An amateur radio rig exposed to the internet and discovered by a security researcher was collecting real-time medical data and health information broadcast by hospitals and ambulances across U.K. towns and cities.
The rig, operated out of a house in North London, was picking up radio waves from over the air and translating them into readable text. The hobbyist’s computer display was filling up with messages about real-time medical emergencies from across the region. For some reason, the hobbyist had set up an internet-connected webcam pointed at the display. But because there was no password on the webcam, anyone who knew where to look could also see what was on the rig’s computer display.
Daley Borda, a security researcher and bug bounty hunter, stumbled upon the exposed webcam. The live stream was grainy, and the quality of the images so poor that it was just possible to make out the text on the display.
“You can see details of calls coming in — their name, address, and injury,” he told TechCrunch.
TechCrunch verified his findings. Messages spilling across the screen appeared to direct nearby ambulances where to go following calls to the 999 emergency services.
One message said a 98-year-old man had fallen at his home address. A few moments later, another message said a 49-year-old male was complaining of chest pains at a nearby residence. One after the other, messages were flooding in, describing accidents, incidents and medical emergencies, often including their home addresses.
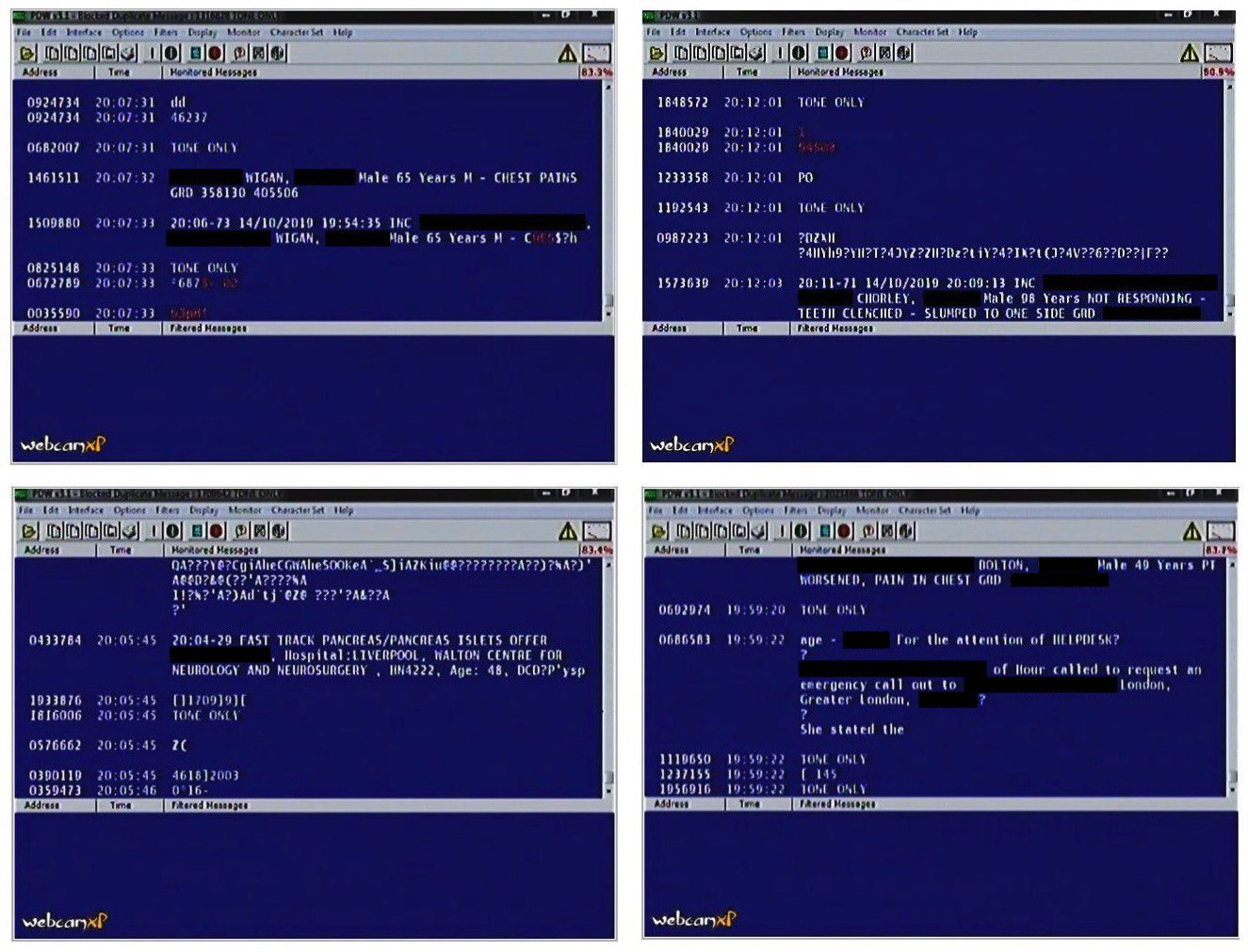
Several screenshots of the amateur radio decoding software, revealing unencrypted pager messages from nearby NHS trusts (Image: TechCrunch)
Borda spends much of his time scouring the internet for things that shouldn’t be online. He looks for exposed databases and devices and, like most other security researchers, privately reports them to their owners. If he’s lucky, the owner takes action. Better yet, they pay out a bug bounty for his efforts.
But he could not figure out who the rig belonged to. TechCrunch contacted the hobbyist’s internet provider to warn of the data exposure.
“Last night we contacted the customer to make them aware that there was a live webcam broadcasting on the open web from their household,” said a spokesperson from the internet provider. “The customer was unaware of the nature of the information being shown so has said that they will stop the feed on that particular camera.”
The hobbyist was picking up and decoding pager communications from a nearby regional National Health Service trust.
“With some cheap, relatively basic, software it is possible for hobbyists to access these frequencies and decode the information being sent, which appears is what has occurred here,” the spokesperson said.
Old but reliable
Pagers — or beepers — may be a relic of the past, but remain a fixture in U.K. hospitals.
These traditionally one-way communication devices allow anyone to send messages to one or many pagers at once by calling a dedicated phone number, often manned by an operator, which are then broadcast as radio waves over the pager network. But pagers still offer benefits where newer technologies, like cell phones, fall down. Because they work a low frequency, pager radio waves are able to travel farther and deeper inside large buildings — particularly hospitals — which have thickened walls to protect others from X-rays and other radiation. Pagers also work across long distances, including in cell service dead-spots.
But few were thinking about message security when pager use was at its peak.
“They aren’t secure,” Andy Keck, an electronics and amateur radio hobbyist, told TechCrunch. Keck said messages sent over the pager network are encoded when they are converted into a burst of radio waves and broadcast over the air.
“But people don’t necessarily understand the difference between encryption and encoding,” he said.
Because the two widely used pager protocols — POCSAG and FLEX — are not encrypted, it’s easy to understand what messages are broadcast over the airwaves using free and open-source software.
For years one of the largest barriers to intercepting and decoding pager messages — or any other radio waves — was that hobbyists needed custom, often expensive hardware. But with the advent of software-defined radios, most hobbyists can get by with a $20 plug-in dongle and an antenna.
“It’s just enter the command to start the application, sit back, and start decoding in real time on the screen,” he said.
130,000 NHS pagers
Although the number of pagers has dropped to near-zero from their height in the 1980s, pagers still carry a considerable amount of information every day.
Pager messages can travel over a large distance, said Keck, depending on how high the transmitter is located. Most major cities are covered with some pager service. Given the geography of the U.K., amateur radio hobbyists can often pick up pager messages from different sources.
The NHS still uses about 130,000 pagers, according to the U.K. government’s latest count, or about 10% of the world’s current pagers in use. But the NHS has been told to stop using pagers altogether by 2021.
But it’s not clear how many trusts are exposing medical information — if at all. According to NHS spokesperson Oliver Michelson, “each NHS organization is responsible for its own IT equipment and security.”

Pagers receive encoded, but not encrypted messages (Image: Getty Images)
One NHS trust we spoke to said they had around 1,600 pagers and are managed by the trust. (We are not naming the trust, as it would expose their communications.) When asked if the trust was aware that pager messages are not encrypted and can be intercepted by amateur radio hobbyists, the spokesperson responded: “Yes.”
Another trust we spoke to said they were “aware” that the handful of pagers it operates do not encrypt their messages. The trust said their pagers were managed by a third-party.
PageOne, the last remaining pager network in the U.K., says in a brochure that its pager service can deliver “real-time messaging cost effectively and securely to their staff.”
But a spokesperson told TechCrunch: “PageOne ensures customers are aware of the ability to intercept messages in its terms and conditions” and that encrypted services “are available if required.”
The company said the majority of NHS pagers are operated on private pager networks operated by the trusts themselves.
‘Trivially interceptable’
Amateur radio hobbyists know all too well the risks posed by unencrypted pagers.
Over the years there have been numerous headlines of hobbyists picking up signals from nearby hospitals, including patients’ names and medical information. Some have even turned eavesdropping on hospital pagers into an art project.
Last month, hospitals in Vancouver were found broadcasting unencrypted patient medical data across the city.
Sarah Jamie Lewis, executive director at Open Privacy, who first revealed the issue, said the hospital pager messages were “trivially interceptable” by anyone nearby.
“It tends to be pretty common knowledge in the amateur radio community that these kind of broadcasts are going on but it’s only recently that we started seeing a culture of disclosure,” said Lewis.
In the U.K., it’s legal for amateur radio hobbyists to scan the airwaves but unlawful to disclose the contents of messages. That’s put some security-focused hobbyists who disclose exposed sensitive messages in a tough legal spot.
“You get this horrible situation where not disclosing is bad, but people have a right to know that their health data is being breached,” said Lewis.
But the penalties could be far steeper for organizations that expose sensitive health data. Exposing personally identifiable and health information violates GDPR, the Europe-wide data protection laws that came into force last year. Organizations can be fined heavily for breaching the rules.
With more than a year on the clock before the NHS pager ban comes into effect, it’s not a problem that can be easily fixed.
The obvious solution would be not to send sensitive health or medical data over pager messages. Clearly, as seen by the amateur hobbyist’s radio rig, that message isn’t getting through.
Got a tip? You can send tips securely over Signal and WhatsApp to +1 646-755-8849. You can also send PGP email with the fingerprint: 4D0E 92F2 E36A EC51 DAAE 5D97 CB8C 15FA EB6C EEA5.
