Over the years, Apple has introduced features to its mobile operating system, iOS, that made jailbreaking your device in order to customize and tweak your phone or tablet less appealing. Users now can do things like add widgets, install dynamic (moving) wallpapers, send audio messages, quickly access frequently used controls and, thanks to 3D Touch, invoke shortcuts to installed applications.
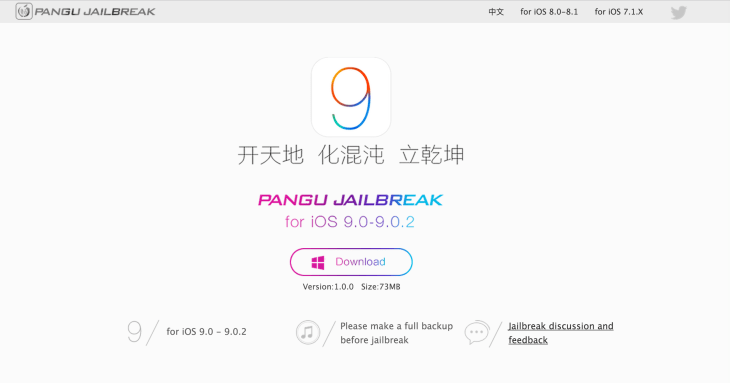
But a core community of iOS jailbreakers remains, and now they have a way to jailbreak their iOS 9 devices, thanks to a hack from a Chinese hacking team called Pangu released today.
The jailbreak consists of a Windows software package that allows for an “untethered” jailbreak – meaning, your device doesn’t have to be plugged into your computer to run. The jailbreak reportedly works on iPhones, iPads and iPod touch devices running iOS 9 through 9.0.2.
This is the first public jailbreak released for iOS 9, which supposedly runs a security system dubbed ‘rootless’ designed to prevent malware. The system was expected to be a big blow to the jailbreaking community. (An earlier jailbreak was not released to the public.)
Specifically, Pangu’s jailbreak covers the iPhone 4s, 5/5c/5s, 6/6 Plus, and 6s/6s Plus as well as the iPad 2, 3 and 4, iPad Air/Air 2, iPad mini, iPad mini 2/3/4, and the 5th and 6th generations of the iPod touch. In other words, an extensive list of both current and older devices.

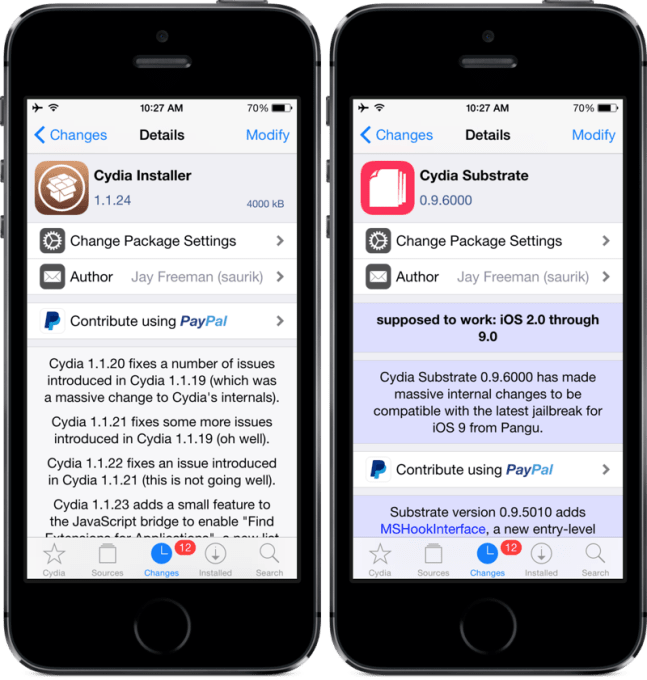
After jailbreaking, users are able to install Cydia, a framework that lets you download and install unofficial packages onto your device that allow you to run apps or make changes the iOS operating system would otherwise prevent.
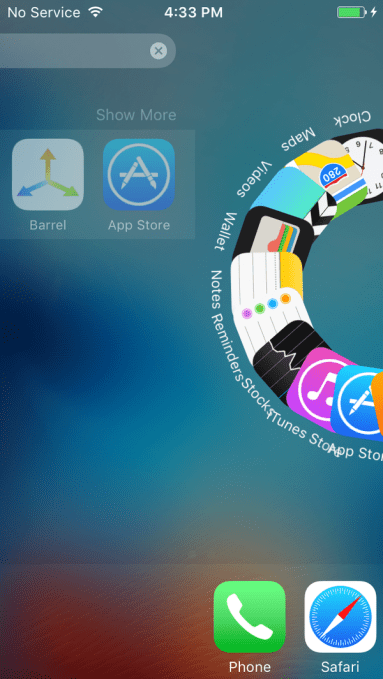
However, though devices can be jailbroken and Cydia can be installed, many of the apps and tweaks are not yet ready, notes modder enthusiast site ModMyi.com, which also says that some developers, like the makers of the interface tweak Barrel, have begun looking for testers.
Caution Advised
So should you run the jailbreak? Well, probably not. Unless you really know what you’re doing and are willing to put your device and your data at risk.
But if you’re determined and you need tips, Reddit users are offering a how-to guide and help.
 Jailbreaking not only violates your End User License Agreement (which voids your warranty and means you won’t be able to get help from Apple when things go wrong), it also exposes your phone to security vulnerabilities and puts your personal data at risk.
Jailbreaking not only violates your End User License Agreement (which voids your warranty and means you won’t be able to get help from Apple when things go wrong), it also exposes your phone to security vulnerabilities and puts your personal data at risk.
In fact, some of the recent attacks involving iOS malware -yes, it does exist! – have specifically targeted users with jailbroken devices.
For example, the KeyRaider malware, which accounted for what was possibly the largest known Apple account theft to date at the time – affecting 225,000 users – targeted customers who had jailbroken their phones. The malware attempted to steal account names, passwords, device IDs and more.
The more recent YiSpector malware targeted both jailbroken and non-jailbroken iOS devices. However, Apple confirmed that only those who had downloaded applications from outside the App Store, as jailbreakers tend to do, were affected.
In addition, many of the malware variants are focused on targeting iOS users in China, where it’s more common for iOS device owners to find workarounds to buying software directly from the App Store. The tendency to utilize unofficial resources – in part, due to the Great Firewall and the way it slows or blocks downloads from legitimate sites – also aids in the spread of malware in that region.
Even a number of top-tier app developers in the region recently released official versions of their apps onto the App Store, which contained malware after downloading a compromised version of Xcode. The XcodeGhost malware, as it was called, infected apps like DiDi Taxi, Baidu Music, WeChat, and several others.
In other words, with a slew of newly-jailbroken iOS devices coming online, you can be sure that the malware authors will step up their attempts at finding ways into these devices.
The Pangu hacking team, it should be noted, released their jailbreak into the wild instead of submitting their discovery to an exploit acquisition platform maker Zerodium, which was earlier promising a $1 million payday for iOS 9 jailbreaks. Zerodium founder Chaouki Bekrar said on Twitter today that’s likely because the Pangu jailbreak wouldn’t have qualified for the reward as it’s not remote and is publicly available.
The jailbreak is available here, if you dare. There’s no word yet on OS X support.