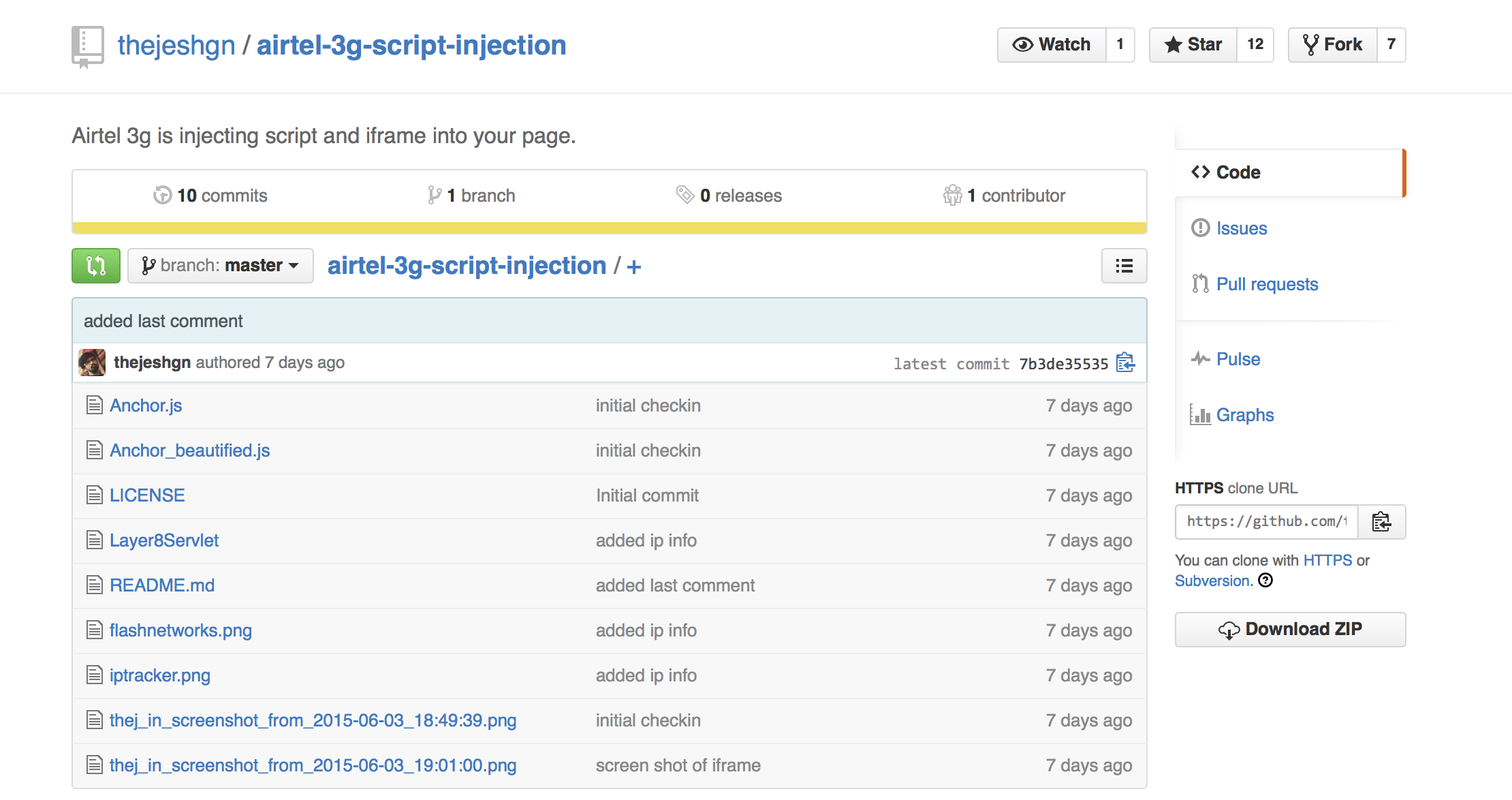
In an exciting example of the Streisand Effect, an Indian Airtel customer, Thejesh GN, discovered that the carrier had begun using Flash Networks Layer8 “monetization” (read “ad injection”) solutions. The code, which appeared on most mobile webpages downloaded via Airtel’s network, consists of a pair of basic JavaScript injectors. Thejesh published the code, which used to be freely downloadable via any browser, and was served a cease and desist letter.
The crime, it seems, was the uploading of public code to a public repository, Github. The code, which was publicly available here but now seems to be locked, is considered Flash Network’s proprietary property. However, like most code on the Internet, it is amazingly difficult to protect this claim barring proof of actual theft. However, like so many ridiculous cease and desist letters, that hasn’t stopped Flash Networks lawyer Ameet Metha at Solicis Lex from trying to scare Thejesh and Github, for their part, cravenly pulled the code as part of DMCA request.
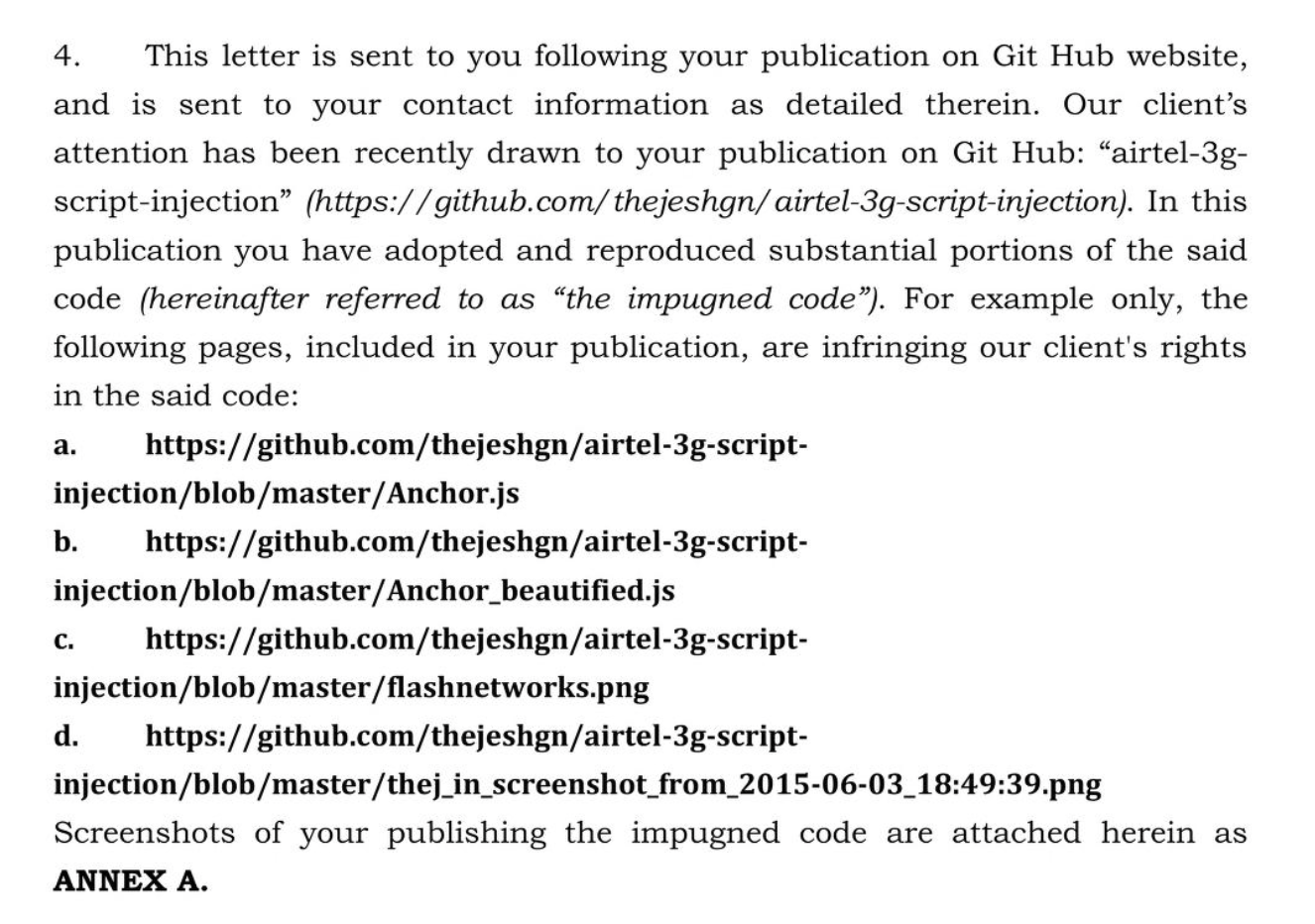
The problem with this sort of back-and-forth between spammers and the spammed is that the spammer never comes out ahead. Almost every example of code injection of this sort, from Superfish to AT&T’s attack on Weev make the corporations out to be the bad guys. While the Internet nerd in my says that isn’t a bad thing, the realist in me says that’s just silly. Presumably some short-sighted monetization person at Airtel talked to some short-sighted monetization person at Flash Networks and struck a deal which, because of the code injection, is unsafe and unwanted. Exposing that isn’t a crime and it is a crime for Flash Networks to make it one.
Airtel, for their part, told Storypick that they have nothing to do with the C&D:
I’ve contacted Flash Networks as well to see what they can make of this whole exciting ordeal. They write:
Relative to the legal notice sent by Flash to Thejesh GN – Thejesh GN published Flash Networks’ proprietary source code, without Flash Networks consent. This was done to protect and ensure Flash Network’s intellectual property. We are grateful that Github found our request reasonable and automatically removed the code. To clarify, no claims were made as to the discovery of the javascript injection as this is not confidential but rather to the disclosure of intellectual property source code.
We appreciate concerns about user privacy so we follow the most stringent ethical, regulatory and legal practices to ensure data confidentiality.