Well, that was fast! Only days after the first public jailbreak for iOS 9 devices hit the web, it appears that Apple has closed two of the exploits used by the Chinese hacking team Pangu, whose untethered jailbreak allowed users to jailbreak nearly all iPhone, iPad and iPod touch devices running iOS versions 9.0 through 9.0.2.
In a security document posted on Apple’s website, the Cupertino company credits Pangu with discovering two vulnerabilities in the iOS operating system that have now been patched.
These include one vulnerability that would allow a malicious application to elevate privileges, and another that would allow a malicious application to execute arbitrary code with kernel privileges.
The jailbreaking community already knew that Apple had patched these exploits in iOS 9.1. After all, the jailbreak didn’t work with the beta build of the iOS 9.1 software. That’s likely why the Pangu team pushed their iOS 9 jailbreak out the door just ahead of the iOS 9.1 release – it was the only way to get it into the hands of end users before it was too late.
However, this doesn’t mean that you’ll never be able to jailbreak your device again if you already accidentally upgraded to 9.1. There’s always the chance that the Pangu team or another hacker will find a different vulnerability to exploit in the future.
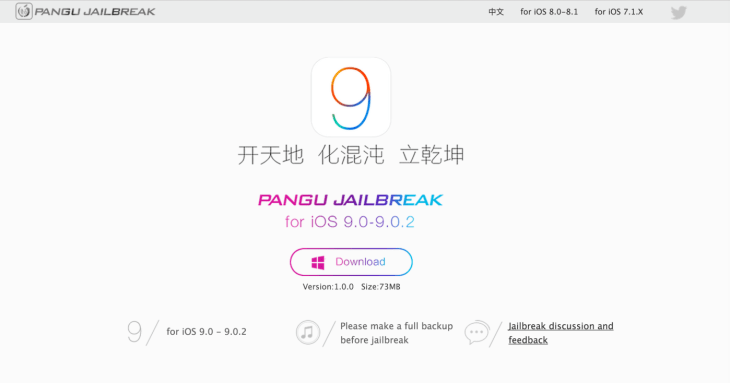
Just ahead of this news and the 9.1 release this morning, the Pangu team rolled out a new version of their jailbreak tool (version 1.1.0), which was more stable and saw better results, they claimed. However, that tool was still focused on offering users the ability to jailbreak devices running up to iOS 9.0.2. The team has not said yet if it has a 9.1 hack in the works.
If you were thinking about jailbreaking and still want to do it, the lesson here is to stay away from 9.1. However, although there are a number of cool apps and tweaks you can now take advantage of as a jailbreaker, also be aware that you’re exposing yourself and your personal data to security risks in the process.