Mattress and bedding giant Tuft & Needle left on an unprotected cloud server hundreds of thousands of FedEx shipping labels containing customer names, addresses and phone numbers.
More than 236,400 shipping labels were found on an Amazon Web Services (AWS) storage bucket without a password, allowing anyone who knew the easy-to-guess web address access to the customer data. Often, these AWS storage buckets are misconfigured by the owner by being set to “public” and not “private.”
The exposed labels were created between 2014 and 2017 during the company’s early years. Tuft & Needle was founded in 2012 in Arizona. But some labels were printed as recently as 2018.
It’s not known for how long the storage bucket was left open.
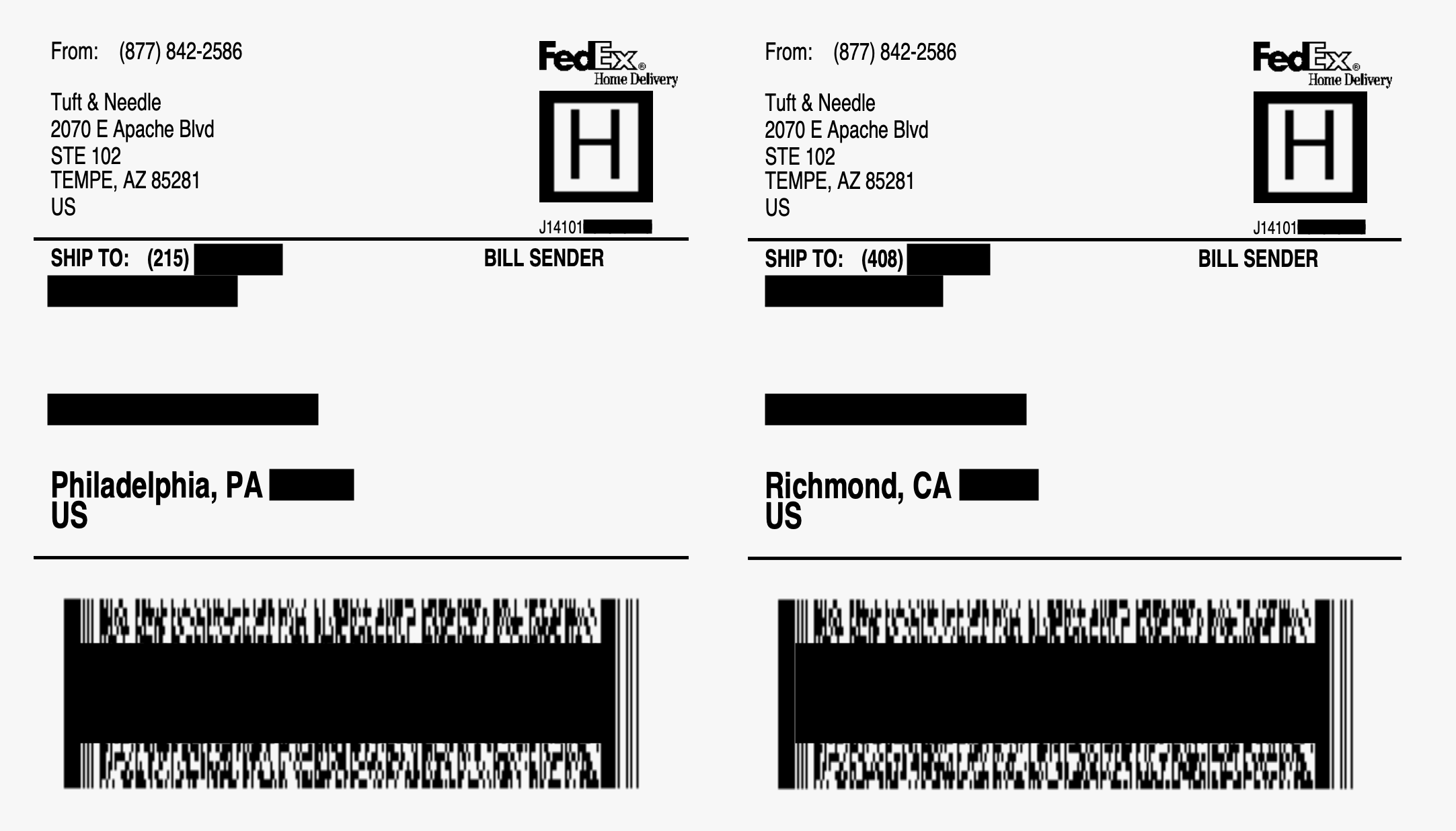
Two customer shipping labels of the hundreds of thousands exposed. We have redacted the shipping labels to protect the customers’ privacy. (Screenshot: TechCrunch)
U.K.-based penetration testing company Fidus Information Security found the exposed data. TechCrunch verified the data by matching names and addresses against public records.
We contacted Tuft & Needle about the data exposure on Monday. The storage bucket was quickly shut down.
“We’ve secured any potential exposure and are investigating the matter further,” said spokesperson Brooke Figlo in an email.
Tuft & Needle said it would “comply” with any applicable state data breach notification laws, but did not explicitly say if the company would inform customers of the security lapse.
