
Eric Stapelfeld, the fishing guide
Cape Cod fishing guide Eric Stapelfeld trusted me to look after his website the same way that I trust him to find fish. Until a few weeks ago, I believed I had the easier part of the bargain. After all, what’s hard about maintaining a simple WordPress site with a phone number and lots of striped bass pictures? As it turns out, everything is hard, really hard, when hackers go to work on a vulnerable site — even a simple one. And no fish ever put up a fight like the malware that took over Eric’s site.
The story began last fall, when Eric called me in San Francisco to report that “some guy” had called to complain about fraud on his site.
“Yeah, like the guy said somebody is running a business inside the website and ripped him off. Said he knows it’s not my fault but I should know about it.”
Eric doesn’t sell anything on his site. It consists of posts about fishing and a phone number to book trips. No hacker would bother with a site like that, right?
“Hey forget about it,” I told Eric. “There’s no way your site could rip anyone off. I have no idea what the guy is talking about.”
That was more true than I realized. Three months later, I got another call from Eric. “Hey, Google is fucking with my site,” he said. “My friends are calling me and saying something is wrong.”
As soon as I typed in www.hairballcharters.com, Google dropped a screaming red screen warning that read: “The site ahead contains malware. Attackers currently on www.hairballcharters.com might attempt to install dangerous program on your Mac that steal or delete information (for example, photos, passwords, messages, and credit cards).”
“Oh crap,” I thought. Maybe there was something more to that guy who called Eric.
My first move was to call customer service at Deluxe Hosting, where the site is hosted, and get them to open a ticket. After a few email exchanges, I realized that they were unlikely to sort out the problem. They found malware and said they deleted some of it, but Google was still showing a warning. After a few exchanges, Deluxe stopped responding.
Next I got in touch with Jennifer Zelazny, the WordPress developer who set up the site and had worked on it from time to time. She agreed to dive in.
What she found was nasty. Hackers had accessed the site either directly through WordPress or through a plug-in on the site. She found at least 20 suspicious WordPress core files. There were also non-core files on the site with file names like “list.php” and “apis.php,” which to an average user might not have raised any red flags. Their names looked typical, but the time stamps were all recent — since July 2016 — and upon further inspection revealed redirects to other sites. She deleted the files, reset passwords, updated the secret keys in the wp-config, cleaned up other valid files with malicious code and then ran scans with Exploit Scanner and Sucuri SiteCheck scanner to ensure she found every bit of malware.
Jennifer asked me if I had a Google Webmaster account so we could request that Google scan the site and give it a clean bill of health. I had not claimed the site before, so I went through the steps. Google provided a code snippet to drop into the site’s markup as a means to authenticate that I was in fact the owner of the site. Jennifer followed up; not long afterwards, Google admitted me to the account.
To my horror, there were already two other email addresses listed as owners of the site. They were really sketchy email addresses, like ones you’d make up if you were up to no good.
I looked around in the Google webmaster account and saw that the hackers had filed 47 sitemaps and submitted 565,192 web pages, of which 229,837 had been indexed by Google.
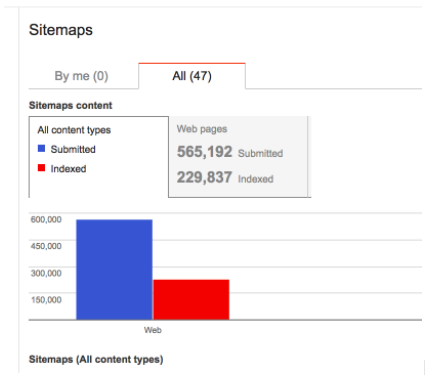
In case you’re wondering, Eric’s site has 130 web pages, most of which feature a picture of an impressive striped bass caught off Falmouth on Cape Cod.
It appears that the hackers were using the malware to insert links in Eric’s site and using the site map to create some kind of dynamic set of redirects. But that’s just a guess, and there may be a better explanation.
Neither of us was crazy about following the links. The hacker had created more than 47 separate sitemaps using links/redirects from the site — all averaging 70,000 lines of code each (that’s a lot of URLs!) The URLs all looked similar in their format:
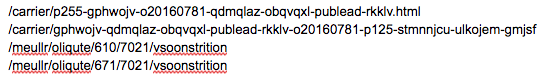
And this example of the result on a Google search results page — needless to say, Hairball Charters does not have any business extensions in Japan:
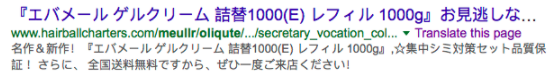
By looking at this cached page, it’s pretty easy to imagine what was happening. In this case, the hackers had set up an e-commerce site targeted at Japanese consumers.
Google’s tools made it easy to kick the invaders out of the account. Google shows the tag associated with each registered account for the site, so I passed those to Jennifer, who deleted them from the mark-up. In an instant, the hackers’ access was gone. Then I gave Jennifer access to the account and she deleted all the fake sitemaps. Jennifer told me that she had worked on a lot of compromised sites, but this was the first time she had seen hackers take over the Google webmaster account in order to manipulate the sitemaps.
Jennifer updated the security patches for WordPress and all the plug-ins and implemented steps to make sure updates take place automatically in the future. We also set up two-factor authentication to access the site.
I always knew that it was important to keep patches up-to-date, but until now I did not know why an out-of-date site was so vulnerable. Jennifer explained that every time WordPress or any developer with an important WordPress plug-in becomes aware of a vulnerability, they usually document the vulnerability at the same time that they issue the security patch. (Here is a WordPress example and a Sucuri example.) Once that documentation goes public, hackers immediately scan WordPress sites to find exploits. Get there late and you get nailed. Sorry to say, that was Hairballcharters.com.
Avoiding situations like Hairball’s is a lot more simple than dealing with the aftermath of a hack. Here is Jennifer’s five-step program to good security on a WordPress site.
Step one: Stay up-to-date with WordPress core upgrades. This is beyond simple: Insert one line of code — define( ‘WP_AUTO_UPDATE_CORE’, minor ) — in the wp-config.php file and your site will always auto update. (Here is the documentation.)
Step two: Keep your WordPress plug-ins up-to-date. The Jetpack plugin makes this straightforward; just use the Jetpack Manage option to select the plug-ins you want updated as soon as patches become available.
Step three: To make your site extra secure, consider the plug-in Sucuri Security: Auditing, Malware Scanner and Security Hardening, which allows you to do exactly what the name suggests. You can enable auditing to send immediate notifications if any files are modified, plug-ins are enabled/disabled and much more.
Step four: Install two-factor authentication for access to your WordPress site.
Step five: Claim your site in the Google Webmaster tool and check in from time to time to make sure your site has no content or sitemap errors — or stealthy invaders populating sketchy sitemaps.
As for HairballCharters.com, the site is back in good order and Eric is happy that Google’s big red screen is now gone. If you happen to be out Cape Cod way this summer, he would love to take you fishing and trash-talk two of his favorite topics: my fishing and my security smarts.
With Jennifer Zelazny