Why is one of the most popular Android apps running a hidden web server in the background?
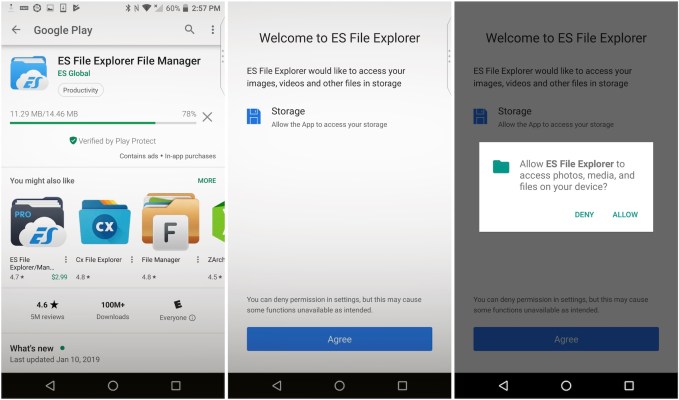
ES File Explorer claims it has more than 500 million downloads under its belt since 2014, making it one of the most used apps to date. Its simplicity makes it what it is: a simple file explorer that lets you browse through your Android phone or tablet’s file system for files, data, documents and more.
But behind the scenes, the app is running a slimmed-down web server on the device. In doing so, it opens up the entire Android device to a whole host of attacks — including data theft.
Baptiste Robert, a French security researcher who goes by the online handle Elliot Alderson, found the exposed port last week, and disclosed his findings in several tweets on Wednesday. Prior to tweeting, he showed TechCrunch how the exposed port could be used to silently exfiltrate data from the device.
“All connected devices on the local network can get [data] installed on the device,” he said.
Using a simple script he wrote, Robert demonstrated how he could pull pictures, videos and app names — or even grab a file from the memory card — from another device on the same network. The script even allows an attacker to remotely launch an app on the victim’s device.
He sent over his script for us to test, and we verified his findings using a spare Android phone. Robert said app versions 4.1.9.5.2 and below have the open port.
“It’s clearly not good,” he said.
A script, developed by a security researcher to obtain data on the same network as an Android device running ES File Explorer. (Image: supplied)
We contacted the makers of ES File Explorer but did not hear back prior to publication. If that changes, we’ll update.
The obvious caveat is that the chances of exploitation are slim, given that this isn’t an attack that anyone on the internet can perform. Any would-be attacker has to be on the same network as the victim. Typically that would mean the same Wi-Fi network. But that also means that any malicious app on any device on the network that knows how to exploit the vulnerability could pull data from a device running ES File Explorer and send it along to another server, so long as it has network permissions.
Of the reasonable explanations, some have suggested that it’s used to stream video to other apps using the HTTP protocol. Others who historically found the same exposed port found it alarming. The app even says it allows you to “manage files on your phone from your computer… when this feature is enabled.”
But most probably don’t realize that the open port leaves them exposed from the moment they open the app.