You’re sitting in your living room. All you want to do is watch some Game Of Thrones on your day off… but your Chromecast refuses to respond. All it will do is play Rick Astley’s Never Gonna Give You Up… over… and over again.
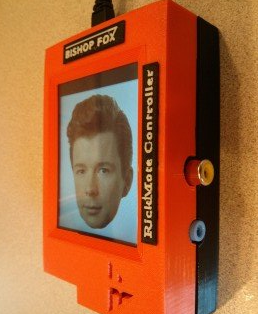
It might be this little box’s fault.
Built by security analyst Dan Petro as a proof of concept, his so-called “Rickmote” is able to discover any Chromecasts nearby, boot it off whatever network it’s on, and send any video the prankster desires straight to your screen.
So how does it work? Petro has a 20-minute breakdown video here, but here’s the gist of it:
- The WiFi standard has something called a “deauth” command built-in, which tells a device that it needs to leave the network and try to reconnect
- For one reason or another, this command is sent to a device without encryption… which means it can also be sent from devices that aren’t actually allowed on the network. That’s not a Chromecast bug; it’s a fairly universal quirk of WiFi devices. Most devices just go “Okay, whatever” and instantly reconnect.
- The Chromecast, however, responds to the deauth command by going back into configuration mode. It starts broadcasting its own WiFi, which you — or a prankster — can connect to to configure the device.
- The Rickmote, built on top of a Raspberry Pi, finds a Chromecast, floods it with deauth commands, then tells it to connect to its WiFi network, instead. Tada! Chromecast hijacked
Once a prankster has hijacked the host seat, they could send the Chromecast videos, or songs, or do whatever else you normally might as the legitimate operator. The nasty part: unless the prankster gets bored or goes out of range, there’s no easy way to get the Chromecast back under your control.
Alas, this isn’t an easy thing for Google to fix. The way the Chromecast responds to a disconnection is intentional; it’s part of the super simple configuration process, and that’s a good chunk of what makes the Chromecast a Chromecast.
Fortunately, the Rickmote is a one-off for now, so you probably won’t see this sorcery out in the wild any time soon — but the source code is out there for others to make boxes of their own.
[via RaspberryPi]