New information in the Silk Road case is sending ripples of schadenfreude through the cryptocurrency community as it reacts to a foiled effort by two US Federal Agents to skim thousands of Bitcoin out of Silk Road and Mt. Gox coffers.
According to a statement issued by the United States Department of Justice on Monday, two federal agents are charged with wire fraud, money laundering and falsifying government documents for stealing Bitcoin while working on the Silk Road investigation.
The agents were part of a Baltimore-based task force investigating the Silk Road marketplace. Their mission included the task of building a relationship with Ross Ulbricht (aka ‘Dread Pirate Roberts’ the accused owner of Silk Road who was found guilty last month). The two agents leveraged their status as federal agents to mislead, pressure, and personally profit from their activities during the investigation – all of it which went unreported or unnoticed to the departments that employed them.
Information in the criminal complaint revealed that the Baltimore task force gained administrator access to Silk Road after arresting one of its employees. Secret Service Agent Shaun Bridges then logged into the Silk Road admin account that afternoon to personally conduct sizeable thefts from Silk Road accounts.
This theft was the cornerstone of the alleged “kill for hire” requests that were part of the case against Ulbricht’s. After the BTC went missing, Ulbricht had offered money to kill an employee who he believed stole from the Silk Road. Little did he know that it was Bridges, acting as the employee, who did the siphoning.
What’s interesting is that these Bitcoins were moved from Silk Road to Mt. Gox by Shaun Bridges where he could exchange them from BTC to USD, giving him time to set up a LLC and open a bank account so he could send the funds back to the United States.
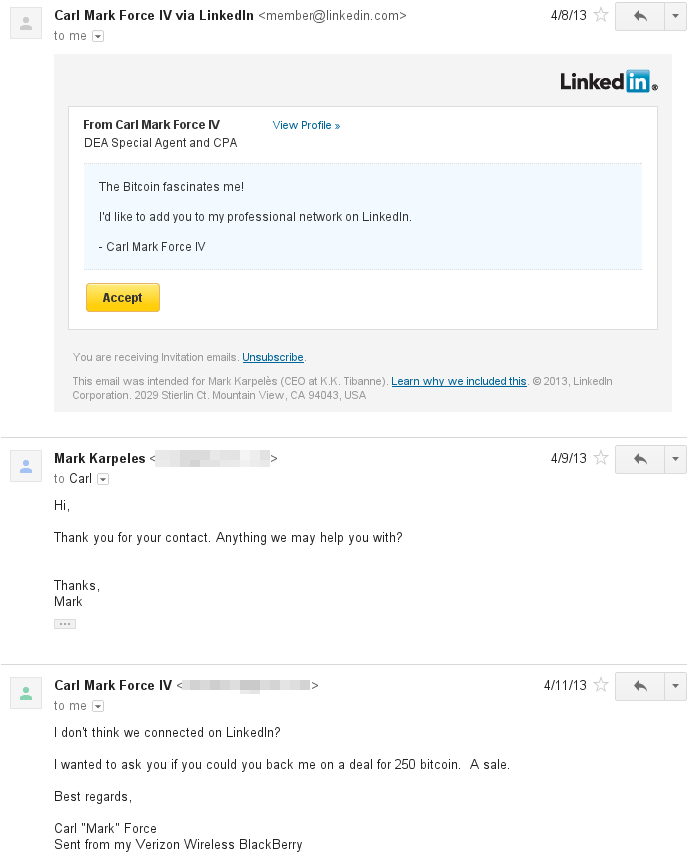
During that same time – the other federal agent charged, Carl Force, reached out to Mark Karpeles of Mt. Gox via Linkedin and asked if he would back Force on a sale of 250 bitcoins. Force said he was a federal agent but was looking for other employment.
During this time, Bridges’ funded his bank account with nine wires from Mt. Gox totaling $820,000 in a three month period. After completing these bank transfers, Bridges signed the seizure warrant against Mt. Gox, confiscating $5 million USD shutting down the Bitcoin exchange in the process. The affadavit charged that Mt. Gox was acting as a money services business without a license, unlawfully allowing people to exchange bitcoins to fiat currency – an activity which Shaun Bridges had conducted just days before.
A lovely email from Carl Force after the Mt. Gox seizure mockingly told Karpeles that he should have partnered with him – an offer which was declined by Karpeles a couple days before the shutdown. It’s important to note that Carl Force, a DEA Special Agent for 15 years – was doubly employed during this time as a ‘Compliance Officer’ for a Bitcoin exchange called coinMKT where he personally invested $110,000 USD worth of bitcoin.
In fact Carl Force used his DEA access to illegally run criminal history checks against users of the exchange and illegally froze one of its individual customer’s accounts containing $297,000 USD worth of digital currency and $37,000 USD in cash. The account in question belonged to a California resident who worked as a self-employed actor – unfortunately, due to a glitch in CoinMKT’s system preventing withdrawals over $10,000 – this account was flagged gaining the attention of Carl Force to take control of the funds even though he lacked a sufficient legal basis on which to do so.
Claiming that the seizure was part of a federal investigation (which was faked), Carl Force then had coinMKT move the bitcoins to his personal account at Bitstamp. Thankfully, Bitstamp became suspicious and froze the account after they noticed Carl Force trying to withdraw $80,000 USD into a personal bank account – while using the TOR (private) browser because he didnt wan’t the “NSA looking over [his] shoulder.”
It was only after Bitstamp talked to Bridges that Carl Force’s accounts were unfrozen and he was able to move the stolen Bitcoins which were exchanged to USD and transferred to his personal bank account. Carl Force’s made several real estate purchases, transferred some cash to off-shore banking accounts, and paid off his mortgage.
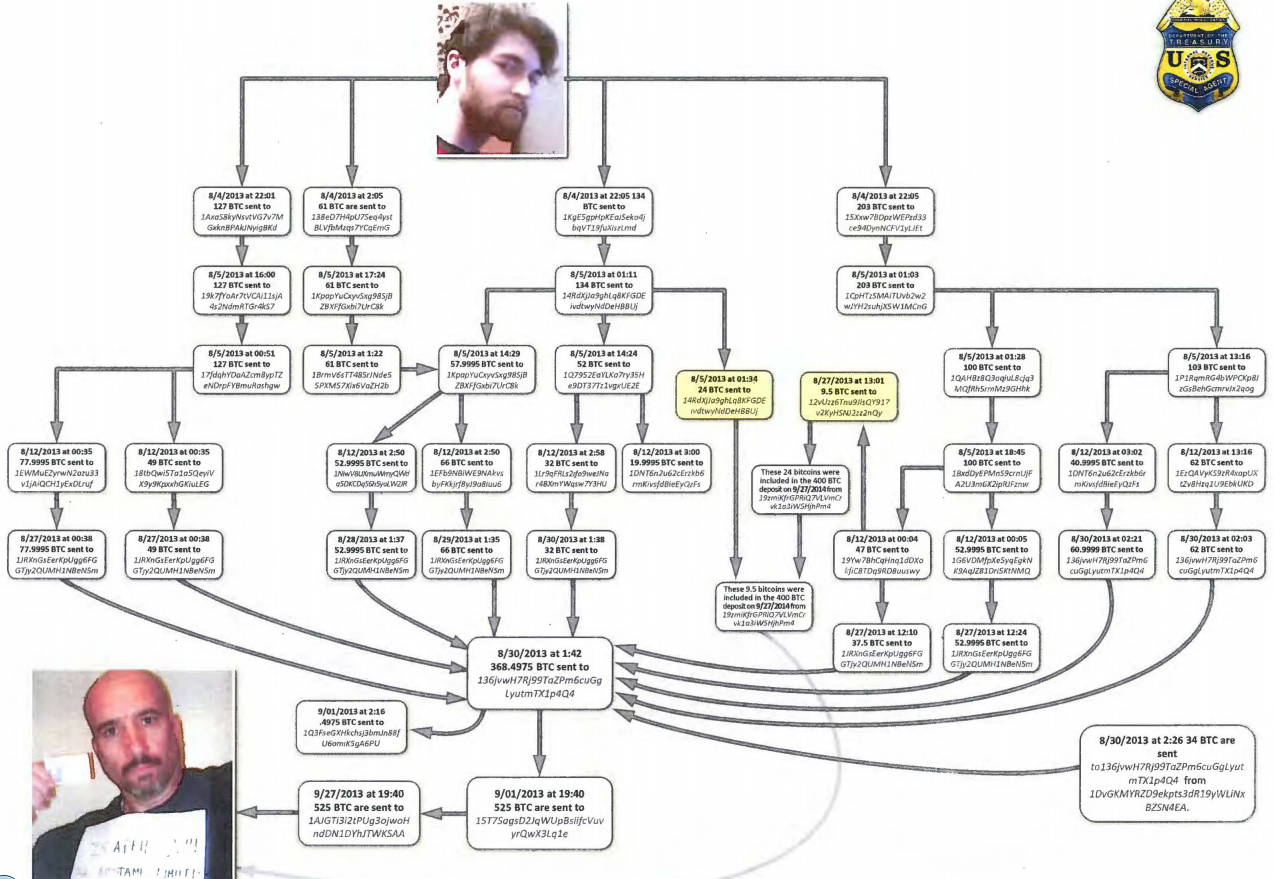
Shaun Bridges and Carl Force stole millions of dollars worth of bitcoin and digital currency. The federal agents used a number of bitcoin exchanges, payment processors, and bank accounts in an attempt to move their funds between accounts and identities. Unfortunately for them, they were unfamiliar with how Bitcoin is inherently traceable and transparent with transaction flows. Thankfully, we can thank IRS Special Agent Gambaryan Tigran for piecing this together. In the end, this strange sad saga is one more step on the road to cryptocurrency’s mass adoption and acts mostly as a cautionary tale for those who think they can fool the hackers at their own game.
Editor’s Note: Lisa Cheng is the chief executive of the Vanbex Group, a cryptocurrency consulting firm.
