Business services and retail operations saw the most online intrusions from malicious hackers in 2014, and one business was infiltrated and tapped for a full eight years before it figured out it was being targeted, according to Mandiant, a division of computer security firm FireEye. In the news recently for tracking how supporters of the pro-Assad Syrian government have been spreading malware through innocuous-looking chats, today the company is publishing its annual survey on threats and hacks that have breached security online.
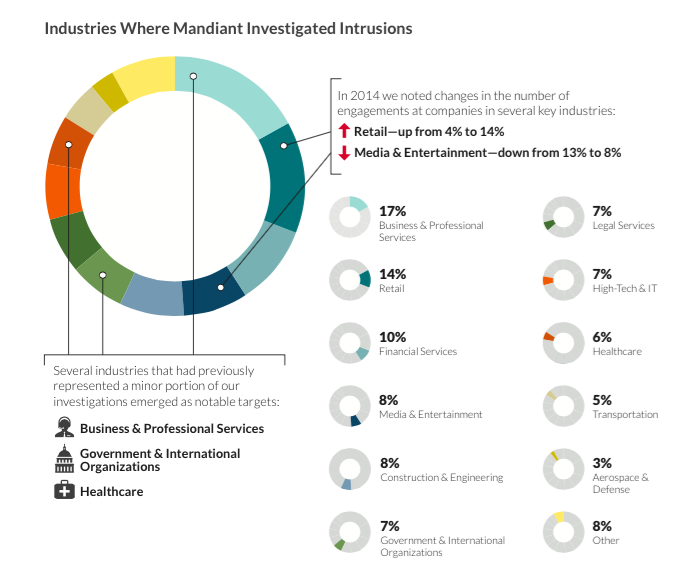
The report notes that malicious “engagements” at retail sites have gone up 10 percentage points in the last year, to 14% from 4%, while media and entertainment services — despite notable breaches like the Sony hack — have dropped to 8% from 13%. Similarly, business and professional services, along with government and healthcare organizations, all saw a rise in security intrusions.
One of the key issues with retail, Mandiant notes, is one of the most elementary. While retailers, in the wake of security scandals for companies like Target, had managed to segment their machines from each other, they still had not moved to two-factor authentication, “allowing for a single user credential to open up their entire networks to attackers.”
But while the targets may be evolving, some of the logic and methods are not: “Where money goes, criminals will follow,” Mandiant writes. “Retailers have always been in the crosshairs of financially motivated cyber criminals. We saw no change to this in 2014. While attackers used some new techniques and grabbed more headlines, their playbook remained largely consistent with what we have observed over the last few years.”
It also notes that in general attackers are becoming far more sophisticated to keep up with advances in security, with software being only part of the issue: hardware-based attacks remain a target, the firm says.
The report — embedded in full below — gives an overview of some of the more common routes that hackers are using to breach systems. Here are some other notable data points:
Detection time is dropping, but there are still some huge lags. One organization, it noted, was breached for over eight years before identifying the problem. (I would like to know who that is. Wouldn’t you?) On average the time it took to detect a breach in 2014 was alarmingly high — 205 days — although that is at least down from 229 days in 2013 and 243 days in 2012.
It’s still largely up to outsiders to raise alarm bells. Yes, companies are beefing up security, but apparently still not enough. Mandiant notes that 31% of organizations discovered their own breaches, using their own resources, only slightly down from 33% the year before. In other words, 69% of breaches were identified by external people, who then alerted the targeted companies.
“Threat actors” are posing as IT employees — and getting away with it. This is now the most popular route for phishing schemes, Mandiant says, with 78% of all phishing being malicious hackers impersonating nice guys from the IT department asking you to update your credentials, taking a page from the phishing book that has been used on consumers for years now.
Chip-and-pin is not as safe as you think. Although mag-stripe cards have often been seen as a far less secure alternative to chip-and-pin services, the latter is not 100% secure, either. Hackers are now coming up with ways of breaching EMV systems, too — just in time for U.S. adoption of the standard. This could end up being a boost to mobile payment and tokenization services. That is, until criminals turn their attention to cracking that code.
