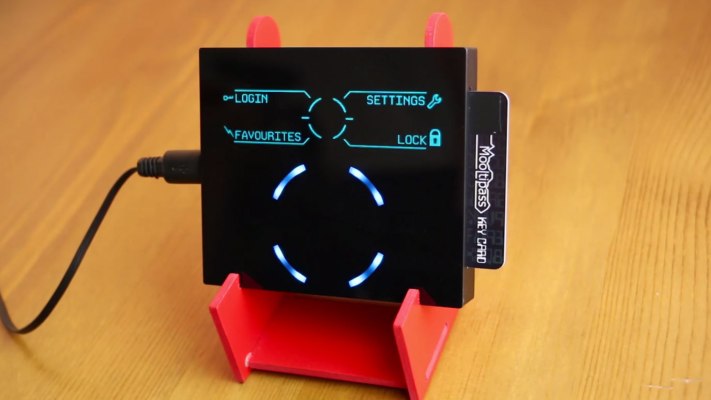
Meet Mooltipass, a device taking aim at the password problem — the problem being we desperately need better passwords to secure our digital stuff but our feeble human minds have trouble remembering enough complex strings to maintain robust security across a range of services.
Mooltipass’ makers reckon the solution to this problem is to AES-256 encrypt and store all your passwords in an offline device, taking the strain out of remembering multiple complex passwords while also promising better security than using password manager software (they claim) — being as the USB hardware device sandboxes your encrypted credentials offline. Ergo they are harder for a hacker to nab.
“Software based password keepers essential keep an encrypted database inside your computer’s memory. To unlock it you’d use a master passphrase. This means that at a given moment, both your passphrase and database are inside your computer’s memory. Therefore, a malicious program could gain access to both and compromise all your credentials at once without you knowing it,” says co-founder Mathieu Stephan.
“I therefore wanted to make a device that would allow users to know when their credentials were accessed, give them full control over their passwords and reduce the number of attack vectors by simply having the Mooltipass type their credentials as a standard keyboard.”
A smartcard and PIN-code is required for each Mooltipass user to manually gain access to their stored credentials so there’s a two-factor authentication layer to help secure the device locally. The box emulates a standard USB keyboard (and does not need driver software to function), plugging in to your computer or mobile device via a USB cable, and allowing it to send the password to the device when prompted for it — and after the user confirms they want their password to be sent to that site.
Increasing control and visibility by informing the user when a site is requesting their credentials is another key aim here, again making it harder for hackers to gain access on the sly, says Stephan.
It’s not impossible for a hacker to sniff a password sent from an offline human input device — given it is still connected to an Internet connected device, so Mooltipass is not perfectly secure, however its makers argue the project’s aim is to “reduce the number of attack vectors to a minimum” and say it’s “as secure as a regular USB keyboard”.
“Perfect security could only be achieved by sharing dedicated secrets or by checking in person public keys with every possible service and website… which is practically impossible to do,” it adds.
Mooltipass will be able to authenticate a user on websites and devices, although its browser plug-in is currently limited to Chrome (and devices need to support plugging in a USB device). Support for other browsers may be developed, depending on how much the crowdfunding campaign raises, according to Stephan.
“Our extension is based on the well accepted chromeipass and we’re asking our beta testers to list the incompatibilities they find… as of today, less than five websites for three months of use,” he adds.
The Switzerland-based team behind the prototype is using Indiegogo to run a crowdfunding campaign, securing Mooltipass pre-orders to be able to bulk manufacture the device. They’re looking to raise just over $100,000 and have passed the half-way mark with another 21 days left on their campaign clock. The device started at $80 to early backers. It’s now stepped up to $140 for an aluminum version.
The project is open source, giving a boost to their security claims — given that all their code is available on Github to be sifted through by interested third parties.
Dev costs thus far have been kept very low, just $6,000 so far, by having a range of contributors working on the open source project for free. Stephan put in the $6k himself and has been helping hand solder the dev units (he has a background in electrical engineering and an existing relationship with a Shenzhen-based product assembler which he’s putting to use). Beta tester units were mostly paid for by the testers themselves, he adds.
Stephan posted about his original idea for Mooltipass on Hackaday, for which he also writes, back in December last year. He points to the myIDkey project as a similar concept when I ask about competitor devices, however that crowdfunded project failed to deliver a properly working product — despite raising some $3.5 million on Kickstarter. The Mooltipass team is evidently intending to avoid a similar fiasco by applying a different development philosophy — by crowdsourcing the expertise of open source enthusiasts as well as cash from backers.
“I thought it’d be a nice idea to create a fully open source security device made by people willing to commit some of their spare time. Over the last year our team therefore fluctuated between 4 and 20 contributors depending on the required tasks (design, mechanics, card art, trivial firmware tasks),” adds Stephan. “They are teachers, engineers, artists, students and security engineers.”
Who is the Mooltipass mostly for? Hopefully both business and consumer web users, says Stephan. “Discussions with our community were intense when choosing our form factor…. we actually asked them to vote for their favorite design. The benefit of our device is that it can be used on locked computers as it is recognized as a standard keyboard and you don’t need to install any additional software. Our display is rather ‘large’ as we wanted people from all ages to have a nice user experience,” he adds.
If it seems like a lot of hassle to carry around a smartcard and a USB gizmo to log into your digital stuff it will be possible to sync credentials across multiple Mooltipasses so you could have one at work and one at home, for instance, meaning all you’re carrying around is the smartcard in your wallet. These are AT88SC102 based smartcards, with a secure element contained on the chip which stores the encryption key for each user’s credentials (meaning one Mooltipass can support multiple users, so long as they each have their own smartcard).
Each Mooltipass ships with two smartcards, but more can be cloned by the user as needed.