Here we go again. Western governments are once again dialing up their attack on end-to-end encryption — calling for either no e2e encryption or backdoored e2e encryption so platforms can be commanded to serve state agents with messaging data in “a readable and usable format.”
U.S. Attorney General William Barr, acting U.S. Homeland Security Secretary Kevin McAleenan, U.K. Home Secretary Priti Patel and Australia’s minister for home affairs, Peter Dutton, have co-signed an open letter to Facebook calling on the company to halt its plan to roll out e2e encryption across its suite of messaging products. Unless the company can ensure what they describe as “no reduction to user safety and without including a means for lawful access to the content of communications to protect our citizens,” per a draft of the letter obtained by BuzzFeed ahead of publication later today.
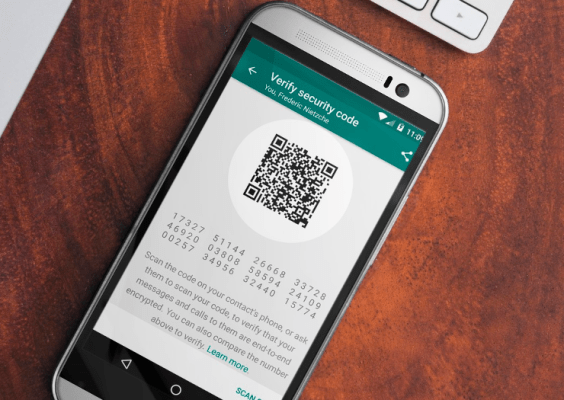
If platforms have e2e encryption, a “means for lawful access” to the content of communications sums to a backdoor in the crypto — presumably along the lines of the “ghost protocol” that U.K. spooks have been pushing for the past year. AKA an “exceptional access mechanism” that would require platforms CC’ing a state/law enforcement agent as a silent listener to eavesdrop on a conversation on warranted request.
Facebook-owned WhatsApp was one of a number of tech giants joining an international coalition of civic society organizations, security and policy experts condemning the proposal as utter folly earlier this year.
The group warned that demanding a special security hole in encryption for law enforcement risks everyone’s security by creating a vulnerability which could be exploited by hackers. Or indeed, service providers themselves. But the age-old “there’s no such thing as a backdoor just for you” warning appears to have fallen on deaf ears.
In their open letter to Facebook, the officials write: “Companies should not deliberately design their systems to preclude any form of access to content, even for preventing or investigating the most serious crimes. This puts our citizens and societies at risk by severely eroding a company’s ability to detect and respond to illegal content and activity, such as child sexual exploitation and abuse, terrorism, and foreign adversaries’ attempts to undermine democratic values and institutions, preventing the prosecution of offenders and safeguarding of victims. It also impedes law enforcement’s ability to investigate these and other serious crimes.”
Of course, Facebook is not the only messaging company using e2e encryption, but it’s in the governments’ crosshairs now on account of a plan to expand its use of e2e crypto — announced earlier this year, as part of a claimed “pivot to privacy.” And, well, on account of it having two billion+ users.
The officials claim in the letter that “much” of the investigative activity, which is critical to protecting child safety and fighting terrorism, “will no longer be possible if Facebook implements its proposals as planned.”
“Risks to public safety from Facebook’s proposals are exacerbated in the context of a single platform that would combine inaccessible messaging services with open profiles, providing unique routes for prospective offenders to identify and groom our children,” they warn, noting that the Facebook founder expressed his own concerns about finding “the right ways to protect both privacy and safety.”
In March, Mark Zuckerberg also talked about building “the appropriate safety systems that stop bad actors as much as we possibly can within the limits of an encrypted service.”
Which could, if you’re cynically inclined, be read as Facebook dangling a carrot to governments — along the lines of: “We might be able to scratch your security itch, if your regulators don’t break up our business.”
Ironically enough, the high-profile intervention by officials risks derailing Facebook’s plan to unify the backends of its platforms — widely interpreted as a play to make it harder for regulators to act on competition concerns and break up Facebook’s business empire along messaging product lines: Facebook, WhatsApp, Instagram.
Or, well — alternative scenario — Facebook could choose to strip e2e crypto from WhatsApp, which is currently the odd one out in its messaging suite on account of having proper crypto. Governments would sure be happy if it did that. But it’s the opposite of what Zuckerberg has said he’s planning.
Curiously, the draft letter makes no mention of platform metadata. Which is not shielded by even WhatsApp’s e2e encryption. And thus can be extracted — via a warrant — in a readable format for legit investigative purposes. And let’s not forget U.S. spooks are more than happy to kill people based on metadata.
Instead the officials write: “We must find a way to balance the need to secure data with public safety and the need for law enforcement to access the information they need to safeguard the public, investigate crimes, and prevent future criminal activity. Not doing so hinders our law enforcement agencies’ ability to stop criminals and abusers in their tracks.”
The debate is being framed by spooks and security ministers as all about content.
Yet a scrambled single Facebook backend would undoubtedly yield vastly more metadata, and higher-resolution metadata, on account of triangulation across the services. So it really is a curious omission.
We’ve reached out to Facebook for its reaction to the letter. BuzzFeed reports that it sent a statement in which it strongly opposes government attempts to build backdoors. So if Facebook holds firm to that stance it looks like another big crypto fight could well be brewing. À la Apple versus the FBI.
Update: Facebook has now sent us this statement:
We believe people have the right to have a private conversation online, wherever they are in the world. As the US and UK governments acknowledge, the CLOUD Act allows for companies to provide available information when they receive valid legal requests and does not require companies to build backdoors.
We respect and support the role law enforcement has in keeping people safe. Ahead of our plans to bring more security and privacy to our messaging apps, we are consulting closely with child safety experts, governments and technology companies and devoting new teams and sophisticated technology so we can use all the information available to us to help keep people safe.
End-to-end encryption already protects the messages of over a billion people every day. It is increasingly used across the communications industry and in many other important sectors of the economy. We strongly oppose government attempts to build backdoors because they would undermine the privacy and security of people everywhere.
Bilateral Data Access Agreement
In another announcement being made today, the U.K. and the U.S. have signed a “world first” Bilateral Data Access Agreement that’s intended to greatly speed up electronic data access requests by their respective law enforcement agencies.
The agreement is intended to replace the current process, which sees requests for communications data from law enforcement agencies submitted and approved by central governments via a process called Mutual Legal Assistance — which can take months or even years.
Once up and running, the claim is the new arrangement will see the process reduced to a matter of weeks or even days.
The agreement will work reciprocally with the U.K. getting data from U.S. tech firms, and the U.S. getting access from U.K. communication service providers (via a U.S. court order).
Any request for data must be made under an authorisation in accordance with the legislation of the country making the request and will be subject to independent oversight or review by a court, judge, magistrate or other independent authority, per the announcement.
The U.K. also says specifically that it has obtained “assurances” which are in line with the government’s continued opposition to the death penalty in all circumstances. Which is only mildly reassuring given the home secretary’s previous views on the topic.
The announcement also makes a point of noting the data access agreement does not change anything about how companies can use encryption — nor prevent them from encrypting data.
For interfering with proper encryption the plan among this trio of signals intelligence allies is, seemingly, to reach for the old PR lever and apply public pressure. So, yeah, here we go again.