One of the more interesting devices here at Mobile World Congress is Blackphone: a pro-privacy handset being developed by Spanish startup Geeksphone, in partnership with U.S. security company Silent Circle using a “security-oriented” Android build called PrivatOS.
“We modified some default behaviours of Android and some security flaws that we found and we call that PrivatOS. It’s just small modifications of the Android core,” said Geeksphone founder and CEO Javier Agüera, demoing the device to TechCrunch.
“For example the default crypto engines — there’s a list of crypto engines that the system by default uses… and in the first version of Android the first option was good enough, then they changed it for something that is terrible. So we reverted that to what it was before.”
“PrivatOS is 100% compatible. It doesn’t create any fragmentation at all,” he added. “Also we made performance improvements.”

The Blackphone will ship in June — with a price-tag of $629 — but the company has already started taking pre-orders via its website, and snagged its first carrier partnership with Dutch mobile operator KPN.
PrivatOS will get direct — and frequent — over-the-top updates from Blackphone, with no carrier bottleneck to negotiate. Which is as it should be; a security-centric phone can’t have users waiting around for a fix to a new software vulnerability.
“This is one of the most important features because if we discover something we will fix it right away,” said Agüera. He added that new PrivatOS features that get developed in future will also be made available to all existing Blackphone users.
The version of the handset on show here in Barcelona is a demo version, with both the handset design and its software set to change before the product ships.
“It’s going to be completely different,” Agüera said, adding that the phone may also get some additional features than those already announced, come launch.
The pro-privacy feature-set that has been detailed so far includes Silent Phone and Silent Text for secure, encrypted telephony and messaging — using Silent Circle’s secure network — so that only you and someone also using a Blackphone or using Silent Circle’s service on another device are privy to the contents of the messages.
Contact data is also protected on Blackphone in the event of the device being lost via a remote wipe feature that does not require a third party cloud service to be involved in the chain. “You have [remote wipe] on other devices but you rely on a third party company with a cloud,” said Agüera. “This company knows where your phone is. We don’t know where your phone is.”
Blackphone does not hold any encryption keys for the secure messaging itself — ergo, it can’t be strong-armed into giving up your secrets by overreaching government agencies since it can’t unencrypt your data. Silent Circle of course shuttered its own email service last August in the wake of the Edward Snowden NSA revelations — saying it was doing so to pre-emptively avoid having to be complicit with NSA spying.
As for local data stored on the phone, the Blackphone user is given the option to encrypt this — an option that is suggested to them right at the start of the device set-up process, underlining the “optimized for privacy” ethos of the whole project.

Secure cloud storage is included in the cost of Blackphone via SpiderOak, one of the partner services bundled with the device. Blackphone buyers get two years free SpiderOak service included.
They also get two years’ of Disconnect (capped at 1GB/month), a secure/non-trackable search product that deploys a VPN to anonymise Internet browsing on Blackphone. Unlimited use of Kismet’s Wi-Fi analyzer product is also bundled into the package. Plus there’s one year of Silent Circle usage to gift to friends/family so you have some people to talk securely with, even if they don’t own a Blackphone.
“Disconnect is a very interesting because, as it’s integrated deep inside you device, it can anonymize all your Wi-Fi browsing and it actually secures the Wi-Fi connection,” noted Agüera, demoing the app running on Blackphone.
“When you click here [to activate Disconnect] everything you do on the Internet goes through a VPN and that affects all the applications on your phone. And we don’t have to root your device or anything, it’s already there. And it’s already enabled for all the applications you will install.”

While normal VPN use slows down a connection, Agüera said the opposite is true when browsing on Blackphone through Disconnect. “What this VPN does is it removes all the crap that the websites put — all the advertising, all the tracking cookies, and it’s faster than a normal connection,” he said.
Notably there’s no ‘Silent Email’ product on the phone. The security of email is clearly problematic at this point. But Agüera told TechCrunch the future intention is for Blackphone to incorporate the open source encrypted messaging protocol currently being developed by Lavabit — under the Dark Mail banner (Silent Circle is a founder member of the Dark Mail alliance).
For now, the focus for Blackphone is clearly on raising the level of privacy the average user experiences by making a suite of security features more accessible and visible to the user. By, for instance, foregrounding switching on local storage encryption by making it part of the set-up mix.
“Blackphone is meant for people from all walks of life who are concerned with privacy,” said Agüera. “It can be very expert people but it can be not so expert people. It can be normal users from the street, or politicians or whatever.
“There’s an activation wizard so that when you take your device out of the box you’ll configure the device as a security expert will do but in a very easy, simple way.”
The activation wizard gives the user a short intro on Blackphone’s pro-privacy ethos, before diving into the set-up process proper — kicking off by requiring them to use at least a PIN or a password to secure their device. Users will also be told how secure their password choice is.
After this, the encryption option is offered which, if selected, secures data stored locally on the device — with the key being the PIN/password the user previously selected.
Access to/activation of the Blackphone’s bundled third party security services is done by the user scanning a QR code to provision the licenses for those services. Blackphone users can also choose not to use these bundled services, if they prefer.
Blackphone owners need to provide a username and email address during the set-up process, which Agüera said is “the only information we keep from you”.
“We keep your nickname [username], which is not your real name unless you want to, and that’s the only information we will ever have about you. If you ordered online or in a shop we will have your shipping details but once we give those to the shipping company we delete that data.”
Agüera argued that the set-up process, which takes less than five minutes, already puts the Blackphone user in a far more secure place than the average smartphone user. “You have taken some steps that 99% of users don’t make — like encrypting the whole file system,” he added.
PrivatOS continues works in the background to push its security-focused agenda, configuring the device with optimal security settings and flagging up app insecurities to the user.
“We’ll disable that you can install apps from non-trusted sources by default, we won’t let you connect to an open network when you’re configuring — we’ll remind you that you need to be using a secure connection. We’ll establish firewall policies,” noted Agüera.
Users are still free to do less-than-secure things on Blackphone, if they choose — such as download Google apps which are obviously going to try to harvest their data. But the phone will at least raise a flag about certain types of apps and services.
“The point of Blackphone is giving you information and choice,” said Agüera. “The point is making a phone that you can use. You can download Angry Birds and we’ll tell you what are the risk you’re taking, what does the Angry Birds application do and then you choose.”
More granular security information is pushed to Blackphone users via a Security Centre hub on the phone. This includes updated briefings on recommended best practices for privacy and security. But the main feature is analysing individual app behaviours to see what they’re accessing, and to give users the ability to block certain actions for individual apps.
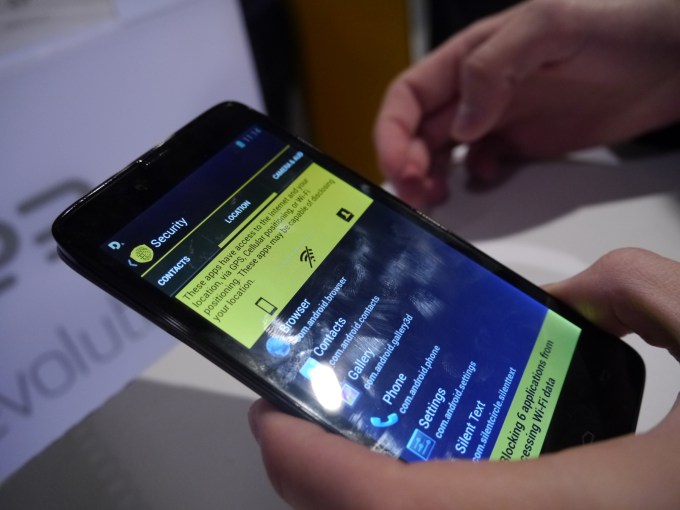
“It’s not the permissions that the application says it will do… we actually analyse the application,” said Agüera. “So when you configure your device for the first time we analyse all the default apps so it’s ready to use when you turn it on.”
For example, via the Security Centre, a user can go to a location tab and see all of the apps that use location and then turn off their ability to use personal data, or to harvest your Wi-Fi information.
“As an example, if you go to a sound recorder app you’ll see it records audio. That makes sense. But it also accesses the Internet. ‘Why should a sound recorder access the Internet? I don’t want that. Switch it off’,” explained Agüera. “Some apps may not work after you do this. We’ll tell you — we’ll say ‘ok, this game that you downloaded, it accesses your contacts list — if you turn it off, it’s not going to work. What do you want to do? Uninstall it or not — it’s up to you.”
He also pointed out that some companies are doing Wi-Fi tracking of mobile devices to identify repeat visitors to a particular location, for instance. This can be used, in one example, by coffee shops and restaurants to track visitors and figure out what food/drinks to offer them, based on what they ordered elsewhere.
But it can also have less beneficial, more creepy uses to mobile owners — so Blackphone has incorporated a technology into its device that knows when to kill the Wi-Fi to protect the users’ privacy.
“Imagine you go to an investment bank for a job interview — what will you think if the person who’s interviewing you knows that you also make the same interview at a competitors’ bank a few streets away?” he said.
“That’s a bit creepy and with this technology… developed [by Kismet creator Mike Kershaw] specially for the Blackphone it takes control of the Wi-Fi chip, it learns where your safe locations are — home and work normally — and when you leave your home.. if you’re not in a safe environment it will switch the Wi-Fi off.”
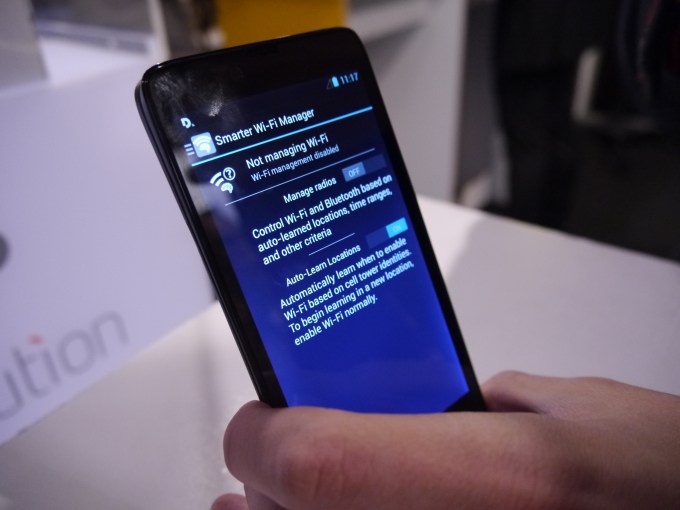
If you use an open Wi-Fi network somewhere — such as at a coffee shop — that location will still be able to gather data on you at this point, but Agüera said Blackphone is working on techniques that will effectively cloak your presence by randomizing the parameters that they use. “So even if they detect you, the next time they detect you, you’ll be a different person,” he added.
As for the security of the mobile chipset hardware inside the Blackphone itself, that layer is out of the company’s hands to a degree. However Blackphone general manager Toby Weir-Jones told TechCrunch that it doesn’t currently know of any backdoors in the chipsets it’s using, and if it finds any it will commit to telling Blackphone users.
Of course the Blackphone is not ‘NSA proof’, as Weir-Jones reiterated. “Bad guys wanting to talk to each other probably shouldn’t be using a phone at all,” he said.
But he described security as a spectrum — and said the level of privacy protection Blackphone affords its users is far greater than what the average smartphone user can expect.
