ZenGo, a startup that is building a mobile cryptocurrency wallet, has discovered a vulnerability in some of the most popular cryptocurrency wallets, such as hardware wallet Ledger, BRD and Edge.
Named BigSpender, the vulnerability might lead to an incorrect balance on your wallet as unconfirmed transactions are taken into account in your total balance. The attacker could revoke the transaction before it is confirmed, which could lead to some confusion.
Even if you’re not familiar with cryptocurrencies, that type of attack is quite popular on peer-to-peer marketplaces, such as Craigslist.
Let’s say you’re trying to sell a phone. Somebody might tell you that they want to buy your device and send you a fake PayPal transaction email. If you just look at the email, you might think the buyer has already sent you the money. But if you load your PayPal account, you might notice that the buyer never sent you anything — it was a fake payment notification email.
BigSpender could be used in the same way, but with cryptocurrencies. The potential attacker leverages a feature in the bitcoin protocol called Replace-by-Fee. This feature lets you send some bitcoins with a low transaction fee and then send the same crypto assets but with a higher transaction fee.
The original transaction is canceled and replaced with the new one. This way, the new transaction should be confirmed more quickly as miners process transactions with higher transaction fees first.
But some cryptocurrency wallets take unconfirmed transactions for granted a bit too quickly. When you check your balance, it looks like you’ve received some bitcoins, but the sender may have canceled it to replace that transaction with another one to another wallet — a wallet that they control. Even though the transaction has been canceled, the balance still reflects those fake transactions.
If the attacker is trying to fake-buy something really expensive, they can use the BigSpender attack multiple times even if they don’t have a lot of money. For instance, they could initiate 10 transactions each worth 0.1 BTC, the recipient would see a balance of 1 BTC even though they received 0 BTC.
Because the wallet has miscalculated the balance, attackers could also leverage the BigSpender vulnerability to freeze your crypto assets using a denial-of-service attack. When the victim tries to send some bitcoins after receiving a ton of fake transactions, the wallet might try to send crypto assets that never arrived. The transaction fails.
To be clear, your existing bitcoins remain safe. Usually, clearing the app cache and resyncing your wallet with the bitcoin blockchain solves that issue. But you might not understand why you can’t use your crypto assets.
BigSpender isn’t a vulnerability in the bitcoin protocol — it doesn’t let you steal bitcoins. But it can be used to confuse users. Going forward, wallets should clearly mark unconfirmed transactions with a big “pending” label without increasing the balance of the wallet. Transactions that have been replaced using Replace-by-Fee should also be identified as failed.
ZenGo disclosed the vulnerability with Ledger, Edge and BRD 90 days ago. Ledger and BRD have handed bug bounty awards to ZenGo. BRD has released a fix already while Edge and Ledger are working on fixes. ZenGo also released an open-source tool to test your wallet against BigSpender to see the behavior.
Update: Ledger has published a blog post minimizing the impact of BigSpender. The company doesn’t consider it a vulnerability but more as a design flaw — your funds remain safe. “Everything has been fixed in the most recent update that was released two days ago,” VP of Marketing Benoît Pellevoizin told me. Unconfirmed transactions are highlighted, there’s a message next to your balance if there are unconfirmed transactions, and Ledger Live doesn’t use funds from unconfirmed transactions when you’re sending funds by default.
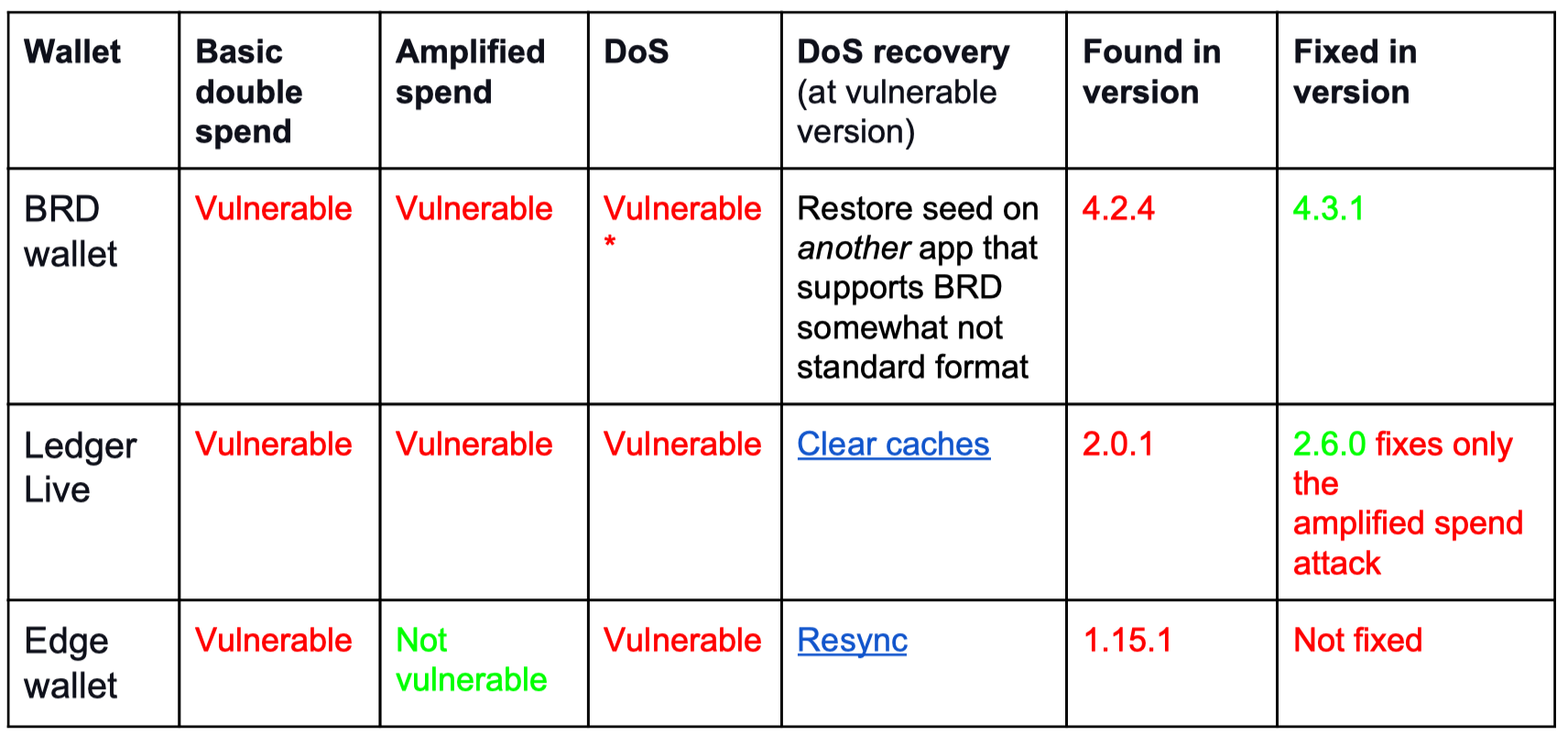
Image Credits: Zengo
