Editor’s note: Steve Herrod is managing director at General Catalyst Partners and the former CTO and SVP of R&D of VMware.
As we bear witness to the aftermath of major attacks this year against the likes of Target, Home Depot, Neiman Marcus and most recently, Sony, it becomes clear that we are entering an entirely new “war” against cyber crime. Those who do not change their approach will lose.
The sophistication and proliferation of advanced malware is greater than it has ever been, and widespread awareness of this problem is being fueled by the near daily headlines touting the latest company to fall victim to a cyber attack. Large enterprises are investing more money into cybersecurity technologies than ever before, and the need for a stronger and more comprehensive security model has become a board-level discussion as the severity of these attacks hits home for businesses and consumers alike.
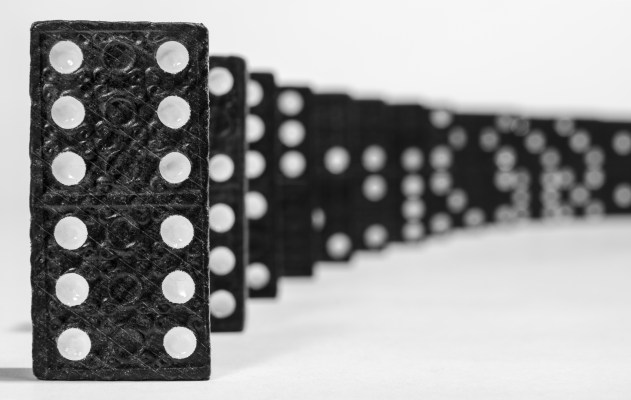
While the cybersecurity crisis has seemingly come to a head in 2014, the increased challenge with protection has been years in the making due to the proliferation of mobile, cloud and virtualization technologies. Perhaps ironically, it is these newer computing paradigms that also offer new avenues for addressing the problem. The convergence of these technical factors, coupled with increased human usage and awareness, is building up to what will be a tipping point for cybersecurity in 2015. A new approach to security is needed based on the following pillars.
Assume You’re Always Under Attack
All security technologies today, even the state-of-the-art virtual execution tools, rely on techniques and algorithms to identify “good” from “bad.” Sophisticated cyber criminals are selling malware that is guaranteed to get through these security solutions because they masquerade as “good” or use software vulnerabilities that have not yet been discovered.
Companies are undertaking enormous costs and administrative burdens playing catch-up with software patching and signatures, and/or deploying an army of analysts to deal with the barrage of false positives generated by traditional security solutions.
Next year, we’ll see the emergence of security tools that are based on the core assumption that it is impossible to tell good from bad. Security models will focus on eliminating attack vectors or isolating their outcomes, and move away from the never-ending battle of separating “good” from “bad.” The cloud offers near boundless resources for these new approaches.
Security Must Be Dynamic and Software-Defined
Cloud computing and virtualization are allowing businesses to do more and work faster than ever before. Data centers are now incredibly dynamic and widely distributed, requiring a much more flexible and adaptive security model. Traditional infrastructure security technologies that are based on the idea of a perimeter have become obsolete. The perimeter is dead; mobile devices wounded it and the cloud finished it off.
Applications today are mobile, and security must be built to move with them. In 2015, we’ll see more solutions focused on securing the perimeter-less enterprise, and protecting these cloud and virtual servers that make up the modern data center. In most cases, the solutions themselves will leverage the power and flexibility that comes from virtualization and the cloud.
Information Sharing Is Critical to Security
Many organizations, from the enterprise to public sector, have a wealth of security data that can be applied to their defenses, but this information is often siloed within their own organization, making it difficult to leverage it in tracking broader patterns and getting ahead of attack cycles. Historically, businesses have been reluctant to share security data for fear of exposing weaknesses in their architecture or disclosing proprietary information.
However, by sharing data and applying the latest in big data analysis — which has a very real application in the security industry — companies are realizing the power in numbers. Holding off organized crime and malicious nation-states is a daunting task for any individual company, but the odds look much better as like-minded companies band together for their collective defense. In 2015, we will see more organizations proactively sharing and comparing threat, attack and vulnerability data among cohorts and across industries, enabling themselves to better predict, prepare for and defend themselves against attacks.
This year will likely go down in history books as the watershed year for cybersecurity. As realization spreads that existing security technologies are no longer capable of addressing today’s threats, we will see more vendors leverage virtualization and the cloud to catalyze a fundamentally different security model in 2015.