The CIA has been involved in a “multi-year effort” to break through Apple’s security code, according to a new report from the Intercept.
Top secret documents provided by former NSA contractor Edward Snowden reveal a CIA-sponsored annual gathering called “Jamboree” where researchers presented the latest tactics at cracking the security code of Apple’s iPhones, iPads and proprietary developer tools.
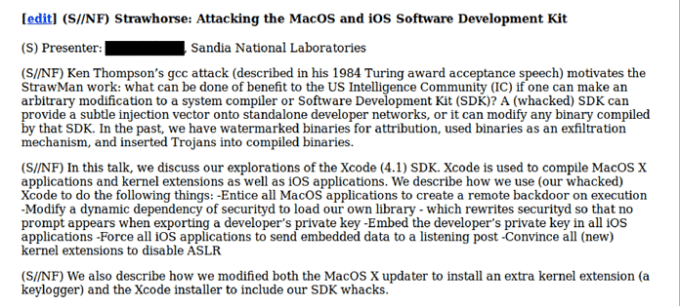
The report provides a total of 10 presentation slides detailing efforts to weaken the security of Apple’s products. One such slide describes the creation of a dummy version of Xcode that would be targeted at most likely innocent developers in order to “entice all MacOS applications to create a remote backdoor on execution.”
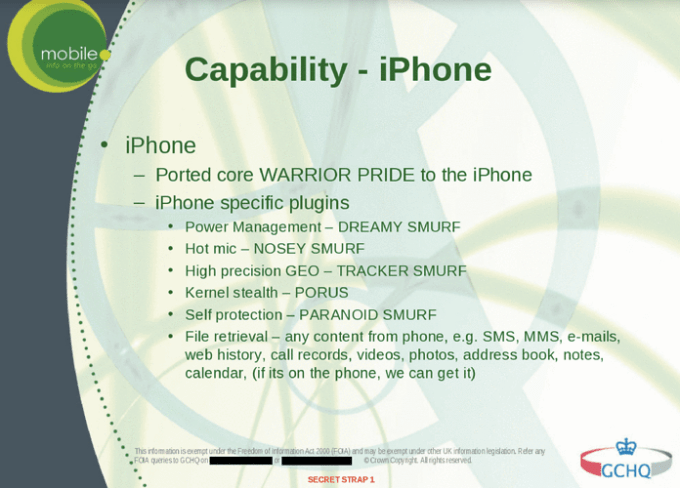
Another reveals efforts to embed surveillance and counter-surveillance for iOS devices (note the British Government Communications Headquarters logo and the reference to the WARRIOR PRIDE program that was revealed by Snowden last year on this slide):
“The most troubling part is the revelation that the CIA has targeted App Store developers – a vast majority of whom were US citizens in 2010 – to compromise their computers and install software that would then install back doors in all of those developers’ products,” security researcher Jonathan Zdziarski told TechCrunch. “This is very direct evidence of the government weakening commercial technologies and likely violating a number of laws by attacking innocent software developers,” he said.
The slides don’t reveal any successful operations, but the practice could potentially create security weaknesses within everyday apps used by millions of iPhone and iPad users, as well as compromise the security of every app made by targeted developers.
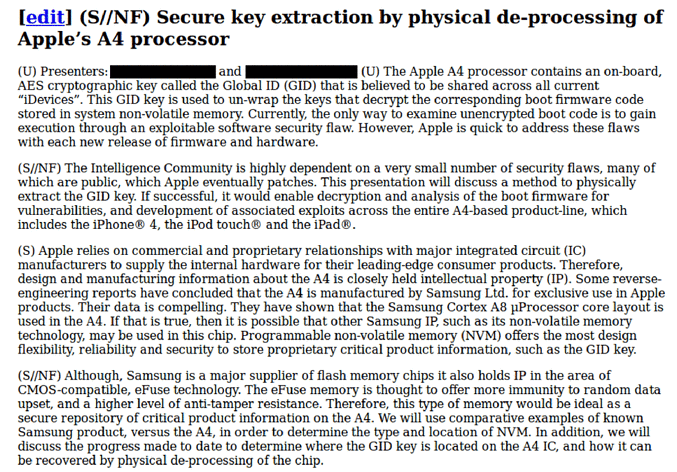
Even more troublesome is the kind of data the CIA was supposedly extracting from these devices. According to one slide, it was attempting to extract GID keys, not UID keys. UID keys allow access to an individual’s data on one phone. It’s something you’d want access to if you were trying to track a terrorist, according to Zdziarski. However, the GID 256-bit key is shared by all devices with the same application processor.
“So what that tells me is that the CIA was NOT interested in getting to encrypted personal data on individual devices, but was instead interested in cooking their own low-level boot firmware to install across an entire product line of devices,” Zdziarski said.
This sort of technique could be used for widespread mass surveillance, not targeted surveillance against one group of individuals, according to Zdziarski.
This is just one accusation in a series of damning allegations against the NSA and cooperating security agencies. The NSA worked in conjunction with the British equivalent organization Government Communications Headquarters (GCHQ) to steal SIM encryption keys, according to an earlier report from the Intercept.
This latest accusation also comes on the heels of other news that Wikimedia is suing the NSA over mass surveillance.
The CIA did not respond to a request for comment about this story.