Can your computer be hacked? Yep. Can your phone be hacked? Yep. Have your passwords been harvested? Very possibly. (The NYT just reported that one Russian group has more than a billion, though it’s unclear how many are salted and hashed.) So how worried should you be, exactly?
…Good luck getting a real answer to that. Almost nobody has a strong incentive to give you one. You probably want a thoughtful, rational, dispassionate analysis of the security threats that you–or anybody–may face; but a fundamental problem with the security industry is that hardly anybody has any reason to provide that.
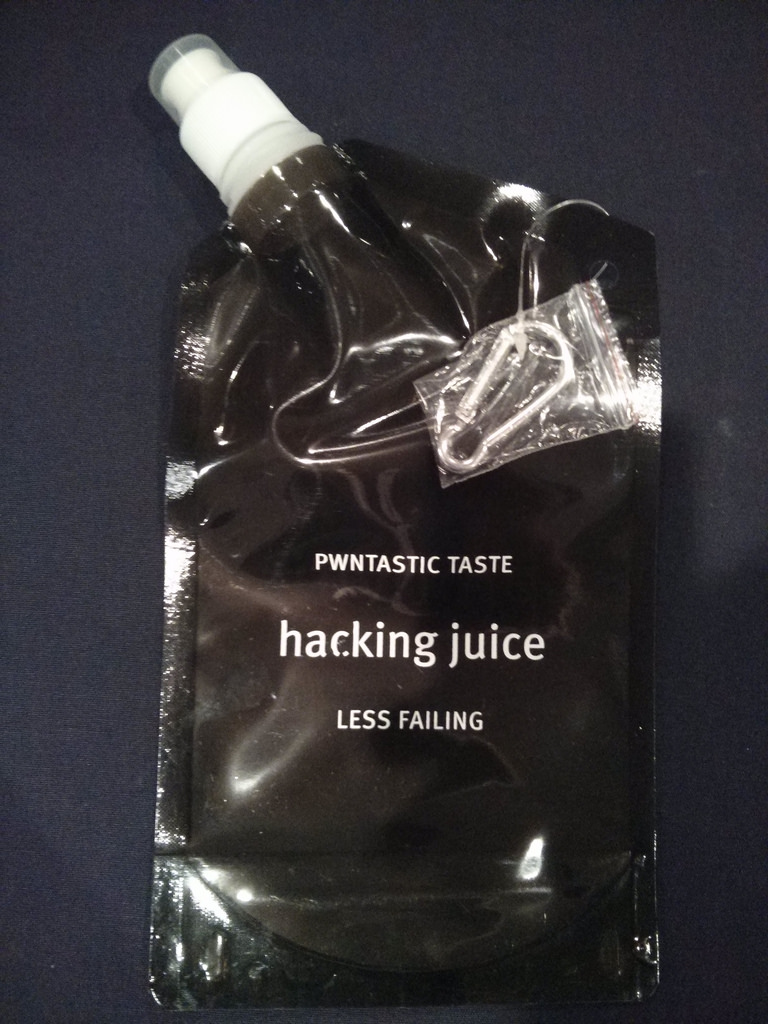
It’s Hacker Week here in Sin City, and your humble correspondent is here to report on it. Over in the colossal deluxe Mandalay Bay, Black Hat hosts thousands of infosecurity professionals paying thousands of dollars apiece, many of whom will change from business-casual to hacker-black for this weekend’s cheaper and less corporate Def Con. Meanwhile, over in the much-more-modest Tuscany Suites, the B-Sides security “unconference” is underway, irreverent and idealistic; here the lanyards are laced with blinkies, an attendee who looks like Gandalf in a top hat and Utilikilt does not seem out of place, and the available swag includes:
The B-Sides keynote speaker was Microsoft’s Adam Shostack, who called on security professionals everywhere to openly disclose and report in full on every successful hack and compromise of their systems, so that the industry can begin to analyze attacks in a fully informed, data-driven, scientific way. He argued that the fears which drive the usual corporate instincts for maximal secrecy after their systems or data are compromised — fear of customer loss, fear of legal repercussions — are greatly overblown, and that people often trust transparent organizations far more than opaque cover ups. In a melodramatic moment at the end he asked security professionals in the audience to stand up to signify a commitment that they would push for this kind of openness when they could. Dozens did.
But there’s at least one massive roadblock between reality and Shostack’s desired future: the computer security industry is not in the business of openness, it is in the business of fear.
When your funding depends on the level of terror among those who hold the corporate purse strings, you have every incentive to maximize that fear — and irrational fear of the unknown, of shadowy ill-defined doombringers, is always more powerful, and hence more lucrative, than well-considered concerns about rationally analyzed and carefully modeled threats. Shostack is right that an open, scientific, collective response to Evil Hackers™ and other security threats would be enormously more effective than the silent, siloed, semi-secret status quo; but there’s inevitably less money in that.
Does this all remind you of, say, the security-industrial complex and the NSA’s business of fear, along with ongoing expansion of its funding and its powers, at least until Edward Snowden blew the whistle? Yeah, it’s not a coincidence that Keith Alexander, then head of the NSA, keynoted last year’s Black Hat, and today’s keynote speaker is the CISO of In-Q-Tel, the CIA’s venture fund.
Don’t get me wrong. There are all kinds of serious infosecurity threats that we most definitely should be rationally afraid of: threats to our computers, our phones, our data, our infrastructure, etc etc. More on those as this week progresses. But as you do, bear in mind that almost nobody in the security industry, private or public, has a financial incentive to provide open, transparent analysis and measurement of the threats we face … which, as Shostack points out, is exactly the best way to fight them.
(While I’m casting aspersions, let me also admit; the media is also incentivized to maximize fears, threats, and anxiety. “If it bleeds, it leads” and all that. This is probably almost as big a problem.)
Even good people can’t help but be affected, consciously or sub-, by this kind of incentivization. Bear that in mind every time we hear about a new, scary, shadowy security threat; and let’s all hope somebody figures out a better way to incentivize security transparency.
