The Syrian Electronic Army has claimed responsibility for hacking the domain name servers of two of Twitter’s sites, and a third appears to have been redirected to servers hosted by the SEA. In addition, attacks have been made on The New York Times and Huffington Post UK name servers. [Updated with statement by Twitter and confirmation statement from Melbourne IT. Both are at the end of the article.]
The New York Times says it was attacked via its registrar, Melbourne IT. Once the Syrian Electronic Army had gained access to registry records, it was able to change both contact details and domain name servers.
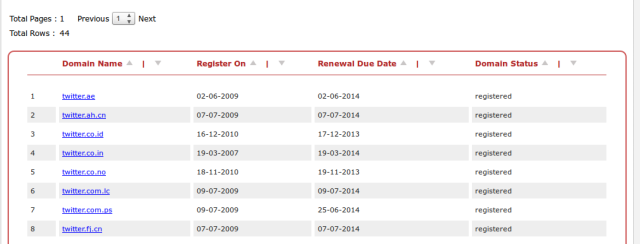
Now, the SEA is claiming access to a variety of international Twitter domains:
After the claimed responsibility for hacking the DNS records of the New York Times, additional issues began being popping up in relation to the hosting of Twitter images. Those issues were followed by a tweet from one of the Twitter accounts attributed to the hacking group, claiming that it had control over the Twitter.com domain. At this time, it appears that the name servers of Twitter have not been changed, only contact information.
The SEA then followed up by claiming responsibility for Huffington Post UK and New York Times domain name server changes.
Another tweet from the account points to an outage of Twitter.co.uk, whose DNS records have also apparently been altered to refer to the SEA’s servers. The Twimg,com domain, which serves up Twitter images and avatars, also shows changes that point to servers that are apparently SEA-owned.
A Twitter representative told TechCrunch that the company was ‘looking into’ the possibility that the SEA had changed DNS records.
“The site is down for some, not all and we are working to fix the problem,” said NYT spokesperson Eileen Murphy. “Our initial assessment is that this situation today is most likely the result of a malicious external attack.”
Interestingly, both The New York Times and Twitter name servers appear to have been registered through the registrar Melbourne IT. This led some to posit that a breach at the registrar allowed changes to be made, possibly with an administrative account. This would explain why the changes are being made across several companies. The New York Times has now confirmed that this is true.
According to a report from The Next Web, Melbourne IT began managing Twitter’s domains in 2009. The firm inherited VeriSign’s high-end DNS business when it acquired it in 2008 (thanks Doug). And Melbourne IT’s domain business itself was actually acquired by CSC earlier this year.
Chief Information Officer Marc Frons of The New York Times issued a statement to employees that attributed the attack to “the Syrian Electronic Army or someone trying very hard to be them.”
New York Times employees were then instructed to be careful when sending sensitive emails until the situation had been resolved.
This is the second time that the Times has been down in a month, with the previous outage coming on August 14th. The Times has been working hard to circumvent the loss of control of its DNS servers by tweeting links directly to its IP address and posting news at news.nytco.com.
The Wall Street Journal has taken advantage of the situation by temporarily removing its paywall and perhaps even advertising this fact against tweets about the New York Times hacking incident.
The SEA has made news over the past several months with high-profile media hacks including one of an AP Twitter account which caused a massive crash in stock market trading briefly in April. The SEA sent a tweet out about a fake attack at the White House.
Update: Twitter has issued the following statement on the DNS record issues with Twimg.com.:
At 20:49 UTC, our DNS registrar experienced an issue in which it appears DNS records for various organizations were modified, including one of Twitter’s domains used for image serving,twimg.com. Viewing of images and photos was sporadically impacted. By 22:29 UTC, the original domain record for twimg.comwas restored. No Twitter user information was affected by this incident.
[UPDATE, 8/28/13: Post updated to reflect that the issue was with our DNS registrar, not our DNS provider.]
It has yet to respond to the changes to contact information on the Twitter.com record.
Update 2: Melbourne IT is now providing a statement, which we’ve pasted in below (h/t Matthew Keys)
The credentials of a Melbourne IT reseller (username and password) were used to access a reseller account on Melbourne IT’s systems.
The DNS records of several domain names on that reseller account were changed – including nytimes.com.
Once Melbourne IT was notified, we:
– changed the affected DNS records back to their previous values
– locked the affected records from any further changes at the .com domain name registry
– changed the reseller credentials so no further changes can be made
We are currently reviewing our logs to see if we can obtain information on the identity of the party that has used the reseller credentials, and we will share this information with the reseller and any relevant law enforcement bodies.
We will also review additional layers of security that we can add to our reseller accounts.
For mission critical names we recommend that domain name owners take advantage of additional registry lock features available from domain name registries including .com – some of the domain names targeted on the reseller account had these lock features active and were thus not affected.