Buffer, the social media scheduling service, experienced a potentially brand-damaging security breach last month that saw a slew of weight-loss spam posted to Twitter and Facebook on behalf of its users. And although it turned out to be the company’s database provider, MongoHQ, that was the origin of the compromise, Buffer, by its own admission, was squarely to blame as it hadn’t encrypted access tokens for the social media services it supports. Today the startup is announcing a host of new security measures, including encrypting user email addresses and access tokens, and 2-step login, in a bid to restore confidence in its wares.
“With all that trust given to us, despite the big mess, we wanted to really step up our game in terms of safety and security,” writes the company on its blog. “For the past few weeks, we have been focusing on making Buffer the safest, most secure way for you to manage and publish to your social media accounts. We have a number of awesome things to show you. The most important step in this process is a feature we’re announcing today: 2-Step Login”.
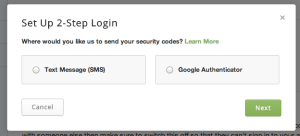 An optional setting for all Buffer users, 2-step login requires an additional security code to login to your Buffer account. It can be powered by SMS, requiring each user to register a mobile phone number with their account, or Google Authenticator, Google’s own 2-step authentication app for iOS and Android. Both single and team Buffer accounts are supported. It’s worth pointing out, however, that 2-step login, though a very sensible move, especially since a brand’s image is essentially in the hands of its employees and Buffer’s security, wouldn’t likely have prevented the recent breach. But it’s a good thing, nonetheless.
An optional setting for all Buffer users, 2-step login requires an additional security code to login to your Buffer account. It can be powered by SMS, requiring each user to register a mobile phone number with their account, or Google Authenticator, Google’s own 2-step authentication app for iOS and Android. Both single and team Buffer accounts are supported. It’s worth pointing out, however, that 2-step login, though a very sensible move, especially since a brand’s image is essentially in the hands of its employees and Buffer’s security, wouldn’t likely have prevented the recent breach. But it’s a good thing, nonetheless.
To that end, Buffer has also added encryption for user emails addresses and access tokens for social media services (Twitter, Facebook, Google+ etc.), preventing exactly the kind of hack that caused last month’s “big mess”, as well as having all of its own team members change their passwords and set up two-factor authentication (where possible) on accounts for Google, Github, Stripe, HipChat and Dropbox. The thing about security is it’s only as strong as the weakest point in the chain, and that is more often people.
