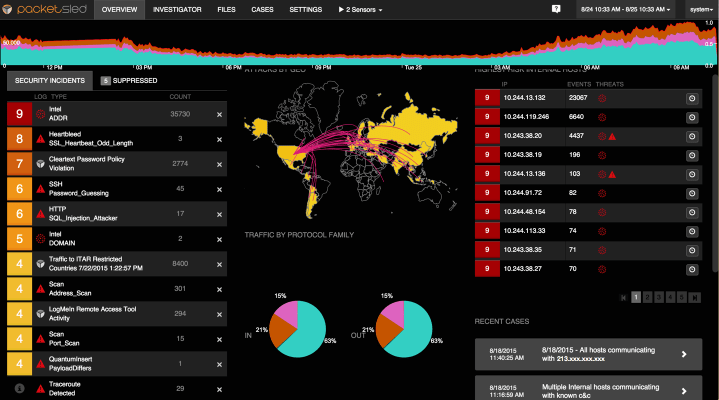
In my years as a programmer and network manager (I still kind of do that stuff when I handle my own servers) I’ve discovered that the tools used have been far from intuitive. While powerful, command-line and web-based systems tend to be confusing, apocryphal, or messy. That’s why Packetsled piqued my interest. This startup has produced a network monitoring tool that uses an interface familiar with anyone who has watched War Games or Jurassic Park and, thankfully, their complex platform is also very powerful and offers a number interesting tools for searching traffic and seeing alerts.
First, as a relative novice, I was intrigued by the setup. The platform runs on a virtual server or on its own hardware and is essentially a powerful web app. You point it at your point of ingress and the machine does the rest, parsing data that flows in and out and looking for suspicious traffic. You can also perform natural language searches on traffic like asking for the last five minutes of web traffic or specific IP address information. It also stores everything – and I mean everything – that happens on your network.
Created my Matt Harrigan and Rick Moy, the platform is not for the faint of heart. Because it manages all traffic on your network it is essentially a very promiscuous appliance and allows you to see everything that’s happening on your network – and I mean everything. In the demo system I used I was able to see notifications that I had sent a plaintext password to an FTP site (acceptable but bad) and I could also see porn visits (which were for testing purposes only). The team also showed me the methodology for tracking virus infestations: a user’s computer is singled out as a virus carrier and the system can track exactly where and when the virus was downloaded and what it is doing to your network. Thankfully all of this appears on a screen that’s easy to read and understand.
As the creator of the first commercial pentest, and someone who has evaluated some of the world’s largest enterprise networks, it became apparent to me that attackers have the advantage. While an attacker only has to find one way in, the defenders have the burden of protecting against an almost infinite set of possibilities,” said Harrigan. “Today’s organizations are trying to process a flood of alert data and they’re drowning, often leaving dozens or hundreds of alerts per day unevaluated. These alerts represent unprocessed business risk to the organization. By providing analysts with visibility and context into potential events, we can dramatically reduce the dwell time, the time between the event and identification, and thus reduce the risk.”
All that is security nerd speak for “This product actually gives you alerts in real time.” While it’s hard for me to comment on how this would work in a larger organization, the services and methodology is sound and could easily integrate into your everyday IT setup. Because it runs on a separate server you won’t bog down your internal servers with forensic tools and, thanks to the search features, you can easy set up forensic tests for you and your workstations in order to ensure nothing slips past you. It’s a fascinating piece of software that, in the end, improves upon the traditional tools by making them nearly invisible.
Pricing depends on your processing needs but you can try the beta for free now.
[gallery ids="1085476,1085475,1085474,1085473,1085472,1085471,1085470,1085468"]