The U.K. government has today published a draft bill setting out new surveillance powers that if passed into law will allow the security and intelligence agencies to more deeply probe Brits’ digital activity by requiring U.K. ISPs keep a log of all the websites visited by Internet users over the past 12 months.
Brits’ media consumption habits, banking activity, political affiliations, health concerns, sexual proclivities and more could all potentially be inferred from state mandated Iogging of Internet activity under the proposed new legislation.
The Investigatory Powers Bill was introduced to Parliament by Home Secretary Theresa May earlier today, who said the government hopes to have an amended bill introduced next spring, following a Parliamentary and committee scrutiny process — with the aim of getting a final bill onto the statue books before the end of 2016.
Speaking in Parliament ahead of May, Prime Minister David Cameron said the new powers are required to help the police and security services combat crime in an era of social media.
May went on to describe the aim of the bill as being to draft a new law “consolidating and updating our investigatory powers, strengthening the safeguards and establishing a world leading oversight regime”.
The government confirmed its intention to legislate to plug what it termed “capability gaps” in law enforcement and security agencies’ intelligence gathering abilities in the digital era back in May. It is tabling legislation now with a view to replacing DRIPA — aka the existing ’emergency’ surveillance legislation which was rushed through Parliament back in 2014, and which has a sunset clause meaning it will expire at the end of 2016.
DRIPA was criticized both for the draconian data capture powers it afforded, and also for the unseemly haste with which it was railroaded through Parliament — allowing no time for proper Parliamentary scrutiny. The Investigatory Powers bill will at least get the latter, with a special committee of MPs due to pore over its detail in the coming months.
Despite criticisms of the potential chilling effect on the U.K. tech sector of draconian state surveillance powers, at a time when European institutions have generally been seeking to roll back data retention capabilities and bolster privacy protections for individuals in the post-Snowden era, the U.K. government is nonetheless pushing ahead with a bid to cement and expand the powers of the surveillance state by enshrining mass surveillance as ‘due process’ for domestic intelligence agencies and proposing what critics have dubbed another ‘Snooper’s Charter’.
The government has of course been attempting to spin otherwise — by, for example, claiming mass surveillance (euphemistically referred to as “bulk collection”) is “proportionate and necessary” in today’s modern digital era, and explicitly stating it is not seeking to ban encryption. Albeit that any ban on encryption would likely be impossible to enforce — especially without international agreement, given how much technology is developed and distributed by non-U.K. companies.
On the encryption point, earlier this year Cameron had made comments widely interpreted as an intention by a future Conservative majority government to outlaw the technology. In the event today’s draft bill does not apparently seek to explicitly outlaw encryption but May said the requirement that is currently in secondary legislation — “that those companies that are issued with a warrant should take reasonable steps to be able to respond to that warrant in unencrypted form” — is being brought “onto the face of the legislation”.
So it remains to be seen whether a company that runs a service under end-to-end encryption and then, if served with a warrant, fails to deliver unencrypted data because they are unable to do so is considered to be breaking U.K. law or not.
On this front, clause 189(4)(c) also appears pertinent — as it sets out that specific obligations on “relevant operators” can include: “obligations relating to the removal of electronic protection applied by a relevant operator to any communications or data” — which appears to suggest a requirement that companies are able to remove encryption when asked. But of course encryption that can be removed is not end-to-end encryption (a technology the U.K. government recently described as “alarming”).
“But we are not banning encryption,” claimed May in Parliament. “We recognize that encryption plays an important part for people in keeping their details secure.”
(It also appears the government recognizes that encryption can play an important role in its new legislation being perceived as more moderate than it could otherwise have been… )
May went on to emphasize that other contentious measures — included in the earlier 2012 Communications Data bill (also dubbed a Snoopers’ Charter), which failed to pass Parliament — have been dropped.
“The draft bill we are publishing today is not a return to the draft Communications Data bill of 2012. It will not include powers to force U.K. companies to capture and retain third party Internet traffic from companies based overseas; it will not compel overseas communications service providers to meet our domestic retention obligations for communications data,” she said.
Despite this, the requirement that Internet and phone companies retain data on the websites users have visited for a full 12 months remains a huge and intrusive expansion of state surveillance powers. Civil rights organization Big Brother Watch sums up this data as “the what and how of the way we live our lives”.
May said it is not a full browsing history, in the sense of logging every click of and page visited by an Internet user, but rather will be a timestamped record of the primary website URL visited. Which still of course generates a hugely intrusive personal history of U.K. web users — or at least those who don’t actively seek to avoid this state-mandated dragnet by using a VPN/proxy, such as the Tor browser, to protect their privacy, or running other obfuscation technologies to muddy the waters of their Internet activity.
The provision is described as an “Internet Connection Record” (ICRs) in the bill, and May likened it to “the modern equivalent of an itemized phone bill”. However it’s clear that far more activity now occurs digitally than does or ever did via voice calls — so the comparison is a stretch.
“Some have characterized this power as law enforcement having access to people’s full web browsing histories. Let me be clear: this is simply wrong,” said May. “[It] is a record of every communication service that a person has used, not a record of every webpage they have accessed.”
Requests for this data from law enforcement agencies would be “for the purpose of determining whether someone had accessed a communications website, an illegal website or to resolve an IP address where it is necessary and proportionate to do so in the course of a specific investigation”, she added. “Strict limits will apply to when and how that data can be accessed.”
Quite how the bulk collection of U.K. users’ Internet browsing activity will be squared with European data protection legislation, currently being drafted with a new data protection directive set to be introduced later this year — which may place competing requirements on ISPs when it comes to user data retention — remains to be seen. (Assuming, of course, the U.K. does not vote to leave the EU in its referendum next year.)
A new criminal offence of “wilfully or recklessly acquiring communications data”, carrying a maximum two-year prison sentence, is being created with the aim of discouraging access abuse of these ICRs. However, given how many data breaches are perpetrated by hackers already — such as the recent data breach of UK ISP TalkTalk, with police arresting several teenagers on suspicion of being behind that attack — it remains to be seen how much of a disincentive a two-year jail sentence is. Not to mention how securely ISPs will store this sensitive data.
Raising the latter point in Parliament, Shadow Home Secretary Andy Burnham noted that the Home Secretary’s introductory speech had referenced how some 90 per cent of commercial organizations have experienced a data breach, and went on to query whether there might not therefore be risks to storing U.K. citizens’ website access data — asking specifically whether it will not therefore be stored in “anonymized form” to safeguard the privacy of the public from hack attacks.
May sidestepped this question, reiterating only that more powers are needed by law enforcement to combat cybercrime. “I think it’s very simple, that as criminals are moving into more online crime that actually we need to make sure that our law enforcement agencies have the power to be able to deal with that cybercrime,” she said.
Police will require warrant authorization to access ICR data, while local councils will be explicitly banned from accessing it. But even with the check of a warrant, the U.K. government affording law enforcement access to web browsing data remains exceptional when compared to powers afforded to police in the U.S. and elsewhere in Europe.
Existing rules allowing U.K. police forces to access communications metadata without a warrant remain unchanged. Earlier this year Big Brother Watch published data obtained via FOI detailing the extent of police forces’ comms data requests in that regard — with some 733,000 requests made by domestic U.K. police forces over a three year period, between 2012 and 2014.
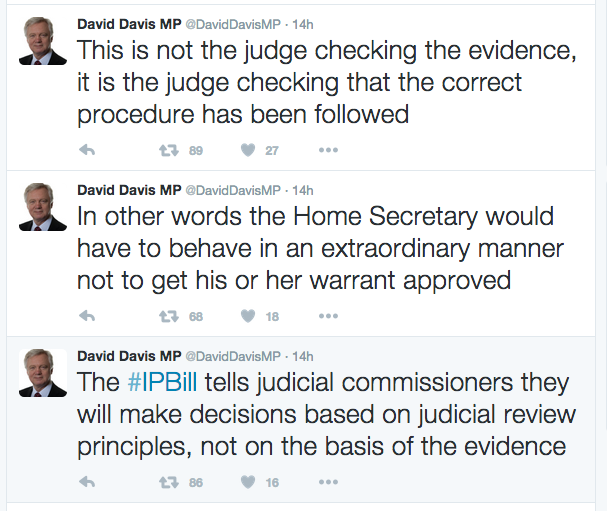
On judicial oversight for signing off surveillance warrants — a key recommendation of the independent terrorism legislation reviewer, David Anderson, in his report this summer — the Home Secretary is proposing a third way, with senior ministers and judges both involved in sign off. She referred to this as a “double lock”, claiming it offers “both the reassurance of democratic accountability and judicial accountability”.
“As now the Secretary of State will need to be satisfied that an activity is necessary and proportionate before a warrant can be issued but in future the warrant will not come into force until it has been formally approved by a judge,” she said. “This will place a double lock on the authorization of our most intrusive investigatory powers.”
Anderson’s recommendation that the power to sign off warrants be taken away from ministers and handed over to judicial oversight entirely has, however, been rejected — leaving the U.K. still somewhat at odds with other ‘Five Eyes’ allies and countries elsewhere in Europe where judges are solely responsible for authorizing surveillance.
Commenting on this aspect of the bill, Ben Emmerson, the UN special rapporteur on counter terrorism and human rights, argued that the U.K. will remain out of step with international standards if judges are not fully empowered to sign off warrants.
“Prior authorisation by an independent and impartial judiciary is an essential safeguard. Empowering judges to weigh the balance between the competing interests at stake would bring the UK legislation into full compliance with the requirements of international law, and in particular Article 17 of the International Covenant on Civil and Political Rights. Judicial review after the event is better than no judicial review at all, but it falls short of the requirement to place the power to issue a warrant into the hands of an independent judge, which is where it belongs,” he wrote.
It is also noteworthy that it does also remain possible under the current draft bill for a senior minister to rubberstamp warrants on their own.
May clarified that it would be possible for the Home Secretary to authorize an “urgent warrant to come immediately into effect”, to avoid too much delay being caused by her double lock — with the warrant then subsequently reviewed by the panel of judges to determine whether the warrant should continue or not. However she added that in “most circumstances” there would be a double authorization for warrants.
Another portion of the draft bill involves clarifying oversight rules for surveillance powers. A senior judge will be appointed as the overseeing commissioner, said May.
“I am clear we need a significantly strengthened regime to govern how these powers are authorized and overseen. So we will replace the existing oversight with a powerful and independent Investigatory Powers Commissioner. This will be a senior judge, supported by a team of expert inspectors with the authority and resources to effectively and visibly hold the intelligence agencies and law enforcement to account,” she told Parliament.
More broadly, the bill seeks to enshrine mass surveillance as a lawful modus operandi for U.K. security and intelligence agencies that have already been using such digital dragnets for years, enabled by a lack of scrutiny and via arcane existing investigatory legislation (such as RIPA and section 94 of the Telecommunications Act 1984).
The ability for police and security agencies to use hacking (aka “equipment interference”) as an investigatory tool is also being enshrined in law.
The bill refers to “bulk data” as “a vital tool in discovering new targets and identifying emerging threats”. And says a “clear statutory framework” will be provided for “all of the bulk powers available to the security and intelligence agencies”, in addition to introducing “robust, consistent safeguards across all of those powers”.
Responding to the draft bill in a blog post, the government’s independent terrorism legislation reviewer said the best thing about the bill is the light finally being shone onto the operations of the U.K.’s security apparatus.
“For the first time, we have a Bill that sets out, for public and political debate, the totality of the investigatory powers used or aspired to by police and intelligence agencies,” writes Anderson, going to list some examples.
“Not everyone will be happy about those powers. It will now be for Parliament to decide whether they are justified. That is the way things should be in a democracy — but rarely are at the moment, anywhere in the world. Whatever the content of the eventual UK law, it will no longer be possible to describe it as opaque, incomprehensible or misleading.”
