.com, the damage appears to have been fatal.
And even if your startup beats the odds and survives its infancy without a serious incident, playing catch up later will cost many times more in time, money, reputation and distraction as you change architectures, re-writing code, moving infrastructure, re-imaging laptops, migrating email, and replacing billing systems.
But until your startup can afford a CISO, how do you protect your mission, IP, brand, assets, employees, and capital from cyber threats? For startups with limited resources and intense focus, what’s the right measured response to these threats?
To help our portfolio companies answer these questions, I surveyed Silicon Valley startups to understand their regrets and successes in mitigating cyber losses. I interviewed technical founders, Engineering VPs, CTOs and CISOs to hear what measures they wish they’d taken sooner, or in some cases, later. I also tapped security gurus like Dan Farmer (author, inventor of SATAN), Barrett Lyon (anti-DDoS warrior, hero of Fatal System Error), and Richard Clarke (author, top cyber intelligence officer in the White House and State Department).
I learned that adopting strong security practices is much easier to do when a company is young, while they still enjoy a small attack surface and a manageable number of devices to track. I was encouraged to hear that some basic, affordable practices – both technical and cultural – can mitigate the greatest risks to startups, positioning them well to develop a strong cyber posture as they grow.
So I now advise founders to download and consider these recommendations from Day One, and review the team’s progress quarterly. A secure organization starts at the top with the CEO, but demands a team effort. Whether you’re in a leadership position in finance, engineering, operations or finance, or simply in a position to influence those who are, following this 10-step plan could potentially save your venture.
 Cyber security will remain unsolved for as long as people compete for resources on a planet with digital assets. We face this challenge together, so as you read, please think about what may be missing, and share your feedback. As a VC, I share the entrepreneur’s goal – to minimize the distraction of cyber threats so each startup can focus on its mission. Keep in mind that if you want your venture to make a dent in the world, you can’t let hackers make a dent in you.
Cyber security will remain unsolved for as long as people compete for resources on a planet with digital assets. We face this challenge together, so as you read, please think about what may be missing, and share your feedback. As a VC, I share the entrepreneur’s goal – to minimize the distraction of cyber threats so each startup can focus on its mission. Keep in mind that if you want your venture to make a dent in the world, you can’t let hackers make a dent in you.
