Once upon a time, when you wanted to secure something of value, you put it in a vault and distributed the keys. Today, when you want to secure software credentials especially as you move across services, you can use a digital secrets manager and distribute the virtual keys.
HashiCorp announced an early release of an open source secrets manager today appropriately called Vault. The tool provides a range of services including secure key and secret management with in-transit encryption, automated key creation, key revocation and detailed audit logs.
“The problem that it’s solving is at its core storing secrets, which could be passwords, credentials, certificates [and so forth],” Mitchell Hashimoto, co-founder at HashiCorp explained.
That’s becoming increasingly important as the world moves to micro services and containerization — think Docker — which requires passing credentials through this myriad of services. Keeping those containers secure has been a challenge.
“The need for service-oriented identity, communication, container security and container identity is really higher than ever,” he said. “Every Software as a Service you talk to (or anything as a service), requires an API key or credentials to do so.”
Recognizing A Need
The problem is managing those multiple credentials as you communicate across different pieces of the infrastructure and it’s a real challenge. From that perspective, the timing of this product couldn’t be better, but Hashimoto says while that’s a nice benefit, it’s not really why the company developed it.
Like so many products, Vault emerged from an internal need driven by customers. HashiCorp is made up of five (now six) open source products and it sells a commercial front end to the open source tools called Atlas. It requires credentials to get to other services it connects to and IT pros were reluctant to simply enter the company credentials into a third-party tool like Atlas without some security.
Necessity proved the mother of invention once again.
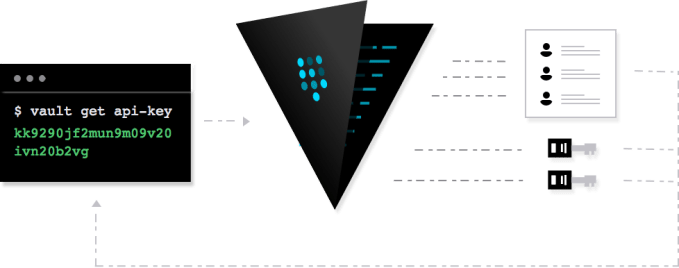
“It’s basically an encrypted source mechanism. You write stuff in securely [such as passwords] and you get stuff out securely.” What’s more, every action in the system is recorded in an audit trail, so all of the information related to the vault such as requests for credentials (or failed requests) gets recorded in a report and stored redundantly across multiple sources. That means if someone compromises your system, you can learn who they are quickly and revoke their credentials, all from the Vault administrative interface.
Hashimoto admits that in itself is not terribly exciting, but it solves a problem and it provides an open source mechanism for dealing with it. Where it gets more interesting is that the system can create new credentials automatically every time you need them. These credentials can have a limited shelf life, making it harder to steal. If a hacker somehow obtained these credentials, he or she might find they no longer work or they might only work for a limited time.
“That means you don’t have to even put secrets on disk anymore,” Hashimoto said. “They never have to be persistent anywhere. The application can request the new credentials, store them in memory and they never hit physical storage,” he explained.
And that solves a huge problem around hackers breaking into password databases. If there is no password database, there is no treasure to steal (at least no password cache).
Adding Additional Layers Of Protection
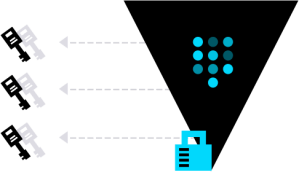 To further protect the system, it requires multiple keys to make changes. When you are first setting up, you decide how many keys you want and how many you need to perform an operation. Typically, customers generate five keys and it requires three to perform an operation. This is akin to a vault that required three keys to be turned within a certain amount of time to open.
To further protect the system, it requires multiple keys to make changes. When you are first setting up, you decide how many keys you want and how many you need to perform an operation. Typically, customers generate five keys and it requires three to perform an operation. This is akin to a vault that required three keys to be turned within a certain amount of time to open.
While he says he knows this isn’t completely fool-proof, the ability to audit and revoke does deal administrators a much stronger security hand — and the chances of three rogue administrators operating in tandem is pretty remote.
HashiCorp is not the first to come up with this idea. There are commercial offerings such as AmazonHSM. This offers a dedicated Hardware Security Module (HSM) appliance, which lets customers control the encryption keys and cryptographic operations in the cloud.
This is still a very early release, what Hashimoto calls version 0.1. The company is working with financial services clients to put the product through its paces. He believes if it can pass muster with banks and other financial services, securing other environments should prove much easier.
HashiCorp was founded in 2010. It received $10M in Series A funding last December. The company’s commercial product, Atlas provides a single place for developing, building, deploying and monitoring distributed applications.
Graphics courtesy of HashiCorp.
