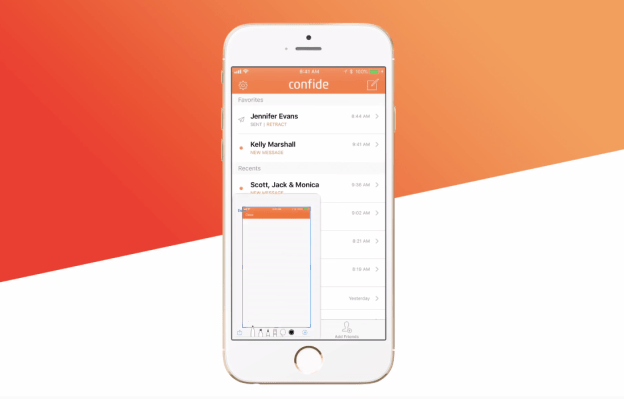
Messaging app Confide, which was last year touted as a popular choice in Trump’s White House for staff wanting to leak intel to the press, has added protection against screenshotting to its iOS app.
The iOS app previously put some limitations on how users could screenshot contents when using the app — but full anti-screenshotting tech was limited to its Android app.
Not anymore, says co-founder Jon Brod. “ScreenShield is a collection of several different technologies that work together to prevent various screenshots and screen recording techniques,” he says, discussing the new feature.
“There are many ways to capture a screenshot or make a screen recording on iOS, and each method requires different handling. One of the newest prevention technologies that we added to our toolkit utilizes the same content protection APIs already used by Netflix, iTunes Movies, and other video streaming apps. We have built upon the underlying technology to prevent capture of other media types including text, photos, documents, stickers, and more. Importantly, we are only using public iOS APIs in our ScreenShield technology.”
Anti-screenshotting technology like this is really just security theatre, of course.
Not least because all it takes is a second device, unconnected but in close proximity to the first, to snap away and record its on-screen contents regardless.
Even so, Brod claims there’s still value in the feature, despite such an obvious loophole. “While nothing is 100% foolproof, we believe the combination of our end-to-end encryption, ephemerality, and now complete screenshot-prevention makes Confide the most private and secure messenger available,” he claims.
However rather more serious charges of flawed security were leveled at the messaging platform last March — when researchers demonstrated it was possible to intercept encrypted Confide messages, and claimed the platform could in fact decrypt and read users’ missives (rather undermining its end-to-end encryption claim).
Asked about this now, Brod says all the security issues raised by the researchers were addressed “in a timely fashion as soon as they were reported to us last year”.
“Confide implemented safety codes, which are a cryptographic hash that includes all public encryption keys for an account. Users can validate the keys used by Confide‘s end-to-end encryption by ensuring that the safety code displayed on their device matches the one displayed on their contacts’ device. We also allow users to be notified if the safety code for one of their contacts changes,” he tells us.
“We also underwent a comprehensive third-party security audit including blackbox, greybox and whitebox testing, covering both the client and server. The executive summary of the audit is published on our site.”
And while a third-party audit is a welcome development, the presence of such serious flaws in Confide’s crypto implementation in the first place remains concerning.
And for anyone with ongoing concerns about the robustness of its crypto, other end-to-end encrypted messaging apps are available.